Wardriving started out as a search for unprotected WiFi access points before hot spots were prevalent. And so this ZigBee protocol wardriving hardware which [Travis Goodspeed] put together really gives us a sense of nostalgia for that time. Don’t get us wrong, we love our pervasive WiFi access and don’t wish to go back to simpler times. But if the radio signals your looking for are scarce, locating them provides a challenge.
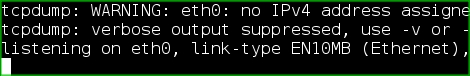
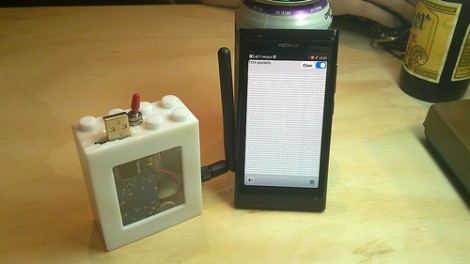
Regular readers will recognize that [Travis] is interested in all things RF. One of his projects included sniffing wireless keyboard packets out of thin air and displaying them on the screen of his Nokia N900. This is right along those lines but he’s upgraded to an N9 phone for the display hardware. He switched up the RF hardware, using a TelosB (a board he’s already familiar with) to get on the 802.15.4 ZigBee spectrum. This dev board has an expansion port which let him use an RN42 module for wireless communications with the phone. This means the sniffing hardware can be hidden away in a backpack or jacket. After all, nobody will question someone walking around staring at a smart phone.