We once knew a guy who used to tell us that the first ten times he flew in an airplane, he jumped out of it. It was his eleventh flight before he walked off the plane. [Mathias Lasser] has a similar story. Despite being one of the pair who decoded the iCE40 bitstream format a few years ago, he admits in his 34C3 talk that he never learned how to use FPGAs. His talk covers how he reverse engineered the iCE40 and the Xilinx 7 series devices.
If you are used to FPGAs in terms of Verilog and VHDL, [Mathias] will show you a whole new view of rows, columns, and tiles. Even if you don’t ever plan to work at that level, sometimes understanding hardware at the low level will inspire some insights that are harder to get at the abstraction level.
In theory, the reverse engineering ought not be that hard. The device has some amount of resources and the bitstream identifies how those resources connect together and maybe program some lookup tables. In practice, though, it is difficult because there is virtually no documentation, including details about the resources you need to know at that level.
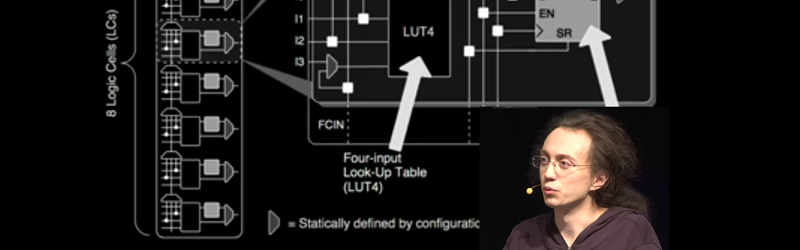
For example, in the video, you can see Lattice’s diagram for a logic cell. There are several options to do things like bypass the flip flop, set the look-up table, and so on. There’s any number of options available to set that configuration and that doesn’t even address how to connect the inputs and outputs to the routing resources.
Of course, you know he managed the iCE40 decoding since he and [Clifford Wolf] did the work behind the open source Lattice toolchain. We even used that toolchain in several of our FPGA tutorials.















Unfortunately he lost his presentation slides right before the presentation so the actual content of the presentation in the video is not that much.
Let see whether lasser.io will be available sometime with more information, as promised in the video.
For me the most fascinating part of this talk is [Mathias]’s motivation. He’s clearly in the “Why did you want to climb this mountain?” territory ([George Mallory]: “Because it’s there”). Maybe even a step further, like “and I didn’t feel like waiting in line for the cable car”.
That’s the hacker spirit!
youtube referral revenue my guess?
LOL.
Funny languages?
The link (https://media.ccc.de/c/34c3/34c3-9237-reverse_engineering_fpgas) from the media.ccc.de youtube page, currently says 404 page not found…
https://media.ccc.de/v/34c3-9237-reverse_engineering_fpgas
This one is okay, took half a second from the video-list located here : https://media.ccc.de/c/34c3
https://media.ccc.de/v/34c3-9237-reverse_engineering_fpgas this works fine for me (note the /v/ vs the /c/ in the URL).
The embedded video is gone from the article. There are supposedly eight (now nine) comments, but only two are displayed. Lasser.io is empty. Strange. Maybe in the end he did not accidentally loose his slides after all.
someone have any ideas about where to get the slides?
The website lasser.io was never available, at least never when i was looking for it. Also the missing slides were not published. … Disappointing :/