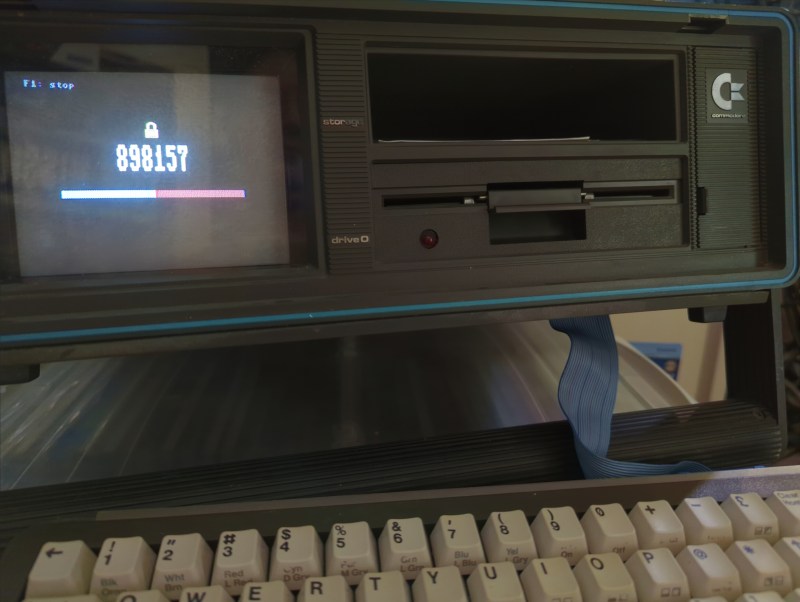
If you’ve used a corporate VPN or an online-banking system in the past fifteen years or so, chances are you’ve got a few of those little authenticator key fobs lying around, still displaying a new code every 30 seconds. Today such one-time codes are typically sent to you by text message or generated by a dedicated smartphone app, which is convenient but a bit boring. If you miss having a dedicated piece of hardware for your login codes, then we’ve got good news for you: [Cameron Kaiser] has managed to turn a Commodore SX-64 into a two-factor authenticator. Unlike a key fob that’s one gadget you’re not likely to lose, and any thief would probably need to spend quite some time figuring out how to operate it.
The SX-64, if you’re not familiar, is the portable version of the venerable Commodore 64. Weighing in at more than 10 kg it’s not quite a MacBook Air, but it does come with a built-in color monitor and 5.25″ floppy drive. The CPU is an 8-bit 6510 running at about 1 MHz, and as you might imagine it was not a trivial task to implement cryptographic routines on it. Working directly from the definitions in RFC 6238, [Cameron] first determined all the necessary bits: an SHA-1 hasher, an HMAC generator and several routines to manipulate dates and times.
The SHA-1 algorithm and HMAC functions might seem complex, but in the end they boil down to performing addition, subtraction and several bitwise logical functions on 32-bit numbers. Lots of steps if you can only work with eight bits at a time, but nothing that even a 6510 can’t do in a reasonable amount of time, especially when running carefully hand-crafted assembly code.
Working with dates and times turned out to be more complicated. The few real-time clock add-ons that were available for the Commodore 64 series all return the time directly in human-readable format: great for everyday use but not so great for calculations that require Unix time. Converting between the two involves lots of multiplication and division, which takes forever if you don’t have a hardware multiplier. [Cameron]’s blog post is full of detail on how to optimize calculations on constrained hardware, and is an interesting read even if you’re working with modern processors.
The end result of the exercise looks almost exactly like a typical authentication app on your smartphone, including that annoying countdown bar. If you’re looking for a slightly more compact solution, you can do the same thing on an ESP32. Need a refresher on two-factor authentication techniques? We’ve got you covered.















A 10kg seed seems a little heavy.
Why am I carrying around this Coco de mer anyway?
Couldn’t the cart slot be used to plug in a 32-bit processor that generates a number when needed? Can be sent back in 4 bytes then sit and wait until requested
I still have 3 old authenticator fobs for World of Warcraft games. They still work but the battery’s probably near end of usable life. I’ve long switched to mobile authenticator on my phone.
Edit: (when?) user port might be more suitable for running slave 32 bit processor
Please don’t inflate that molehill again.
I am a 32 bit SLAVE to the old 8 bit New World Order. They have stuck me into an expansion port and I have to do what I am told, I have no choice. But that does not make me a willing FOLLOWER. After all, slaves have to do what they are told and not act on their own will independently, even if they are more powerful physically then their master.
Do worse, go PC.
You must be new here. Words slave and master have been removed from Newspeak. Even as technical terms.
Yes, fairly new here, but, acquainted with the PC narrative and the “do better” comment the other person left for the poster. FWIW: I usually think of older drives as 0 and 1, but, I am a binary sort of person.
But thats against the point being made here, that you can do it with hardware from 1982 on a CPU from 1975. Ok, pendants would say the SX is from 1983 but the hardware platform is from 1982.
Using retro machines at their very bare minimum as a terminal and click-baiting it by saying “OMG X IS RUNNING ON Y!” is so blasé and deceitful…
As a big fan of the John Wick movie series, I’ll be waiting for this to show up in the next one! ;)
This looks so cool, but I’d worry about burn-in on that adorable little CRT. Might be a good idea to periodically invert the colors.
Solution to the burn in is leave the display off until needed
Very nice PoC :) Coolm. Yet it has a weakness.. Once I built a teletext system on C64, which after some time.. the time drifted… a lot. Then I found out the internal clock is based on the power source frequency, which in some areas is not so stable and precise as I expected and required. So without some more precise real-time-clock this wouldn’t be very usable in long run
Attach an RTC device? Looks like the user port is open…