Rolling codes change the signal sent by car keyfobs unpredictably on every use, rendering them safe from replay attacks, and we can all sleep well at night. A research team lead by [Levente Csikor] gave a presentation at Black Hat where they disclose that the situation is not pretty at all (PDF).
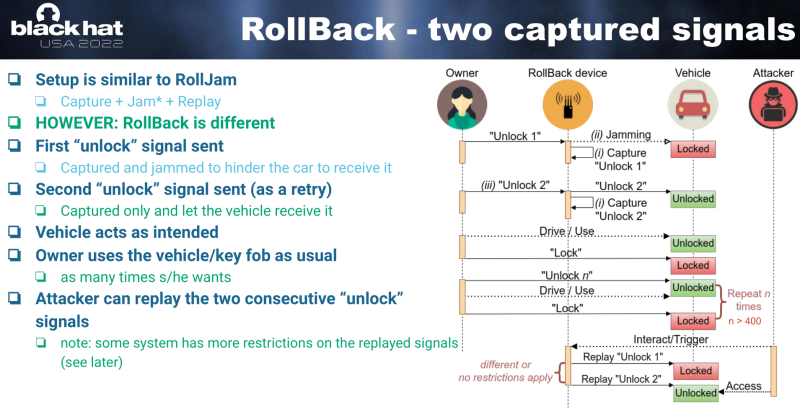
You might know [Samy Kamkar]’s RollJam attack, which basically consists of jamming the transmission between fob and car while the owner walks away, fooling the owner into clicking again, and then using one of the two rolling codes to lock up the car, keeping the other in your back pocket to steal it once they’re getting coffee. This is like that, but much, much worse.
It seems that most of the rolling-key systems accept a sequence of valid keys as kind of a “resync” code – the actual number varies from a sequence of two to five. RollBack, as the new hack is called, takes advantage of this behavior. You somehow eavesdrop on a few keyfob presses in a row, and you can reset the code and open the car forevermore. As with RollJam, probably the easiest way to get multiple codes from a fob is to jam a couple and record them all, but the jamming isn’t even necessary. Simply having a handful of consecutive keycodes suffices.
This “resync” behavior does seem to be documented in the rolling-code chips’ datasheets, as the researchers point out in their slides. In hindsight, it’s a horrendous security hole. Having a series of keyfob codes compromises a car forever, in contrast to [Samy]’s RollJam attack, which must be executed before the owner presses the fob again. We never got the details on a couple of prior claimed attacks, but it’s quite possible that this is what was going on.
If this flaw is as widespread as the researchers fear it is, we would be very careful about pressing our keyfob twice, because mitigation is going to be a nightmare.















Just grab some toggle switches and implement the security system from Fury Road under the dashboard
Thief with flatbed truck says “whatever” and your car is gone.
It’s like thinking that nobody can steal your laptop if you lock the screen.
I’m going to go out on a limb here and submit that the number of thieves roaming around with flatbeds is far lower than that of them with radio-based break-in devices.
Over here in the UK our caravan-loving friends are well known to use low-loaders with HIAB cranes to reach across locked yards and repatriate large items such as trailers, mini diggers, towed generators, etc.
This is what happens when you ban guns.
In this day and age one can never know
People actually think that locking the screen somehow prevents theft? I’ve never thought anything like that. I never even thought that anyone thought that. Maybe I give people too much credit.
Of course. Just let me stuff this flatbed truck into my pocket…
Ouch.
Happened to a friend. When he returned home his neighbours said they saw it being driven off on a flatbed with the lights flashing and horn blasting. They had not thought much about it at the time. It had been lifted over his fence and was undoubtedly parted within the hour.
In the electronic security profession car alarms are treated as a joke. They are ‘Security Theatre’.
And watching the LockPickingLawyer on Youtube has destroyed any faith I may have had in car locks.
Maybe add a security chain connected to the ground, and looped around part of the suspension.
Then the flatbed owners will also need an angle grinder.
Hold my beer and I’ll pick your padlock lock. No angle grinder needed. LPL ain’t the only one with lockpicks.
