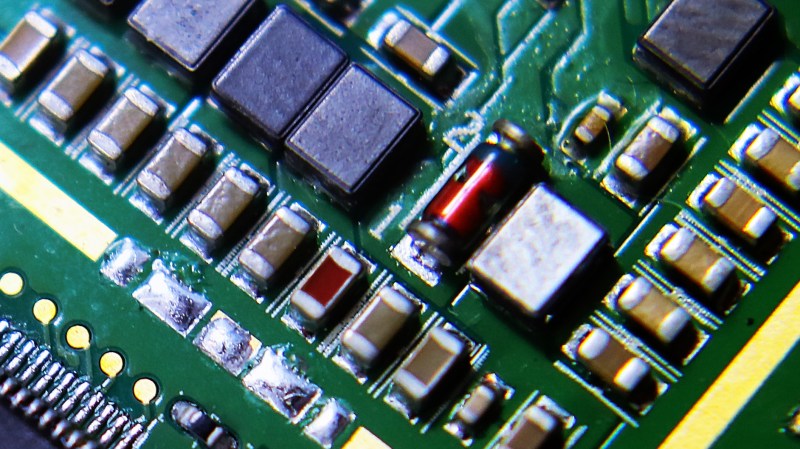
This morning Bloomberg is reporting a bombshell for hardware security. Companies like Amazon and Apple have found a malicious chip on their server motherboards. These are not counterfeit chips. They are not part of the motherboard design. These were added by the factory at the time of manufacture. The chip was placed among other signal conditioning components and is incredibly hard to spot as the nature of these motherboards includes hundreds of minuscule components.
Though Amazon and Apple have denied it, according to Bloomberg, a private security contractor in Canada found the hidden chip on server motherboards. Elemental Technologies, acquired by Amazon in 2015 for its video and graphics processing hardware, subcontracted Supermicro (Super Micro Computer, Inc.) to manufacture their server motherboards in China. It is unknown how many of the company’s products have this type of malicious hardware in them, equipment from Elemental Technologies has been supplied to the likes of government contractors as well as major banks and even reportedly used in the CIA’s drone operations.
How the Hack Works
The attacks work with the small chip being implanted onto the motherboard disguised as signal couplers. It is unclear how the chip gains access to the peripherals such as memory (as reported by Bloomberg) but it is possible it has something to do with accessing the bus. The chip controls some data lines on the motherboard that likely provide an attack vector for the baseboard management controller (BMC).
Hackaday spoke with Joe FitzPatrick (a well known hardware security guru who was quoted in the Bloomberg article). He finds this reported attack as a very believable approach to compromising servers. His take on the BMC is that it’s usually an ARM processor running an ancient version of Linux that has control over the major parts of the server. Any known vulnerability in the BMC would be an attack surface for the custom chip.
Data centers house thousands of individual servers that see no physical interaction from humans once installed. The BMC lets administrators control the servers remotely to reboot malfunctioning equipment among other administrative tasks. If this malicious chip can take control of the BMC, then it can provide remote access to whomever installed the chip. Reported investigations have revealed the hack in action with brief check-in communications from these chips though it’s difficult to say if they had already served their purpose or were being saved for a future date.
What Now?
Adding hardware to a design is fundamentally different than software-based hacking: it leaves physical evidence behind. Bloomberg reports on US government efforts to investigate the supply chain attached to these parts. It is worth noting though that the article doesn’t include any named sources while pointing the finger at China’s People’s Liberation Army.
The solution is not a simple one if servers with this malicious chip were already out in the field. Even if you know a motherboard has the additional component, finding it is not easy. Bloomberg also has unconfirmed reports that the next-generation of this attack places the malicious component between layers of the circuit board. If true, an x-ray would be required to spot the additional part.
A true solution for high-security applications will require specialized means of making sure that the resulting product is not altered in any way. This hack takes things to a whole new level and calls into question how we validate hardware that runs our networks.
Update: We changed the penultimate paragraph to include the word if: “…simple one if servers with…” as it has not been independently verified that servers were actually out in the field and companies have denied Bloomberg’s reporting that they were.
