Our own [Brian Benchoff] asked this same question just six months ago in a similar headline. At that time, the answer was no. Or kind of no. Some exploits existed but with some preconditions that limited the impact of the bugs found in Intel Management Engine (IME). But 2017 is an unforgiving year for the blue teams, as lot of serious bugs have been found throughout the year in virtually every fields of computing. Researchers from Positive Technologies report that they found a flaw that allows them to execute unsigned code on computers running the IME. The cherry on top of the cake is that they are able to do it via a USB port acting as a JTAG port. Does this mean the zombie apocalypse is coming?
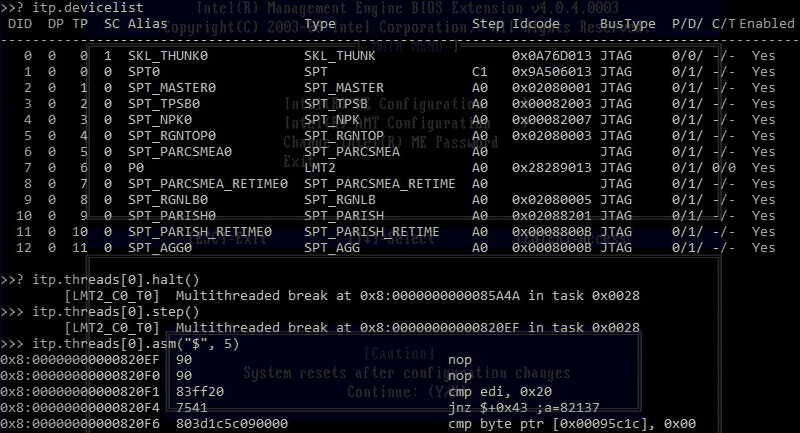
Before the Skylake CPU line, released in 2015, the JTAG interface was only accessible by connecting a special device to the ITP-XDP port found on the motherboard, inside a computer’s chassis. Starting with the Skylake CPU, Intel replaced the ITP-XDP interface and allowed developers and engineers to access the debugging utility via common USB 3.0 ports, accessible from the device’s exterior, through a new a new technology called Direct Connect Interface (DCI). Basically the DCI provides access to CPU/PCH JTAG via USB 3.0. So the researchers manage to debug the IME processor itself via USB DCI, which is pretty awesome, but USB DCI is turned off by default, like one of the researchers states, which is pretty good news for the ordinary user. So don’t worry too much just yet.
We recommend [Benchoff]’s excellent article about IME in case you have questions about what it is. In a nutshell, IME is a completely independent processor that can control networking and hardware as long as the power cable is connected, even if the computer is turned off. Although independent, it is baked into the main processor chip (Intel inside Intel inside?) so there is no way to remove it, but there is a way to disable it, at least in some processors. Since IME is executing code on a different CPU, apparently running MINIX, its network operations bypass any OS installed and are completely invisible to the host, among other cool ‘features’. This is so cool that the EFF actually accused IME of being a backdoor.
In other news, Betteridge’s Law of Headlines seems to remain unbroken.















What if Intel fsckd ME on purpose? Today everyone has their chips, everyone needs them, everyone wants to be secure. But for Intel this is not enough to make enough profit. Oh, no there is a security bug in Intel chips! We need new secure CPUs from… Intel.
or jump on the ARM bandwagon ;)
With the TrustZone in it?
RISC-V.
But which one? Ready for an ARM-wrestling match?
Might have to start using IBM’s Power chip. The Amiga folks may just get the last laugh.
They’ve been waiting 30 years, but.
Yah it could be a chance for IBM and other RISC cpu manufactures to take back the server space market.
A potential back door on the level of ME should be of grave concern to enterprise users esp banks because they’re high profile targets.
IBM’s had a BMC for years that acts much the same way the IME works. I’d bet that that any Power-based boards would have it built in.
Amiga
* OS mostly ran from ROM
* dynamic resolution at the same time on the same screen video card (early GPU)
I always suspected it was Alien technology, as mere humans had no idea how to use the new tech at the time.
As for Intel’s ME, I will give 1337 Internet points to the first person to boot Linux on the sand-boxed processor with a shared DMA window.
IBM. The same company that was behind AIX with the option to rsh that allowed it to bypass the root password?
https://www.extremetech.com/computing/259036-early-qualcomm-server-cpu-benchmarks-mean-big-trouble-intel
I’d rather have Intel spy me, than clicking the “thousand spying scripts” tech site.
I seriously doubt that you could find a hardware engineer willing to cripple their own design on purpose. There are enough problems by accident.
Otoh if $shadowy_government_institution were to come to Intel and say, “you’re gonna put this code into your ME for us, or else…” Then I doubt that they would have much of a choice if they wanted to keep their company running. All it would take to put Intel under is losing all their government contracts, some nasty tax audits, and having their shipments get lost in customs.
“The natural progress of things is for liberty to yield, & government to gain ground. As yet our spirits are free.” -Jefferson, 1788
Yes and as a counter to all that let’s keep in mind that some of Intel’s customers are likewise other sovereign states, so saying “the government made me do it” doesn’t works so well.
A check with a sufficient number of zeros, or appeal to nationalism would probably work better than a gun to their head.
There are enough people with good intentions to prevent the next 9/11, 7/7 or truck attack that they don’t need to make threats.
I bet you could find a manager who would keep searching until they find somebody to do it though…
One partial fix would be avoid using the built in networking on Intel MBs and use a separate card and maybe go as far as remove the RJ45 connectors from the motherboard or filling them with epoxy if you’re really paranoid.
Though this would not fix the gaping hole putting diagnostics on the USB port caused.
That doesn’t solve it though, the ME doesn’t need to directly access the hardware, it can look in the memory of your operating system. It’s potentially the world’s best rootkit.
