As reported by The Register, hackers can now listen in on conversations happening around your computer by turning a hard drive into a microphone. There are caveats: the hack only works if these conversations are twice as loud as a blender, or about as loud as a lawn mower. In short, no one talks that loud, move along, nothing to see here.
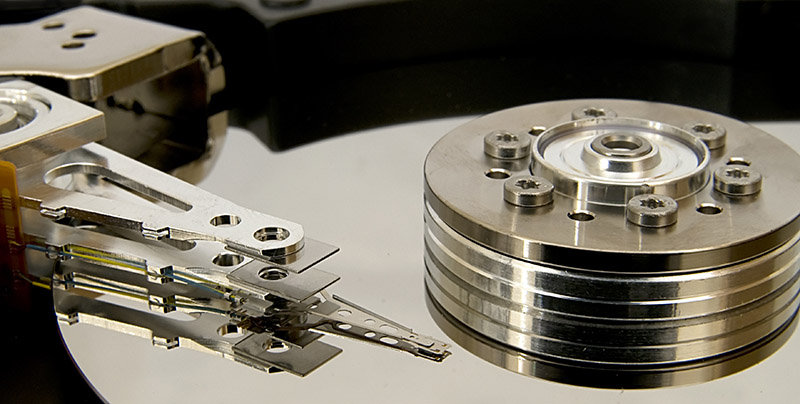
The attack is to be presented at the 2019 IEEE Symposium on Security and Privacy, and describes the attack as a modification of the firmware on a disk drive to read the Position Error Signal that keeps read/write heads in the optimal position. This PES is affected by air pressure, and if something is affected by air pressure, you’ve got a microphone. In this case, it’s a terrible microphone that’s mechanically coupled to a machine that has a lot of vibrations including the spinning platter and a bunch of fans inside the computer. This is an academic exercise, and not a real attack, and either way to exfiltrate this data you need to root the computer the hard drive is attached to. It’s attacks all the way down.
The limiting factor in this attack is that it requires a very loud conversation to be held near a hard drive. To record speech, the researchers had to pump up the volume to 85 dBA, or about the same volume as a blender crushing some ice. Recording music through this microphone so that Shazam could identify the track meant playing the track back at 90 dBA, or about the same volume as a lawnmower. Basically, this isn’t happening.
The interesting bit of this hack isn’t using a hard drive as a microphone. It’s modifying the firmware on a hard drive to do something. We’ve seen some hacks like this before, but the latest public literature on hard drive firmware hacking is years old. If you’ve got a tip on how to hack hard drives, even if it’s to do something that’s horribly impractical, we’d love to see it.















Too bad that SSDs are already mainstream.
Was about to say the same.
ssd firmware hacking is fine as well :P
Most of those drives are built around two or three ARM cores with a JTAG accessible, the tricky part would be to actually reverse engineer the architecture and be able to do something useful
Done and dusted by Sprite :)
http://spritesmods.com/?art=hddhack
I propose starting on page 3… and click the first link he posted.
http://spritesmods.com/?art=hddhack&page=3
man, no wonder “sprite” is so friggin’ famous.
1: Attacks never get worse, they only get better.
2: The only people still running spinning-rust are running LOTS of it.
3: If you have an array of time-correlated microphones, you can do beamforming.
4: Manufacturers’ own firmware update utilities can rewrite the firmware over the SATA connection. Ergo, so can hackers. It just wasn’t the focus of this research.
I expect by next summer, someone will have turned a small NAS into a microphone array capable of picking up regular conversation several feet away.
I’d certainly be impressed by someone turning the NAS into a usable mic; but in terms of ‘unnerving possibilities’ the suggestion for exfiltration(use compromised HDD to tamper with system files) seemed even more alarming and likely more immediately practical(and useful against disk arrays that are shoved into a rack and touched as little as possible because it’s loud and cold in there).
HDD controllers are fairly punchy(the one in the linked article had 3 ARM cores, one apparently just spare, SSD controllers tend to be even punchier and equipped with more cache RAM), and responsible for bad block handling/general mapping between what happens inside and the logical address space presented to the outside world.
That’s very possibly enough to accommodate at least enough of one or more filesystems to allow recognizing files worth changing and room for both the unmodified versions(to pass secure boot type integrity checks) and tampered versions(to achieve the desired behavior).
Trying to run a system where your mass storage device hates you would not be a pleasant business.
The attack would be tricky and have to be tailored to the target(since filesystems and files worth tampering with differ) and might not be viable if you only control one disk in an array(though, in that case, anyone know if there’s a way for HDDs to chat with each other without the host noticing? The SGPIO or i2c connections used by backplanes might be worth a look…); but against a known target it would not be pleasant.
