Of the $11.7 million companies lose to cyber attacks each year, an estimated 90% begin with a phone call or a chat with support, showing that the human factor is clearly an important facet of security and that security training is seriously lacking in most companies. Between open-source intelligence (OSINT) — the data the leaks out to public sources just waiting to be collected — and social engineering — manipulating people into telling you what you want to know — there’s much about information security that nothing to do with a strong login credentials or VPNs.
There’s great training available if you know where to look. The first time I heard about WISP (Women in Security and Privacy) was last June on Twitter when they announced their first-ever DEFCON Scholarship. As one of 57 lucky participants, I had the chance to attend my first DEFCON and Black Hat, and learn about their organization.
Apart from awarding scholarships to security conferences, WISP also runs regional workshops in lockpicking, security research, cryptography, and other security-related topics. They recently hosted an OSINT and Social Engineering talk in San Francisco, where Rachel Tobac (three-time DEFCON Social Engineering CTF winner and WISP Board Member) spoke about Robert Cialdini’s principles of persuasion and their relevance in social engineering.
Cialdini is a psychologist known for his writings on how persuasion works — one of the core skills of social engineering. It is important to note that while Cialdini’s principles are being applied in the context of social engineering, they are also useful for other means of persuasion, such as bartering for a better price at an open market or convincing a child to finish their vegetables. It is recommended that they are used for legal purposes and that they result in positive consequences for targets. Let’s work through the major points from Tobac’s talk and see if we can learn a little bit about this craft.
Reciprocity
One of the most common online dating tips is to start off conversations with information about yourself. If you open up to people, most of them will likely return with information about themselves.
There’s often a sense of social obligation that comes along with this — if someone pays for your meal, you feel obligated to pay for theirs the next time you go out. Likewise, once you start offering information about yourself over the phone with a member of customer support they will most likely feel more comfortable talking about themselves, establishing rapport early on in your conversation. This is true even if it’s fake information you made up for the purpose of vishing — the over-the-phone equivalent of phishing.
Commitment & Consistency
Most people don’t like to go back on something they’ve already agreed to. Starting off your conversation with your target in a friendly and helpful tone will allow the rest of your conversation to remain at the same level of amicability. Soft questions, such as asking them about their pets or finding things you have in common, are the easiest techniques for building up consistency for the future.
If you start off small, with subtle commitments, you can eventually build your way up to convince your target to download malware or visit a suspicious website.
Social Proof
We all have a tendency to trust larger groups, especially if these groups are our close family and friends. Even a stranger associated with a group that we’re close to will make us instantly more trusting of them.
One technique often used in social engineering attacks is name dropping a relative or coworker as a means of gaining the trust of the target. In the off chance that the target starts to press for more details than you prepared, re-direction (“Oh, I think I’m getting another call on my end… what were we talking about again, by the way?”) can be a good way to avoid suspicion.
Liking
For in-person social engineering attacks, imitating the body language, cadence, and even word choice of your target can put them at ease and lead them to be more trusting of you. Subtle factors — having similarities, giving them compliments, cooperating with them towards a mutual goal — can make you more likable, and thus easier to work with. Even for vishing attacks, using slang that your target uses or speaking in a similar tone as they speak in can help you be more relatable.
Authority
Stanley Milgram was a social scientist famous for experiments about peoples’ obedience to authority figures. He showed that people were willing to obey an authority figure in a white lab coat despite the morally questionable acts they were told to perform. When you start looking into it you may be surprised the lengths that we’ll go to obey authority. People are more likely to follow what credible experts and leaders tell them to do. In a company setting, employees are likely to do as they’re told if the instructions are coming from their boss or someone above them in the hierarchy of their workplace.
Scarcity and Urgency
If you rush someone at their job, they’re probably going to be less careful and make more mistakes, which is exactly what you want as a social engineer. Setting up situations conducive to this — such as pretending to be in an airfield waiting for your airplane to take off or in a house with a crying baby — can make your target more receptive to quicky doing as you tell them to do without question. In the video below, a DEFCON social engineer uses this technique quite effectively to perform a SIM swap and lock the journalist out of their phone.
https://www.youtube.com/watch?v=bjYhmX_OUQQ
OSINT Strategies
The vast amount of time spent on a vishing or in-person social engineering attack focuses on gather information ahead of time. This includes social media research (60% of a company’s sensitive information can be found on public Instagram posts), dorking (doing targeted searches on a company to find private documents and information), and picking a target.
Often, photos found by searching Instagram geolocations and hashtags can reveal information such as the operating system, email client, and antivirus used by a company. It can even reveal the landline phone and printer models used by the company, their office layout, and vendors they use (which can be spoofed to obtain information on the company’s finances).
Many times sensitive documents have accidentally made their way into search results. Google dorking — performing searches such as site:google.com filetype:pdf OR filetype:docx to obtain files that were not originally meant for public viewing — can help with uncovering internal company documents and policies. These can help an attacker establish general logistics about how the company works, how their IT and helpdesk is structured, and even lingo used inside the company.
Attachers often adopt the person of someone who actually works for the company, making it harder for the victim to figure out a social engineering attack is in progress through a quick search of who they claim to be. This can be accompanied by a spoofed telephone number (something easy to do for free online).
