[Zitt] has a security camera which will send him messages any time it detects motion. However annoying this might seem, we’re sure he has his reasons for needing this much immediate feedback. The real problem comes when he goes to view the feed on his iPhone. His solution is to turn the camera’s notifications off, and use his own script to transcode a clip and shoot off an email.
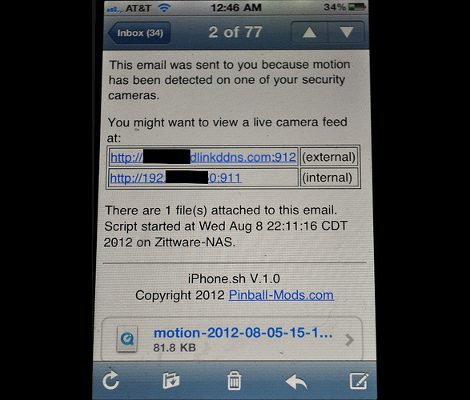
As you can see above, the end result is a concise email that includes the recently captured clip, as well as links to the live feed. He has been storing the clips on an LG N4B2 Network Storage Server (NAS) and since he’s got root access to the Linux system on the device it was an easy starting point for the new system. After he compiled FFmpeg from source (which handles the transcoding) he started work on the script which backs up the recordings and sends the email messages.
One thing he wants to add is a method to clear out the old backup videos. Having encountered a similar issue ourselves we decided to share our one-liner which solves the problem. Find it after the break.
Here’s a cron job that runs at 4:50pm everyday and removes backup video files older than three weeks. If you don’t understand what it does, just consult the documentation.
50 16 * * * find /Videos/backup/*.mpg -mtime +21 -exec rm {} \;















The unix geeks among us eschew -exec in favour of xargs:
find /Videos/backup/ -type f -name \*.mpg -mtime +21 -print0 | xargs -0 –no-run-if-empty rm
This guy seriously doesnt know about the screenshot feature?
That was my first thought too
In the event that someone reading this also doesn’t know it:
While holding the home button (below the screen), press the sleep/wake button (on top of the device.) The screenshot is saved to the camera roll (where photos are stored.) Works on all iOS devices, even those without a camera.
Actually; no I didn’t know about the apple screenshot feature… thanks for keeping me informed.
I have updated the screenshot in my blog.
I’ve run into issues with using find and a large number of files from a security cam in the past. I’ve found that using a python script and the glob module is much more robust. Of course, I assume the composite video is much less numerous than the list of stills I was dealing with. Good post.
Um… and the reason for not just using -delete is?
find /Videos/backup/ -type f -name \*.mpg -mtime +21 -delete
Thanks to you and Mike (the reporter); V1.1 was posted to my blog with these changes. I went with:
# number of days to keep security videos (~6mths)
let sourceage=28*6
# number of days to keep backup videos (~1mth)
let backage=31
[…]
#clean up really old files (credit: Hackaday reporter MikeS and user gerphy)
find ${sourcelocation} -type f -name \*.${conversionext} -mtime +${sourceage} -delete
find ${backlocation} -type f -name \*.${sourceext} -mtime +${backage} -delete
find /Videos/backup/ -type f -name \*.mpg -mtime +21 -delete
Don’t make things more complicated than they need to be.
You better black out that internal IP…
He gets points for doing it the hard way. As for the smart way…
@NamedOne: I know it is actually labeled (internal) so this is pedantic but it is a common mistake that any 192.x.x.x address is private. This one bit me really bad when I was doing support someone who’s public IP started with 192 and the connection didn’t work. I was absolutely convinced this was suppose to be private, and some kind of misconfiguration. Learn the hardway.
Why do we still have dialogs with “n file(s)”? Surely it’s no more effort to figure out if there should be an ‘s’ after ‘file’ as it is to insert ‘n’ into the string?
I like the way people are improving on the original posting. I don’t like the tone of that posts though: “This could be done better”, “Did it the stupid way”, “I know better than you” etc.
I think the guy was kind enough to post his useful setup, it is up to anyone to improve or publish his/her better solution. Until then, I don’t see better stuff.