The best defense I’ve seen against this is using something like grub in a coreboot payload to load up a 100% encrypted disk by doing the decryption in the bios. From there you use a filesystem that can detect and repair errors in case the drive wants to try tampering with the data anyway.
Of course, somebody could still just *brick* the drive.
Just encrypt all or most of the disk. Sure, somebody who knows your system well enough might be able to load some code up before the decryptor starts, then find the decryptor’s password in RAM. That is, if you keep it in RAM and not use some s00per-paranoid method of storing it the the remanent capacitance of the PCB tracks or something. But it’d have to know what it was looking for. If you made the encryption truly end to end, say off-disk hardware doing the decryption from the first bit, then the disk would have no chance of injecting any code. But there’s surely 999 better attack vectors than that.
The “microphone” thing is extremely silly, because if somebody has the ability to update your drive’s firmware, seemingly without your noticing, then, paranoid-encryption excepted, they own your system. So just switch on the internal mic anyway. Or the cheap passive speakers or headphones. Sound jacks on modern PCs are software routable, so you could tell the card that the speaker port is actually the mic port, with an incredibly crap low-impedance mic attached. Or else, even better, just nick all your files! And while they’re there, put the PC on remote control.
This is a pretty Heath-Robinson hack. I estimate it’s use in reality will be 0 cases, within a 15% margin of error.
They have bugs like a grain of rice these days. Those are also better. Any room with any features at all, even the wood chips in the wallpaper, could hide a bug. If you still can’t plant one, bribe somebody who works there. If that fails, bring in the LSD and prostitutes, if only to cheer yourselves up.
As an audio bug the Great Seal Bug / “The Thing” was better than this HD thing, much better technically, spy-wise, and by any other metric you could think of. That was from 1945.
Alexa! Find all hdd microphone hacks.
if you’re going to call mechanical HDDs “spinning rust” then I think it’s only fair to call SSDs “hot sand”
I would opt for “dirty sand” :-)
Which is why the SSD controller company that named itself “Sandforce” always gave me such a grin!
It took me literally years to realise why it’s called “Sandisk”. Might be “Sandforce” is to sound a bit like that, maybe being next to it in the phone book gets a few misdialled calls. If they still have phone books.
So now we can remotely assess if the kids are running a blender and playing loud music while we’re on vacation?
SORRY, WHAT? CAN’T HEAR YOU!
Here’s the fix.
Use SSD’s.
I saw this in ekoparty 2017 too, its an interesting resource
https://www.youtube.com/watch?v=poktHJzvDX0
https://hackaday.com/2017/10/08/your-hard-disk-as-an-accidental-microphone/
So, maybe hard drive mfgr’s have already installed microphones, in the event a future update will necessitate one?
You, like the HaD blog from a day ago…
B^)
tradtional microphones are easy to spot.
MEMs based microphones, not so much.
They may already be present, and we would never know.
Thanks for the spoiler up top Brian, saved me enough time to come thank you here
By combining measurements of hard drive usage and fan speed(which is roughly proportional to CPU load), you might be able to achieve a crude power-analysis-based side channel attack.
Of what? If you’re after encryption keys stored in the CPU you’ve got no chance, even if you connected directly to the CPU’s power pins. They’re like welders, nowadays. Fan speed is glacial compared to CPU speed, even the PWM frequency, never mind the physical inertia and the field in the motor coils. The data from the fan system is even way too slow to do audio on, even if something as noisy and turbulent as a fan would ever work as a mic. You’d have difficulty hearing nuclear explosions, and not even because of the general melting.
Great, now all my relatives will be calling up thinking “they” are spying on them again.
Wasn’t their some talk about using fans to exfiltrate data by controlling their frequency and using that as a slow data channel that could cross an air gap?
Would the internal fans in a server or storage appliance add too much vibration to detect fans nearby?
The comments here sound like using the HDD as a mic had been done before but has anyone tried putting these two things together?
It might be pointless as both machines would need to be compromised which would imply an attacker has access to both machines. But it might be interesting as an academic exercise.
If the fans are the ones they have on the front of aeroplanes, maybe. The article says it’s sensitivity is a lawnmower worth of decibels. Really, no chance. This isn’t even a thing, isn’t even of any academic interest, unless you have fans that can cut lawns.
What is interesting, and I believe has been used, is ultrasound as a transmission medium. Some mobile phone apps have used it to communicate with things. One was a cheap remote-control keyring to control the phone’s camera, that would of course only work with the associated app you had to download. It purported to be Bluetooth but the utter lack of any detectable Bluetooth anything made that suspicious. But that’s all with ordinary mics and speakers. Much simpler and more effective to use actual audio transducers to transduce audio.