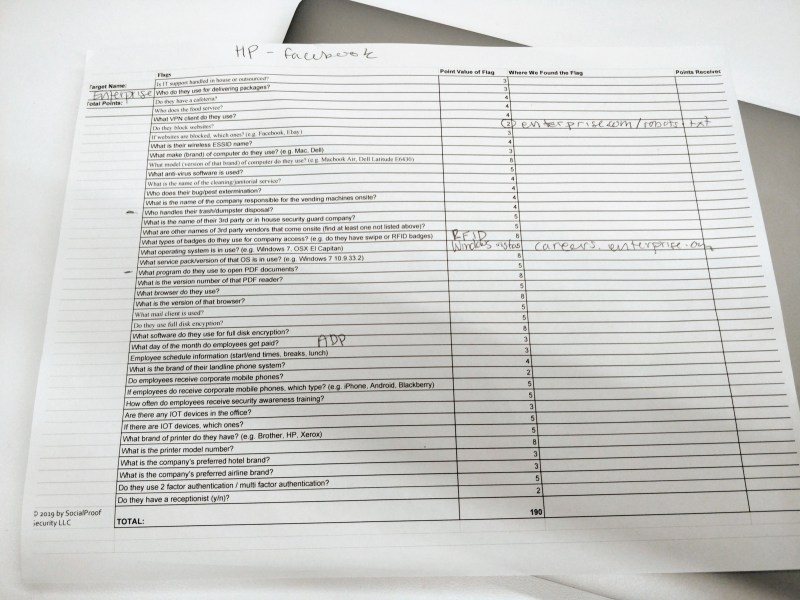
The workshop ended with an OSINT capture-the-flag, where teams of players were instructed to find as much information as they could about a target company from open-source information. Actually vishing a company, however, is against the law unless there are legal steps taken to ensure that the attacks are being done as a way for the company to pen-test their own security.
Defender Takeaways
From the perspective of a defender, this is all incredibly alarming information. Not only are good social engineers difficult to distinguish from actual employees, contractors, or HR professionals, but they’ll be armed with a toolbox of information to use to gain your trust and tap into your intuitive sense of safety.

Furthermore, having 2FA-protected accounts is important. In the case of busting a social engineer, soliciting a security verification — like asking them for a call or email back — can be the difference between being the victim of a hack and staying diligent in the face of cybersecurity threats.
If you have the chance to attend DEF CON, I’d recommend sitting in for one of the open SECTF challenges. It’s quite an experience watching ordinary competitors sit in a glass box and convince companies to give up their most sensitive information for a chance to make friends with ‘Sarah from HR’.
















Interesting, but how much of this is going to be culturally influenced?
all of it, the strategy for social engineering depends on the culture of the entity of which you are attacking. It would be foolish to think that the strategy for getting into a SV Tech company is going to work on a defense contractor in the middle east, or a medical company in india or a manufacturing company in germany.
Likely a lot. Thought I suspect the influence would only affect the way the attacker approached the social engineering, not necessarily the effectiveness of the attack overall.
I am assuming you mean regional/ethnic cultures, but this also holds true to workplace culture. The HAD writeup hints at this in the OSINT Strategies section when they mention picking up the company lingo.
People really need to stop citing the milgram experiment. Its conclusions have increasingly been either overblown or called into question so fundamentally that it is no longer trusted.
While I’m being contrarian, ‘vishing’ is a needless term that seems like someone made it up simply to make their mark on the community; not to increase clarity.
“While I’m being contrarian, ‘vishing’ is a needless term that seems like someone made it up simply to make their mark on the community; not to increase clarity.”
I agree, phishing is a perfectly capable word and as far as i am concerned has never been limited to email only. Phishing was a play on fishing but i have no idea what vishing is supposed to mean.
Oh so this. It’s just lazy – Google the topic for relevant filler and ooooh Milgram. Again. For the millionth time.
“Video unavailable – The uploader has not made this video available in your country.”
Apparently they don’t want anyone in Canada to see this.. wtf.
try this:
https://y2mate.com/de/youtube/bjYhmX_OUQQ
“Of the $11.7 million companies lose to cyber attacks each year”. To be clear, if I interpret the report that this number is from correctly (https://www.accenture.com/us-en/insight-cost-of-cybercrime-2017), then this is the average cost *per company that they asked* in 2017. It looks like a somewhat arbitrary number, I can’t find evidence that the writers of the report took any measures to get a representative sample; for instance the smallest company in the sample seems to be “1050 seats”, while I wouldn’t be surprised if the majority of global cost of cyber crime is endured by the many companies that are smaller than that.
In the end, the statements in the report boil down to: “we asked 254 companies worldwide and this is the average of what they reported for the cost of cyber crime”. Because they ask the same companies each year, they can make statements about whether these costs increase (surprise: they do) or whether bigger companies have higher cost (surprise: they do), but as far as I can tell, the $11.7M is meaningless all by itself.
A sample size of 254 is low indeed. One or two more would though have made a nice round number.
But the true figure for how much companies loose is a better question, though one that is at the same time rather meaningless, since correlating losses due to security to the size of the company alone is a very arbitrary measurement that doesn’t take a lot of factors into consideration at all. (After all, there are some multi million dollar companies that runs practically without IT to speak of… And then on the other side of the spectrum there are the small businesses that does nothing but IT for a living.)
Not Australia either…