Locks have the only purpose to keep honest people honest. For criminals they are just a mild inconvenience.
I think the real lesson here is that you were gullible enough to believe that an industry that started by having a total of what, 9 keys for a mass produced vehicle, might actually be able to catch up when it comes to keys….
The smart thief with an enclosed trailer to block tracking drives by the guy with the flatbed who got busted. Goes on to sell loot.
I prefer my security system – 20+ year old trucks that have only ever lived in NY. I can park anywhere I want in redneck / druggie territory with the windows down and the keys in the ignition without having to worry about a thing.
Haha. My dad does this (and also in NY) but there’s still a risk. Some guy was running from the cops, found dad’s truck, stole it and crashed it. At least take the keys with you
I hope the thief at least got banged up in the deal.
Is this different from the rolling code schemes used in garage door openers? They’ve been easily breakable for years.
I was wondering the exact same thing.
Very likely the same chips / family although garage doors are likely 5-10 years behind automotive.
Got a source? I have never seen them be “easily” breakable
Or just drive a manual transmission car..
How does that stop a thief with a flatbed truck?
If you buy a quirky or unique vehicle it is More likely to be stolen and stripped. They will steal it precisely because it has a manual transmission.
Since you keep bringing up flatbeds as if no one should take measures against OTHER theft methods, what’s your universal solution?
I’m guessing it involves a thermite grenade. Sure, it makes for interesting insurance claims, but the chop shop operators will never see it coming.
X here is a personal friend of mine and they would never say it but they lost their parents in a tragic accident at a flatbed factory and haven’t been able to trust flatbeds since.
Ride a bicycle :) Nobody can steal my car as I don’t own one!
The number of stolen bike warnings I see in Craigslist suggest that doesn’t immunize you from theft though. I also see sellers with rather random collections of quick-release wheels for sale in the dodgier areas of town, suggesting that locking your bike frame only helps so much…
again with the dad jokes ;-)
Good luck, my Citroën 2CV isn’t affected by these attacks ;-)
True, but two guys could just carry it away.
From my experience my 2CV is under constant rust attack :-( I can’t drive it and nobody will steal it.
If someone brings a 3CV (third horse) it might be.
It might be. I personally tested 2 US brands that werent reported to be vulnerable. One was completely vulnerable (a sequential capture could be reused indefinitely, regardless of the fob). The second was partially vulnerable, a sequential capture could be replayed twice and worked, but the keyfob would be desynced. After resyncing the keyfob (turning it in the ignition). The same recording could be used again.
Laughs in 1908 Model T
That is another type of rolling code entirely.
I regularly drive my dad’s model A. Other than prior knowledge or a flatbed no one is getting it started let alone stealing it. We leave the key in there too. Doesn’t do what you think it does.
You need to add an airbag under the drivers seat pointed up and wire it to the key…I would pay good money to watch that show
What’s surprising is how unsurprising it is how vulnerable the keyfob used to secure your $20k (absolute minimum) car is compared to a hardware security key you can get for $35.
You’d think after a couple of decades, OEMs would have realized they need to take security seriously… But of course not.
This is a feature put in there on purpose because people don’t want to be inconvenienced when the remote is out of sync. People would be ticked off if their toddler pushed the remote 11 times when they were in the mall out of range and the car stopped working. Why does a toddler have the keys? I don’t know! I don’t do it but lots of toddlers seem to have keys to SUV’s at the mall.
[quote]very careful about pressing our keyfob twice[/quote]
But we do that all the time in both cars. Once to open driver side, and once again to open all the doors for your passengers. :) Oh course my truck has a real key… Not affected.
The best security system for your car is owning a car that isn’t appealing to the masses.
Owning an insecure car doesn’t inherently mean you are more likely to have it stolen. Theft rings need to be able to part out or sell the vehicles in order to make the risk and effort worthwhile. Knowing just this you can limit your chances of getting anything stolen simply by living further away from urban centers and major shipping hubs. Theft grows more popular the closer you are to places where thieves can easily smuggle or hide their bounty.
