Opening up things, see how they work, and make them do what you want are just the basic needs of the average hacker. In some cases, a screwdriver and multimeter will do the job, but in other cases a binary blob of random software is all we have to work with. Trying to understand an unknown binary executable is an exciting way to discover a system’s internal functionality.
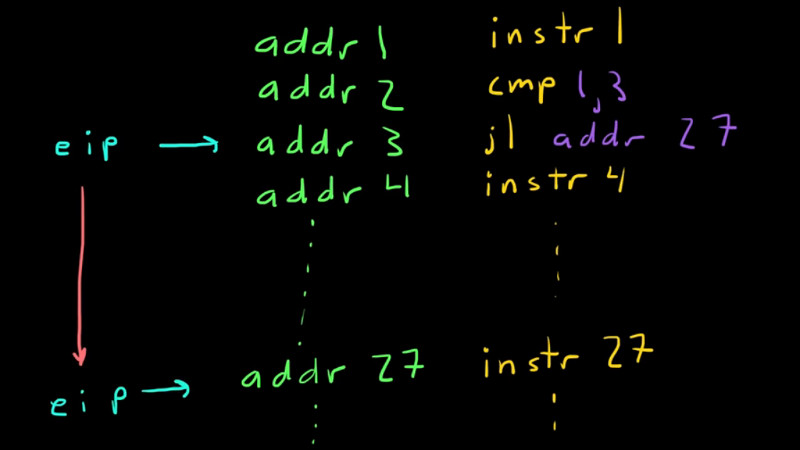
While the basic principles of software reverse engineering are universal across most platforms, the details can naturally vary for different architectures. In the case of the x86 architecture, [Leonora Tindall] felt that most tutorials on the subject focus mostly on 32-bit and not so much on the 64-bit specifics. Determined to change that, she ended up with an extensive introduction tutorial for reverse engineering x86_64 binaries starting at the very basics, then gradually moving forward using crackme examples. Covering simple string analysis and digging through disassembled binaries to circumvent fictional security, the tutorial later introduces the Radare2 framework.
All example source code is provided in the accompanying GitHub repository, although it is advised to avoid looking at them to keep it more interesting and challenging. And in case you are looking for more challenges later on, or generally prefer a closer connection to the hardware, these MSP430 based capture the flag online challenges might be worth to look at next.















Ah! Finally an intro that doesn’t depend on proprietary software.
heh. I presume you are referring to a rather well known disassembly/reverse engineering tool.
There are others which are just as good or better depending on the target architecture and O/S. Immunity debugger is a good one for Windows users.
That tool is like crack to me.
Don’t bring it into my jurisdiction then :)
https://www.youtube.com/watch?v=EOJNs5YPR4g
How very ‘original’ of you Mr. Davidson…
Again hackaday has crashed a website.
Perhaps they should have their “Computer Driving License” suspended :)
Crashing websites is a federal offense over here :)
Crashing automobiles which is far more dangerous, is usually just a local or state matter.
he mixes up bytes and bits a lot in the text, otherwise interesting read.
example : “Then we zero out all but the last 8 bytes of ecx and compare eax to ecx.”
Oh, whoops! That’s a rather egregious problem, I’ll try to fix it right away. Thanks for bringing it to my attention.
Sounds like Lenas reversing tuts
Lena151 tutorials
Read this, including comment thread (I’m not in total agreement with all, but worth reading):
https://reversewithme.blogspot.co.id/2012/10/why-lena151-tutorials-wont-teach-you.html
Has anyone taken a look at the source? Is it safe to run or do I need to setup a vm to run it safely?
Is what safe to run? The tutorial provides only source code; you have to compile the binaries yourself. You can look at the source if you want, though it would spoil the challenge somewhat.
It’s not a ‘challange’ if I take a look at it. Therefore I don’t want – yet I also don’t want to compile & execute it unseen respectively unconfirmed.