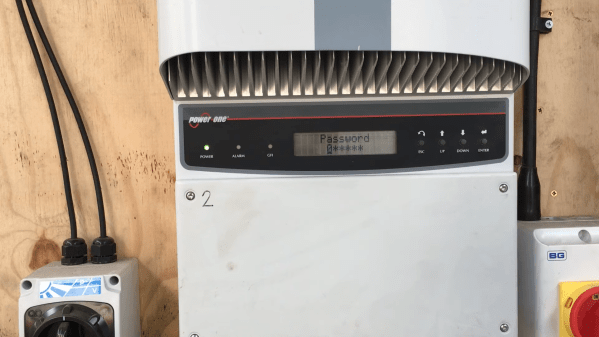
It’s a fact of life that electronic devices become obsolete after a few years. Sometimes this is because technology has moved on, but it can also happen that a perfectly functional device becomes near-useless simply because the original manufacturer no longer supports it. When [Buy It Fix It] found a pair of second-hand Power-One Aurora solar inverters, he ran into an issue for which he needed access to the service menu, which happened to be password-protected. The original manufacturer had ceased to exist, and the current owner of the brand name was unable to help, so [Buy It Fix It] had to resort to reverse engineering to find the password.
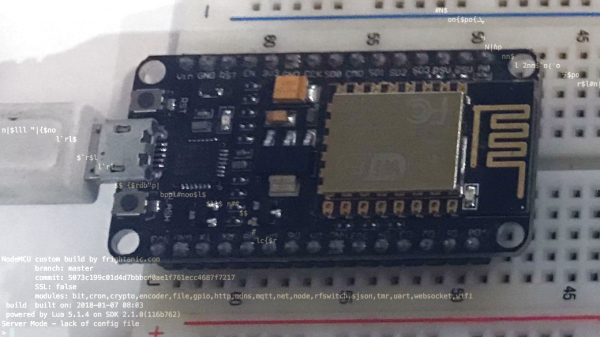
Thanks to the Wayback Machine over at the Internet Archive, [Buy It Fix It] was able to download the PC software bundle that originally came with the inverters. But in order to access all features, a password was required that could only be obtained by registering the unit with the manufacturer. That wasn’t going to happen, so [Buy It Fix It] fired up dnSpy, a decompiler and debugger for .NET programs. After a bit of searching he found the section that checked the password, and by simply copying that section into a new program he was able to make his own key generator.
With the service password now available, [Buy It Fix It] was able to set the inverter to the correct voltage setting and hook it up to his solar panels. Interestingly, the program code also had references to “PONG”, “Tetris” and “tiramisu” at various places; these turned out to be Easter eggs in the code, containing simple versions of those two games as well as a photo of the Italian dessert.
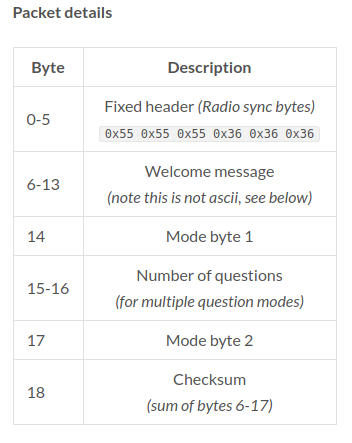
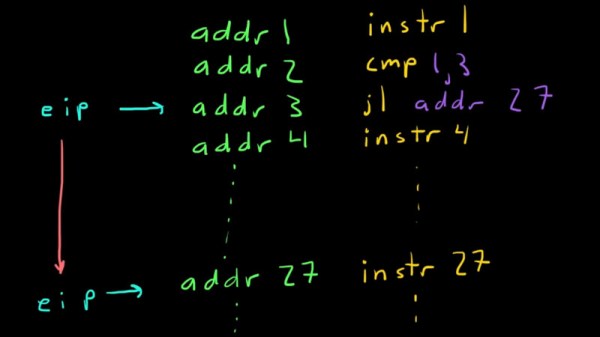
Inside the software archive was also another program that enabled the programming of low-level functions within the inverter, things that few users would ever need to touch. This program was not written in .NET but in C or something similar, so it required the use of x32dbg to look at the machine code. Again, this program was password-protected, but the master password was simply stored as the unencrypted string “91951” — the last five digits of the manufacturer’s old phone number.
The inverter was not actually working when [Buy It Fix It] first got it, and his repair video (also embedded below) is also well worth watching if you’re into power electronics repair. Hacking solar inverters to enable more features is often possible, but of course it’s much easier if the entire design is open source.
Continue reading “Decompiling Software To Fix An Old Solar Inverter” →