Another reason why specific cars are stolen is to use them in committing a crime. So if you drive a snail it is a far less likely candidate.
My Datsun diesel pickup fit that category (non-turbo) I learned to be patient when pulling into traffic. And I had to be patient when refueling, anything more than the slowest stream from the pump would cause the fuel to foam up and prematurely trigger the automatic shut-off.
It also had a weird starting problem, sometimes it either needed to be nudged, or a remote starter switch to crank the engine, a theft deterrent in itself.
All In all, it was still one of my favorite vehicles. ❤
Still probably faster to use a Lishi tool on the mechanical lock.
Around here in the Atlanta area the usual reason to break into a vehicle is to steal guns. Many times they target fire department employee parking lots or night club parking lots.
A neighbor across the street was saved when they could not drive her manual transmission Cherokee. It seems R means reverse and not let’s Roll. My automatic 1982 Chevy Impala, which I kept getting offers on from the donkers, was not stolen for the simple fact the car thieves were idiots and broke the steering column ($600 repair if I didn’t fix it myself) instead of the ignition switch. The ignition switch itself is very easy to pick, along with the Club (master lock territory) , but, it was enough to defeat them.
The best bet to not getting your car stolen by code or flat bed is to have an alarm with a remote notice feature, impact and tilt witch, a steering wheel lock, kill switch, and separate hood lock with a (easy to pick) cylindrical key.
During the snow storm a few years ago that shut down Atlanta and left 1000s of people stranded on the highway, the police DID catch various people trying to steal immobilized vehicles with tow trucks. It seems all the tow truck drivers were named Capt Obvious. Which of course led to the chop shops being taken down which they fed.
It is a very chancy thing to steal a vehicle with a commercial truck (flat bed, side loader, sling tow, etc,), so, most of the time they are not going to target your Yugo no matter how appealing you think it is.
“impact and tilt witch,”
I would definitely reconsider if I found out a car was protected by a witch!
“I’ll get you, AND your little dog! Hahahaha!”
That is why auto thief is very low in downtown Salem Massachusetts, there seems to be a Cabot behind every holly bush watching their Mercedes.
The best defense from theft is have nothing they want. :D
Human organs are fetching a very good price these days. Never can be too careful.
That’s why all my incoming organs are fixer uppers! 🤣
As a young guy, my old car wouldn’t start. I found the starter relay earth connection corroded, nice fault. So I disconnected the cigarette lighter’s 12V supply, and connected the lighter to the relays earth pin. From then on, to start the car, first push the cigarette lighter.
Unstealable car. Lol
Sunds like my 93 silverado that I got a year out of before the transfer case exploded – Idiot I bought it from (price was right, and I didn’t ask the right questions) – had the main wiring harness from the dash resting on the driver side exhaust header. Shorted the ignition wire to ground, but it’s only hot on starting. When I finally figured out what was going on, there was no fixing it, so I bypassed all the column wiring, left the key for “possible,” and wired the starter through a couple momentary switches to the battery.
Go ahead and try to start that – with the key, you’d only set the engine bay on fire. With the switches, you’d only succeed at spinning the starter. Good luck, and if you can figure out how to steal it, well, the keys are literally in the ignition, you deserve it more than I do.
This makes me think. A lot of people pooh pooh security by obscurity, but if you’re doing a one-off, obscurity is likely to foil many outside bad actors. Adding a hidden switch to a car’s wiring will foil everyone except the flatbed user. Using an ssh server that requires some trivial extra step before connection. Running your java code with a modified VM whose opcodes are off by one.
The possibilities are endless, though of course posting about them burns them somewhat. And convenience always suffers.
Very true. And when you have to resort to security by obscurity (such as in most copy protection schemes), it’s best to make it really obscure and custom. It’s always just a slow-down if someone is very determined.
I think some things aren’t just going to be a slowdown, but are something no one in practice would guess. If you hack your car’s firmware so that it only starts if you enter a password in Morse on the brake pedal, and otherwise just makes it sound like your starter is bad, no one will drive away with your car.
Pro tip:
Get out of car
Look at key in your hand
Press manual lock button on the door.
Problem solved.