The situation is that you have your PC running a secure OS and to make sure it doesn’t do anything while you’re away, you turn it off for the weekend. Come Monday morning your secret project has somehow leaked to the press….
That’s what ME can do for you, hopefully only when the onboard ethernet plug is being used. A bug (or feature) in ME will allow a hacker to remotely turn on the PC, grab all the data and then turn it off again. Do you KNOW your data hasn’t been stolen if on Monday it is NOT plastered across the internet?
Patriot act buddy. They are required by “law” to comply If gov agen. demand they do It
Has the IME full Harddisk access? Maybe if you use an filesystem which isn’t supported by “MiniX” or the IME this could be a way to make your data “safe”?
All it takes is a kernel entry exploit, a filesystem driver, a patch of memory allocated as code and a good old JMP payload into the new driver… the kernel would be none the wiser!
For as long as there is raw hardware access from the ME controller, then all that is needed is to move some bits and wind some stacks to convert variable tables (C
Structkeyword) into human abstract form: i.e. a filesystem.You have a sector that point to one or more
root-table(s)that point to bothsub-table(s)andarbitrary data window and pointer table(s)… Thosesub-table(s)point to more of the both above (not toroot tablesBTW)It is up to the hacker to extract the MBR/GPT area and to then find the start of the
root table(s)of each partition and then to extract those tables for comparison against known filesystems… From there, the hacker can either reuse known code (virus scanners can compare against) or design their own… especially if they want to go light weight and only extract the arbitrary data.i.e. there is no point in having write support and journaling in an ext4 filesystem when their Trojan is only leaking data or performing DDoS attacks.
No, with full-access to the hardware, the bad guys can exfiltrate the raw data and then analyse what they have with whatever tools they like.
Alert! Two new flavors of Minix have been discovered!
http://www.gazetadopovo.com.br/bomgourmet/wp-content/uploads/2014/10/pullman3.jpg
Mmmmm!
I just hope there aren’t any bugs in them!
B^)
Extra vitamins.
“This is so cool that the EFF actually accused IME of being a backdoor.”
Something about there being little difference between a tool and a weapon, just in how it’s applied.
Or as the internet is fond of saying: Anything is a dildo if you’re brave enough.
There are likely many of us whom have kept our beady eye out on the development of the Intel Management Engine and have already come across all the information here.
It is nice to see someone has taken the time to collate all the information together so everyone can see the extent of the whole Intel fiasco around their Admin’s god-send tool known as IME or Intel Management Engine.
Our only hope as a community of hackers, creates and modifiers is that the Management Engine cores can be used in the future as another UserSpace-execution core for scenarios such as synchronizing, downloading, uploading or low-priority processing during times when a machine such as a laptop is “Off” for carriage or the home PC is left to save energy on a non-critical task.
Such a re-purpose of the micro-controller would make it from a security nightmare into good use.
My thoughts are to use the micro-controller as a virtual machine “host” and reserve the CPU cores for guest-per-core virtual machines, or uploading that Youtube video whilst you’re at work and don’t want to leave the home PC running full tilt on your electricity bill… Sure, there are many more uses, that being subjective, is up to the rest of the world to decide collectively and individually.
P.s. @Admin(s): Can you e-mail the last post under my internet-name?
And, can you keep it moderated… It has been tainted enough by some idiot! Better safe than sorry (TM)
I’ll only use the following once, here:
The Real Unferium
If you could keep an up to date OS on it that has no back doors it could be very useful indeed.
Supposedly these are a Sparc core so I wonder could it run a cut down version of BSD which could make it a very tool.
The older ones I think are ARC based this may still be true with some low end devices as consumer devices don’t need as much remote management functionality it any at a all.
“Although independent, it is baked into the main processor chip (Intel inside Intel inside?) so there is no way to remove it”
I thought the ME was in the PCH?
Publisher’s Clearing House?
B^)
We are all winners!
Platform Control Hub (Official name),
Peripheral Controller Host (Joe Bloggs terms),
Southbridge (Old Term)
Thanks!
B^)
Possession of china?
Ordinary users may not need to worry but enterprise level users should be worried over this as they are often targeted by large hacker groups, rival corporations and even nation state entities.
Ordinary users only need to be worried about their machines being used as minions for DDoS attacks.
Laptop users mostly (lots of businesses). Enterprise has (supposedly) experienced people who already know what it is, how to use it, and how to keep things under control. Heck even Google is working on the issue.
Still security through obscurity which only works when the hardware is actually obscure enough that only few people can get their hands on it.
ME pretty much everyone has one to mess with so far more people and thus brain power will be at work breaking it.
True though I suspect ME only has drivers for the built in NIC but most people use that built in NIC so if a malware ever is made to take advantage of it could be the worst DDOS worm infection in history that will make the IOT bot fiasco look minor.
Plz write article on installing minix on old pcs OR accessing minix on new pcs
Years ago I downloaded Minix (3.something?) from http://www.minix3.org/ and installed it on a partition of an old PC.
But as I am not a C programmer, there was little I could do with it.
moving to parallela procesors
For some operations they do out perform X86 by as much as two orders of power when it comes to operations per watt.
Though the keyword here is some operations but that said X86 generally has mediocre performance per watt and is more of a brute force approach to getting things done which is why I think it’s largely been a failure in the embedded market.
The day that someone exploits the IME I will bring down my core2 quad from the attic and laaugh as the world burns :)
BANDWAGON
Somebody (maybe crowdsourced) needs to start a project to monitor and identify the traffic coming out of the typical home computer setup by vampire tapping it before the router. It’d be nice to know what the ME (among many other things – windows for example) are doing when we aren’t watching or when the power is supposedly off. Being able to identify the packet streams would go along way to trusting these damn things again.