Hacking these days means everything from someone guessing your password and spamming your contacts with toxic links, to wide-scale offensive cyberattacks against infrastructure by sophisticated operators backed by nation states. When it comes to hacking satellites, though, [Didelot Maurice-Michel] found himself tangling with some hardware belonging to the European Space Agency.
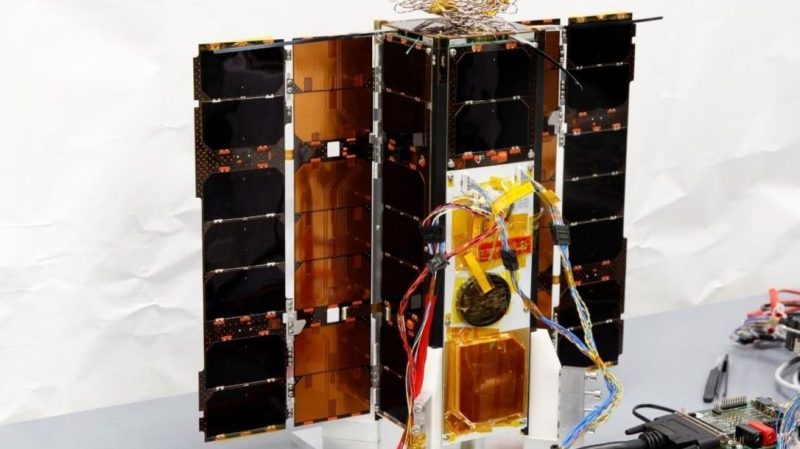
As part of an event called HackCYSAT, hackers were invited to attack the ESA’s OPS-SAT, a CubeSat intended to demonstrate improved techniques for mission control and more advanced satellite hardware. The computer hardware on board is ten times more powerful than other existing ESA satellites, and aims to take satellite technology on a new leap forward.
As with most hacking contests, it wasn’t a perfect representation of a real attack. Hackers were instructed to only exploit the payload, and a system image was provided for them to work with.
[Didelot] goes into a great deal of detail, explaining how he worked his way through the security architecture of the satellite’s software, leading to takeover of the satellite with root privileges. He found several vulnerabilities along the way, with the ESA being notified of such well before publication of the article this month.
In today’s geopolitically-fraught world, it only makes sense that satellites would become another battleground for cyber soldiers on all sides. Friendly exercises like HackCYSAT can serve as great training for those working on satellite embedded systems to help them shore up security, while also being a useful guide for offensive operatives to hone their skills as well.
We recently looked at the amazing bounty to be had when eavesdropping on satellites, too. If you’re out there experimenting in this space-based field, don’t hesitate to drop us a line with your findings. Happy hacking!















Please pay special attention to the last paragraph, where it is revealed that the HackCYSAT quietly cancelled the event without really telling the people who had submitted applications.
Bad look if you ask me, especially if you hope to get any renewed attention from security professionals for your next event.
Jeez yeah what a bad look for them. I mean, we are getting just one side of the story here but that kind of accusation does not go lightly.
That’s awful! The author clearly put a lot of free work into this for them and should be acknowledged. It seems the ESA’s pride is more important to them than their gaping security holes
I man, this might as well be an article on “how to cheese off security specialists”!
What cowards at ESA