[Note: Image is a generic photo and not the actual hardware]















I have it on good authority that this has been implemented on counterfeit USB-serial dongles for a while.
If Windows bricks it, you can guarantee that it is for a good reason.
You guys could give CNN and MSNBC lessons in Fake News Generation.
Every one of my computers has a suspicious chip in it.
What are you trying to say here? That the prevalence of cyberattacks/suspicious hardware is so high we should just stop reporting on them? That this news is fake because it happens so often? That is some next level doublethink.
He’s probably talking about the Trusted Platform Module or Intel’s Management Engine, both of which are “roots of trust” even though they’re black boxes. I don’t trust them either.
What about maliciously trashing drives with “interesting” stuff on them to cripple folks working on certain physics and engineering problems?
Could even be done using software on the drive itself, if it detects specific patterns of searches or key words.
Of course this all assumes that those who wrote/released the malicious firmware knew what to search for and only trash the drive after its critical data had been cloned remotely using a side channel attack.
There’s a few sides to crypto.
Having a chip that relays info back to “the baddies” is of necessity going to be primitive if it has to be small, but what has got to be even harder is having enough resources to handle the equivalent of stream of consciousness flows of info from millions of computers. It also had to generate a signal which ultimately would be traceable.
At the human level just trying to make sense of all the stream of data would tie up more human resources than needed to produce the info in the first place. That means potential leaks about the existence of the operation. Every side has a Snowden.
But for an actual intending to physically harm you enemy, who has probably read Chairman Mao’s Red Book, and the Art of War, denying you access to your computers in a time of strife would be equally valuable.
The Chinese are well aware of the advantages of an enemy’s vulnerability when they do not know what is happening. No data = fog of war.
To my thinking a simple Trojan Horse chip like that which sat doing nothing until actuated by a general message would be far simpler. Probably no need to delete anything, just add a few random bits to each file address and it would be enough to cause chaos, and then revert to being passive for the next time.
The beauty of that is very few people would have a need to know, so secrecy could be maintained, there’s no back signal to be traced, and it just requires one press of a button to broadcast the kill message.
However I think the best place to put chips like that is into control devices – bring down public infrastructure like electricity, water, traffic, food distribution, communications, and if it lasts about a week (because what one can break, another can mend) and you have an enemy reduced to helplessness.
During the first Gulf War, rumor has it that the printers connected to the radar systems Sadam owned were compromised. A code sent to the printers resulted in the printers shutting down the radar systems. Might be true. Might be fluff.
Seriously what did you expect was gonna happen? Hi tech engineering and manufacturing jobs have been willfully off-shored out of the country for over 30 years now by mostly American corporations looking to cut costs by replacing expensive American employees with Cheaper foreign labor. Yay free trade and globalization!!!!
They pretty much handed over the entire Electronics Manufacturing supply chain system to China. If I were China I too would place ‘spy’ chips on to motherboards to monitor the activities of the other global powers and their corporations. I don’t blame China. I blame the Apples, Googles, Microsofts IBMs, CISCOs and the rest of them.
I blame it on the elected congressment/senators over the decades that have been making laws that make it so easy for large multinational corporations to behave like that. For the longest time we have had “the best government money can buy” and its been China and other countries writing he checks.
I blame it on the human species and their obvious mental shortcomings in how they pick out sub-groups of themselves and blame them for their common problems. You complain about how corporations dehumanize and then you demonstrate it by blaming human problems on corporations!
Story marches on.
https://www.bloomberg.com/news/articles/2018-10-09/new-evidence-of-hacked-supermicro-hardware-found-in-u-s-telecom
“apple has found a malicious chip on their server motherboards”
well that’s going to affect a lot of people
It’s a bit strange to me that China can peg their currency to the dollar for over two decades without being called out on blatant currency manipulation. But the minute they set up an exchange to purchase oil in Yuan instead of dollars…..and suddenly we have trade wars and tariffs? And tiny magic chips with four pins that somehow magically intercept a server’s operating system? Not buying it, this is manufactured consent by the the NSA and corporate elites, in direct response to the Chinese challenging the reserve currency status of the U.S. dollar.