Webkeys are small, inexpensive USB devices which launch a web browser when plugged into a computer. They’re given out as a promotional item, but they can be fun to hack as well. [Brad Antoniewicz] recently got his hands on one and decided to crack it open to see what he could accomplish.
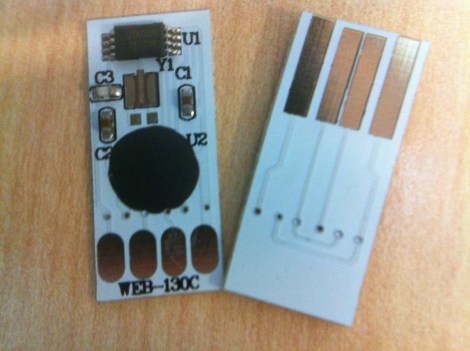
The majority of the device was packaging but it didn’t take him long to get down to the guts seen here. There are two units shown in the image above so that we can get a look at both sides of the circuit board. As you can see, there’s a chip-on-board processor (that black blob) that handles the USB connectivity. But the data which is pushed to a computer is stored in that EEPROM chip at the top. It’s got legs which are just begging to be probed. [Brad] wasn’t able to find the exact datasheet but he got some clues as to the pinout. Using his Bus Pirate he was able to establish communications and sniff the i2c traffic. With that success he went on to overwrite that data. You can see a quick demonstration of it after the break.
[Brad] hopes to do a bit more with the hardware. He thinks those four pads can be used to reprogram the MCU. We’ll keep our eyes out for updates as he moves along on that mission.















It has already be done:
http://jjshortcut.wordpress.com/2011/09/26/webkey-hack/
Those are shame to be shrown away in dozens.
I’m glad to see someone can get something more out of it.
So it looks like its just a keystroke repeater (Keyboard HID)
good stuff!
is there any way for the usb device (or someother similar device) to be able to recognize the underlying OS ? so you can make it do different stuff depending on the OS…
Just thinking aloud… I’m sure you could do something like nmap does for OS detection over TCP (it’s actually scarily accurate). Basically try rarely-used modes or exploit ambiguities in the relevant standard to tease out subtle differences in behavior. Failing that, you could try impersonating various devices that typically only have drivers for specific OSs, but that’s ugly.
As Gaicomo says, yes. One way I could think of would be to create a USB MSD with various filesystems on different partitions to see which ones are properly accessed by the host OS.
Just looking at the photos of both sides, those pads mirror the USB edge connector. Maybe that’s for soldering down a real USB connector?
Those things are fun! I sure wish I could get my hands on some more…
http://www.skot9000.com/amex-webkey/
My guess is it’s a Cypress usb device in bare die packaging.
I say this because I have a large button style one that has a tssop packaged device and prom, with 3 led’s and some other cruft.
The low speed usb devices sometimes had the programing pins (IIC bus based) overlayed on the D+ and D- lines.
If anyone has a cypress Miniprog and one of these, it’s trivial to test, since the PSoC Programer software should be able to do an ID query of the device once you get the wiring sorted out.
I have one of these from Hyundai but there is no EEPROM at the top. There is a spot for it on the board but it is empty.
Woo-hoo – grab a few hundred of them on trade fair, and re-distribute them with malware flashed on it.
And the best is: blame will fall on the companies who had their logo printed on the package.
Hacking for fun and profit!
This doesnt work with all of them, I got a button that goes to 2×2.nl and probably can only change the url. The url is zero terminated and I need to calculate a 16bit crc… wich I now have to learn how to do.
Most of these can be reprogrammed using just libusb.