People who have incredible competence in a wide range of fields are rare, and it can appear deceptively simple when they present their work. [Chris Gerlinksy]’s talk on breaking the encryption used on satellite and cable pay TV set-top boxes was like that. (Download the slides, as PDF.) The end result of his work is that he gets to watch anything on pay TV, but getting to watch free wrestling matches is hardly the point of an epic hack like this.
The talk spans hardware reverse engineering of the set-top box itself, chip decapping, visual ROM recovery, software reverse analysis, chip glitching, creation of custom glitching hardware, several levels of crypto, and a lot of very educated guessing. Along the way, you’ll learn everything there is to know about how broadcast streams are encrypted and delivered. Watch this talk now.
Some of the coolest bits:
- Reading out the masked ROM from looking at it with a microscope never fails to amaze us.
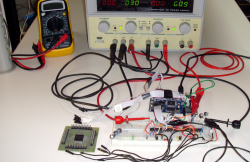
- A custom chip-glitcher rig was built, and is shown in a few iterations, finally ending up in a “fancy” project box. But it’s the kind of thing you could build at home: a microcontroller controlling a switch on a breadboard.
- The encoder chip stores its memory in RAM: [Chris] uses a beautiful home-brew method of desoldering the power pins, connecting them up to a battery, and desoldering the chip from the board for further analysis.
- The chip runs entirely in RAM, forcing [Chris] to re-glitch the chip and insert his payload code every time it resets. And it resets a lot, because the designers added reset vectors between the bytes of the desired keys. Very sneaky.
- All of this was done by sacrificing only one truckload of set-top boxes.
Our jaw dropped repeatedly during this presentation. Go watch it now.

















While I understand this is more like hacking mechanical locks than anything else I can’t help be feeling this pursuit is a terrible waste of talent that could be doing so much more.
U wot mate? This is the creme de la creme of multidisciplinary hacking/engineering.
Who knows, maybe by doing such feats of hacking he will stumble upon an idea that will change the world? Or maybe this hack will inspire people to do something beneficial for mankind? Doing nothing is true waste of time, resources and air…
My remark hardly implied he would be better doing nothing, however these sorts of cracks are largely a zero-sum endeavor even if there is no criminal intent. They are clever attacks on a challenging problem but they represent little real advancement in the applicable technologies.
But a pretty good entry on the resume of anyone looking for work in reverse engineering, even if it was pretty old tech.
^^ this.
At the end, someone in the audience asked what [Chris] did for his day job. “Hardware reverse engineering.” No joke!
Other winner questions: “How long did you spend on this project?” Two weeks at a time, until he burned out, over two years. “Where did you get all that equipment?” A lot of it was expensed to clients when he did previous work for them.
In short, this guy doesn’t just seem professional…
I’m afraid a decent person doesn’t want to work in the job offers you get from this, which probably will all from disreputable 3 letter organizations.
Advancement in defeating the techniques he uses.
you miss the main point. Those people don’t do to be “usefull to mankind” or whatever other noble target, they do because they get fun doing what they do. Why people climb up Everest? because it is there!
Yeah, I did some exercise the other day, it was a terrible waste of using my body when I could have been hiking or swimming or doing something fun.
I saw some mountain climbers practicing on a fairly short indoor wall once, what a waste of ability, they could have been in an exhilarating position on an open rock face!
I even heard professional baseball players play games in the off season, what a waste.
What this person is engaging in is essentially a criminal activity – the things you are mentioning are not. Sugar coating breaking pay TV encryption by making the claim that doing is some sort of intellectual exercise simply does not wash.
You weasled out of “criminal activity” with “essentially”, but reverse engineering is none of the above.
Why do you think that taking things apart to see how they work is wrong? Is it possible that you’re confusing the theft of pay-TV revenues (which would be a crime) with the act of breaking their encryption?
Breaking encryption of this sort is a crime in and of itself under the letter of the law, just like illegal entry is a crime even if nothing is stolen. In that regard it is qualitatively different than taking apart a TV to see how it works. It is an action taken to overcome a security measure designed to keep others out. If anyone is trying to weasel around the truth by constructing ethically questionable justifications here it is those that are arguing as you are.
Yes this is an impressive example of intellectual legerdemain, but as I originally remarked, it is also a monumental waste of time and talent. However in the end that is my opinion and you are free to hold your own in this matter, but do not try and whitewash it with a flimsy defence based on curiosity.
It isn’t illegal in every country. Do not confuse the US with the world.
And what countries would that be? At any rate even if there are some it hardly justifies an attack of this sort, it only shifts it from a legal to an ethical question.
DV82XL, you do realize reverse engineering is often done legally?