I have had this habit ever since i started driving.
As far back as the 1980s this wasn’t a valid sequence of events for all cars. My 1987 Volvo 740 Turbo would unlock the door again if you locked it with the door open in order to prevent you from locking yourself out. You had to close the door and lock it with the key from the outside.
Maybe I’ve missed something, but I’ve been kinda following these posts out of curiosity… are proximity key systems susceptible to this attack? Like, if I walk up to my car with proximity key entry, and push the button on the outside of the door to unlock, is that the same as pushing the keyfob’s unlock? I would imagine the sequence of events are different, but is the same rolling code information transmitted through the air?
I don’t believe this is an issue because of the difference in how they communicate. The exploit used against rolling codes is not a bug. It was a poorly thought out feature which we know because it’s in the documentation for the chip.
Old VW ignitions (1970’s) would often fail after 25-30 years. Removing/replacing them is a pain in the butt so my mechanic would install a high current pushbutton switch somewhere out of sight. You still have to have the key in the ignition, turned to the “On” position to start and drive the car. But rather than turning the key to “Start”, you pressed the momentary switch to crank the starter. I was able to get an insurance discount for having an “anti-theft device”!
You could supplement that by installing a high voltage terminal under the center of the fabric of the front seat. Activated by not engaging the secret button.
;^)
I had an old Honda CRX si with a reed switch in series with start wire. You had to know where to put a small magnet on the center console when starting. Worked well. That car was a blast to drive. Stick shift and 38 mpg. Turning radius felt like 10 ft. Only two seats so eventually our family outgrew it.
Sirs, My issue is a bit reverse of the way most think about car security, I want to do away with it! first my car is over 10 and under 25 years old (rolling scrap metal). yet it still has a keyfob/key that is unable to be duplicated by any lockshop other than the dealer, blank key is $70 , they charge $40 to cut the key, and IF you have an original key they chargeanother $40 to program it to your car!! thats $140 bucks for a second key that all cars used to come with, however if you have the misfortune to loose the original (yes thats right the car came new with 1 key, the charges are a lot steeper than that! by the way the key that is so high tech comes with the thinest most brittle after thought of tiny loop of plastic (and only made into 1/2 the keyfob case) to attach this stupid key plus to your key ring! So yes i lost my golden key! costs? Dealer key blank $70, Cutting no not 40 thats duplicating fee cut from code $85 and the $40 “programing” fee, you guessed it that was simply to add a key to the system without the original they must 1. remove all keys from system 2. program a code to the new keys transponder $65, program the new key to the body control module $70, the ecm gets a new code $70 as does the transmission controller $65 more for a total of $270 oh yea they also charge the standard service fees for shop repairs another $35 and (not the dealers fault yea right) the car that is locked and secured better than my house , has to be at trhe dealer meaning a tow bill of most likely more than 200 bucks (it cost me $165 bucks on night to get a car with a blown tire and unuseable spare towed 13 miles a few months ago, it is over 25 miles to the nearest dealership) oh and of course since this is just a walk in repair (think they are funny do they ?) the fastest they can get to the job is next week , possibly thursday or Friday!!
WORD OF WARNING do not ever buy without a minumum of 2 sets of keys included in a car deal no matter what, walk away from the deal if they drag their feet (only the cheapest sleazyest sales guy would let a sale slip by for the price of a spare key, and you should go else where in that case anyway) it should be required by law!
How about adding a device to cars that listens for these replay attacks and just blocks them.
It would have to always be listening and record every key code the fob ever payed. Then using an SDR maybe, interfere with the cars reception of the 2nd code if the first matches one it’s seen before.
If you need to ever need to do a resync this would have to be disabled but that seems like a small price to pay.
You don’t need to make your car “impossible to steal.” You just need it to be “harder to steal than the car next to it.”
After a thief smashed both door locks and a window, just to get a few coins out of the ashtray, I have started leaving my car unlocked, but with a club lock on the steering wheel. No problems since I started doing this in 2016.
Ironically, the same idea seems to work for the convertible. Because the thief can see there’s nothing of value, they don’t bother smashing windows.
Same over here..