A few months ago, a strange account popped up on hackaday.io. Whoever is behind this count is based in Bielefeld, Germany – a place that doesn’t exist. They are somehow related to the Berenstain / Berenstein Bears dimensional rift, and they may be responsible for giving Cap’n Crunch only three rank insignia on his uniform. There is something very, very strange about this account. Since August, a black and white image of static, 98 pixels wide and 518 pixels tall has sat on this account profile. The Illuminati has given us enough clues, but until now, no one has managed to crack the code.
The first person to make sense out of the patterns in static is [Moritz Walter]. What’s in the code? More codes. While that’s not really helpful, it is to be expected.
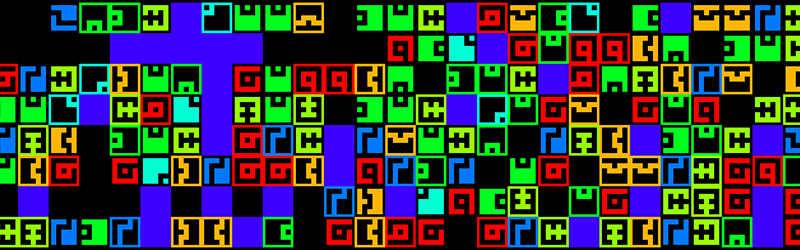
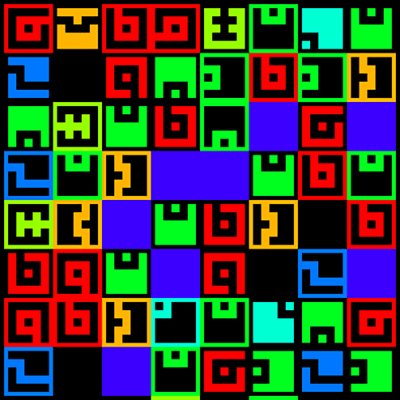 The hackaday illuminati included one additional piece of information with their encoded static image: a 12×12 pixel bitmap. When this bitmap was XORed with the main image, symbols appeared. In total, there are only seven unique symbols in the image. These symbols seem to be stolen from the Fez alphabet, but there are some significant differences. These symbols are rotated multiples of 90 degrees, and are surrounded by a one pixel border that is either black or white (we’re calling the border a ‘sign’ bit). In total, these seven symbols arranged in four different rotations with two different signs yields forty unique variations of a symbol in the decoded image. At this point, it should be noted 7*2*4 = 56.
The hackaday illuminati included one additional piece of information with their encoded static image: a 12×12 pixel bitmap. When this bitmap was XORed with the main image, symbols appeared. In total, there are only seven unique symbols in the image. These symbols seem to be stolen from the Fez alphabet, but there are some significant differences. These symbols are rotated multiples of 90 degrees, and are surrounded by a one pixel border that is either black or white (we’re calling the border a ‘sign’ bit). In total, these seven symbols arranged in four different rotations with two different signs yields forty unique variations of a symbol in the decoded image. At this point, it should be noted 7*2*4 = 56.
As of now, cracking the illuminati’s cyphered machinations has hit a roadblock. There’s a dead image file on the illuminati’s profile. Until that image is rehosted, there is no way to progress any further. That’s not going to stop people from trying, though: the chat channels on hackaday.io have been buzzing about the newly decrypted images. Hopefully, with time, someone will figure out what it all means.















i’m no cryptographer, but i hypothesize that the first 10 (from left to right) may represent 1234567890.( 0 being the black empty square) the rest would probably represent symbols and letters, but i wouldn’t know where to start if they did.
the “missing image” is a link to a blank text file. It doesn’t seem to be a picture at all. just a file of 0 bytes titled: “0dfz7.txt” is this a clue for the other two images by chance?
looked like an imgur link but, probably an insane coincidence. http://imgur.com/0dfz7
Hmm.. German language in the image!
Plot thickens… Or does it?