* for educational purpouses (the above)
* for fixing things a company still needs which are no longer supported
* to inspect and gather evidence if a company is using unlicensed technology (perhaps a company suspects a competitor is using their technology without license, or perhaps an open source community is inspecting if a device is using say GPL code without providing potential improvements in the code back to the community, …)
* …
Your view of “the” law seems a bit oversimplified
I have a really low tolerance for hypocrisy. Yes some laws are stupid, and yes the whole edifice of intellectual property law is a mess by anyone’s standard and needs to be overhauled in the worse way. And indeed sometimes civil disobedience is both an ethically justifiable way to protest bad law, but call it what it is: Breaking this type of encryption is a crime even if its intent isn’t to watch free porn, just like breaking into a locked space is criminal entrance and trespass.
Furthermore I see no greater objective here beyond the self-aggrandizement of the person doing it. Yes it is an impressive hack, taking out a major chunk of the North American grid would be an impressive hack, or killing a large block of ATC, or for that matter compromising the election in someone else’s country, but I bet none of you would be ready to make heroes out of those.
A seller sells an object covered locked by a thin layer of metal to a customer. The customer drills a hole through the thin layer of metal. Is that a crime?
A block of metal consists of a smaller block of metal covered by a thin layer of the same metal. A seller sells a block of metal to a customer. The customer drills a hole through the block. Did he just satisfy your literal definition of breaking into a locked space?
Oh ok, the seller of the block of metal does not care what you do with the block of metal. Who cares what the seller of an object cares about how you use it? The specification of (il)legality should be in the law, not in our estimates of what a specific seller likes or dislikes.
I keep making the same mistakes over and over again… my bull**** filter is so finetuned, I ignore parts of comments which are besides the point… but re-reading this paragraph it seems to be exactly your point:
“Furthermore I see no greater objective here beyond the self-aggrandizement of the person doing it. Yes it is an impressive hack, taking out a major chunk of the North American grid would be an impressive hack, or killing a large block of ATC, or for that matter compromising the election in someone else’s country, but I bet none of you would be ready to make heroes out of those.”
You are making subtle references to supposedly russianoid activities…
Are you just hating the guy because of his last name?
No, definitely not. I am making the point that one cannot excuse ethically, morally or legally wrong activities because one is impressed by the complexity, or cleverness of the act itself or one doesn’t care for the victim. This hack is NOT civil disobedience with a political objective, and no one should try to frame it as one.
I never framed Chris’ talk as civil disobedience, but as education (research): his talk basically takes the form of a research paper if you notice (quick abstract, introduction, methods, results, conclusions)
Did you read the post about perfectly legal (not even civil disobedience yet) reverse engineering situations?
Framing it as research is still a flimsy attempt at justification. This is an unethical pursuit regardless of its legality where the only substantive practical applications are blatantly against the law in almost all circumstances. Celebrating this sort of thing is a clear example of the sort of moral blindness that those of us in the sciences and technologies are too often guilty of.
How is describing in a general way how to circumvent protection mechanisms not educational? How is drawing conclusions of what could have been done better to protect the system not educational? Do you propose censoring entries like NOP slides from Wikipedia as well? Education is a valid application of reverse engineering.
Does only the state sponsored intelligence community have the moral right to reverse engineer? Would you argue only the state has the moral right to reverse engineer say malware? Your antivirus software must be written by the state? Nobody would be allowed to reverse engineer this antivirus software written by the state?
Check this out:
https://www.youtube.com/watch?v=qOwyZGCZ4gs
have a nice day
Don’t try and reframe this – we are talking about one individual’s act here and you are tabling an argument along the the lines that because deadly force is justified in some instances we should accept an act of outright murder because it was carried out in a very impressive way. No. THIS act of reverse engineering is without moral or ethical justification, you cannot claim otherwise by asserting that there are other circumstances where it might be.
Please don’t get me wrong: I appreciate many of your comments in other threads. I value those contributions and I hope to see you continue bringing them.
Humans maintain individual belief systems. Humans learn from each other by means of communication. Communication takes multiple forms: statements and questions.
Statement clauses are like pull requests, inviting the other party to update their belief system (and beliefs about what others claim to believe are also beliefs).
Example: if one claims “I saw a ghost yesterday.” the other party might update its belief system so that the other really believes the first saw a ghost, or perhaps the “only” update is the nested belief that the first has claimed to have seen a ghost the day before.
Question clauses probe the belief system of others, so as to update one’s own beliefs (again beliefs modeling the belief system of another are also beliefs):
Example: if one asks “Was the ghost transparent?” and the other responds “Yes, opacity was 50%.”, then the first could choose to blindly believe and add the content of the claim, or “merely” update the belief system with a more complicated nested claim attributing it to the other.
Whereas statements from different belief systems tend to quickly collide, questions from different belief systems tend to defuse and nuance.
If we limit to sentences of clause simplex (single clauses), then accusations must be statements, and hence questions can not be accusations.
In general though I must admit sentences of clause complex can hide statements by being attached to questions: “What were you thinking when you stole the apple?” does contain the accusation of stealing an apple (which may be false), because it is a clause complex.
Anyway, if you look up the thread, you will see that I mostly ask questions about your belief system, most of them direct (with a question mark) and a couple of them indirect (explicitly using the word “seem”). And if you look at your posts, they mostly contain statements. Some of these statements claim things about me.
