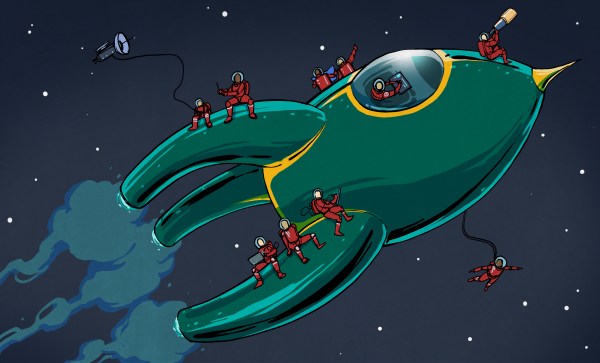
At this year’s Chaos Communication Congress, we caught up with [muzy] and [overflo], who were there with a badge and soldering project they designed to teach young folks how to solder and program. Blinkenrocket is a basically a 64-LED matrix display and just enough support hardware to store and display animations, and judging by the number of blinking rockets we saw around the necks of attendees, it was a success.
Their talk at 34C3 mostly concerns the production details, design refinements, and the pitfalls of producing thousands of a thing. If you’re thinking of building a hardware kit or badge on this scale, you should really check it out and crib some of their production optimization tricks.
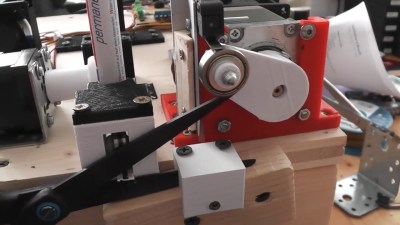 For instance, instead of labelling the parts “C2” or “R: 220 Ohms”, they used a simple color-coding scheme. This not only makes it easier for kids to assemble, but it also means that they didn’t have to stick 1,000 part labels on every component. Coupled with [overflo]’s Zerhacker, SMD parts in strips were cut to the right length and color-coded in one step, done by machine.
For instance, instead of labelling the parts “C2” or “R: 220 Ohms”, they used a simple color-coding scheme. This not only makes it easier for kids to assemble, but it also means that they didn’t have to stick 1,000 part labels on every component. Coupled with [overflo]’s Zerhacker, SMD parts in strips were cut to the right length and color-coded in one step, done by machine.
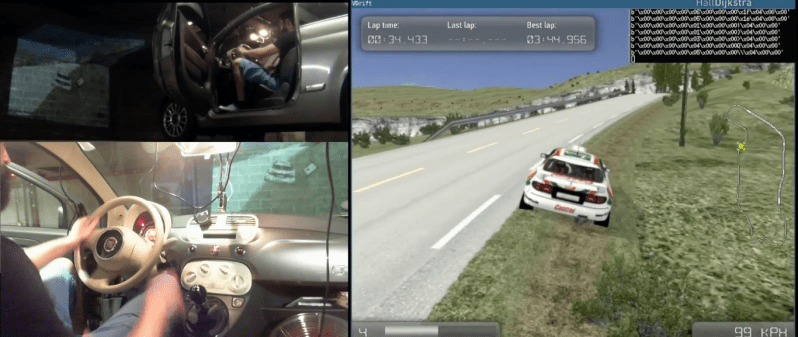
The coolest feature of the Blinkenrocket itself is the audio programming interface. It’s like in the bad old days of software stored on cassette tapes, but it’s a phenomenal interface for getting a simple animation out of a web app and straight into a piece of minimal hardware — just plug it into a laptop or cell phone’s audio out and press “play” in the browser. The original design tried to encode the data in the pulse-length of square waves, but this turned out to be very hardware dependent. The final design used frequency-shift keying. What’s old is new again.
Everything you could want to know about the design, its code, and even the website itself are up on the project’s GitHub page, so go check it out. If you’d like to arrange a Blinkenrocket workshop yourself, shoot [muzy] or [overflo] an e-mail. Full disclosure: [overflo] gave us a kit, the “hard-mode” SMD one with 0805 1206 parts, and it was fun to assemble and program.