Google translate says:
“I’ve applied for should actually be forwarded to each”
“Ehm chief says I should withdraw units , sorry”
I’m going to go with coincidence on that one.
Uploaded 3 years ago – red hearing ?
Could just be a random piece of existing public material used to decode a cypher or something.
This was done with messages hidden in newspapers!
I’d be genuinely surprised if the “0dfz7” is meaningful. It seems like it’s just the arbitrary string of characters assigned to that particular file on that particular file host, similar to image IDs on Imgur. shortened URLs via things like TinyURL, and more. I would by all means suggest combing through all image hosts and file hosts to see what lies there with that ID, I suspect it was an error on the coordinator’s part.
It forms a 2D QR style barcode. It’s like one of those rearrange the image puzzles.
Coincidence that the GCHQ answer was a QR code too.
spoiler: it deciphers to “http://tinyurl.com/2fcpre6”
What is the possible max message length if those are some kind of byte? is their “missing file” filename the prime, hash key, signature, or checksum? they only used an xor for the first gate (and gave us the key) so I dont imagine the rest of the obfuscation is that complicated.
lol, just saw the title of this article.
Is the title a clue or just bed proofreading?
I’m gonna go with bed proofrodding
https://en.wikipedia.org/wiki/Rainbow_table
Did you guys check out the HAD.IO page? It seems to have been partially solved…
0100100001000001010000110100101101000001010001000100000101011001
Oh wow if you interpret the images as ones and zeros you get
HACKADAY
so impress much wow
8×8 on or off
6675636b74617264
As soon as I saw “Fez” I lost interest.
Ugh, Phil Fish…
Saw the pic, immediately thought fez.. nevermind.
http://www.govgistics.com/Public/Cage/0DFZ7
Anything?
Baudot
Obviously a intelligence probe, not a test,
Seems like an out-stretched QR-code or something similar
Without a 6-figure reward, I’m not interested. I make more money tracking down the location of ISIS routers in Turkey and Lebanon.
Sure you do, sweetheart.
Bielefeld gibts doch garnicht ;)
Bielefeld, ein gedank von Dr. Oetker…jetzt mag Ich einen pudding. ;)
Kinda reminds me of this ol’ gem from +Ma http://3564020356.org/
7 times 4 is 28 – – – that is 26 characters in alphabet – with space and comma.
The “empty” hint image… Look for it in the past…
[ http: //web.archive.org/web/20150801000000* /https ://infotomb.com/k5ovc.png]
Remove the spaces and square brackets from the waybackmachine link… concat it to one link and you will see what I’m referring to. Also keep up to date with what we have so far at https://hackaday.io/project/8762-itanimulli-code-crackers
Grrr… HAD link sanitiser! http://web.archive.org/web/20150801000000*/https://infotomb.com/k5ovc.png try that.
possibly relevant that Bitcoin addresses are encoded in base 56? maybe there’s a transaction on the blockchain with a message attached?
It’s a pity you don’t have a donate button! I’d without
a doubt donate to this excellent blog! I suppose for now i’ll settle
for book-marking and adding your RSS feed to my Google account.
I look forward to new updates and will share this
blog with my Facebook group. Chat soon!
code in Latin
look at the bottom squares of the Graeco-Latin square that correspond to this transversal of the top Latin square. Notice that all these squares have the same color!
If you now look at the small squares with the same color in the top Latin square, you’ll notice that they are on a transversal of the big (bottom) Latin square. So, if you have a Graeco-Latin square, then the transversals of one correspond to the positions with the same color in the other, and vice-versa.
So, how can we use this idea? Suppose you are trying to make a Graeco-Latin square. If you start with a bottom square and can break it up into transversals which don’t overlap each other, then you can make a second Latin square which will form a Graeco-Latin pair with the first. You form the second square by taking each of these transversals and putting the same color in each of the positions. Use a different color for each transversal. Here’s an example. We first start by breaking up a Latin square into non-overlapping transversals.