I hereby request a quote where I supposedly argue that the impressiveness of the hack justifies any immoral consequences of it, as you seem to be under the persistent impression that my argument revolves around impressiveness.
Because if I look up in the thread, not only did I not use it as an argument, I did not even refer to any impressiveness.
Are you amalgamating multiple personas on hackaday into one? We are a diverse open-minded bunch. It won’t work like that.
From Wikipedia: “A straw man is a common form of argument and is an informal fallacy based on giving the impression of refuting an opponent’s argument, while actually refuting an argument that was not advanced by that opponent.”
Please don’t put words in my mouth. You are literarily shoving your junk in my oral orifice. Just don’t: regardless of how many layers of rubber you wrap it in or any flavours these may carry, it makes me gag… capisce? Not only is it bad argumentation, it is bad netiquette as well…
In response to your last comment: no, I do not believe because an act may be justified in one setting, that it is justified in all settings. For example even though this act of reverse engineering for educational purpouses is legal, it would have been illegal (even for educational purpouses) to open and decap chips from the set-top box borrowed from the neighbours without the informed consent of these neighbours who are the rightfull owners of the set-top box.
First of all clean-room reverse engineering is legal, at least in the EU, but to my knowledge even in the US, too. Second, your arguments, while true, concerning the letter of the law, are essentially bullshit in regard to the spirit of the law.
You are talking about breaking and entering in the physical sense. But let me know two things. What happens if you unlock a lock, without entering beyond that point. Is that still unlawful, hmm and just a second point. What if you pay someone to unlock your car or house, because you lost your keys. Technically that person is breaking the law, too. Absolutism is narrow minded and has never led to anything good. Just take a look at the current POTUS.
“and it can appear deceptively simple when they present their work”
Heh. I guess it CAN look deceptively simple, but at the point where you strip ICs bare to look at them with microscope to see what they actually do it’s anything but simple looking to me. I mean, yes, I know some ASIC design, and everything is really very simple when divided into small enough pieces, but all that, whoa :-D Got to give credit for doing all that just for the challenge of doing it.
>Other winner questions: “How long did you spend on this project?” Two weeks at a time, until he burned out, over two years. >”Where did you get all that equipment?” A lot of it was expensed to clients when he did previous work for them.
I’ve been paid in tools as well, as part of the cost of doing business. I need X thing to do this job, I don’t own one. Do you want it at completion? No. Ok. Thanks.
The video was very interesting, I was impressed, and I learned a few things from it. I dunno who is worse, the not a hack crowd or your time would be better off spent making something I see as valuable crowd.
This was awesome. Clearly the movie Paycheck was a documentary about this guy.
Only thing I did not like about his talk was that it was so cramped full with specific details and acronyms – while being about a super interesting topic, presented by a very capable and well spoken person. But he really used his timeframe well :-) Kudos!
Some years ago, a Canadian figured out how to crack DirecTV. Instead of going at it via the access cards, he figured out how to directly crack the box so it didn’t need a card, or to communicate back to DirecTV. He had it fixed to always decrypt everything.
Couldn’t be touched on it for a while because of a loophole in Canada’s laws. If something could not be sold in Canada (such as DirecTV service) it was deemed to have zero value. The other part was that if you took something considered to have zero value, it wasn’t considered theft.
I’d like to know how much DirecTV money crossed Canadian political palms to plug that hole and get the guy arrested.
What really did the guy in was he wasn’t being discreet about his hack. He could’ve kept it on the down low and passed the info to a bunch of other people instead of publicizing it and wanting to make a lot of money from it.
Isn’t this the mother of all hacks, given the complexity!
I half expected to see a remote wired to a couple binary counters and some 555s scrolling through all possible unlock codes :D
WDC6502 core :)
Ooooh he’s good! He made it sound easy, but that’s some skillz. “Most of the work was completed over aboot a two year period”. Nice work fella.
Question from audience “What do you do for a living besides reverse engineering?” “..Reverse engineering”. lol
“..it can appear deceptively simple when they present their work. [Chris Gerlinksy]’s talk on breaking the encryption used on satellite and cable pay TV set-top boxes was like that.”
Wat.. this is likely the most complicated documented hack of something that I’ve ever seen. It’s insane how much he put into this. I don’t want to know what gets paid and who he works for if he is doing that sort of thing at his day job.
If his cracking/reverse engineering is at the cost of lost profits for Direct TV (now AT&T), then I support him 100%. Those bastards need to be brought down a few notches.
Direct TV…are you listening? YOU SUCK!
Emass, not buying their products would work faster, and be more ethical. Theft of service sends the wrong message, and it’s not one of disapproval.
For those who think he broke the law: He did NOTHING illegal. The DMCA in the USA specifies unauthorized access to a computer system, which is what the DTV lawsuits and prosecutions were based on. Defeating their security devices is NOT illegal, until you use it for access to the encrypted signal(their computer system). If you own the hardware, it is yours to play with. You might want to rethink this position, as it is flawed logic!