NFC locks are reaching a tipping point where the technology is so inexpensive that it makes sense to use it in projects where it would have been impractical months ago. Not that practicality has any place among these pages. IKEA carries a cabinet lock for $20USD and does not need any programming but who has a jewelry box or desk drawer that could not benefit from a little extra security? Only a bit though, we’re not talking about a deadbolt here as this teardown shows.
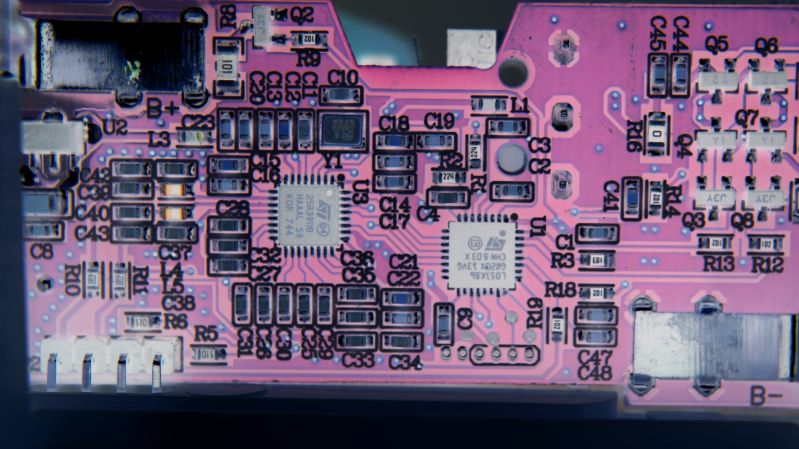
Rothult has all the stuff you would expect to find in an NFC scanner with a moving part. We find a microcontroller, RFID decoder, supporting passives, metal shaft, and a geartrain. The most exciting part is the controller which is an STM32L051K8 processor by STMicroelectronics and second to that is the AS3911 RFID reader from AMS. Datasheets for both have links in the teardown. Riping up a Rothult in the lab, we find an 25R3911B running the RFID, and we have a link to that PDF datasheet. Both controllers speak SPI.
There are a couple of things to notice about this lock. The antenna is a flat PCB-mounted with standard header pins, so there is nothing stopping us from connecting coax and making a remote antenna. The limit switches are distinct so a few dabs of solder could turn this into an NFC controlled motor driver. Some of us will rest easy when our coworkers stop kidnapping our nice pens.
Rothult first came to our attention in a Hackaday Links where a commenter was kind enough to tip us off to this teardown. Thanks, Pio! If this whets your appetite for NFC, we have more in store.















it doesn’t look like that ikea product is very widely released.. looks like just the UK..
I have gotten them from two different US stores.
They are availible in Norway (at least in the web page ikea.no)
According to the Ikea website, my local Ikea in Germany has 43 of them in stock. I did not go to check if that’s true though….
Also sold in The Netherlands. I will get one to play with although I don’t trust anything of value with a wireless lock..
Here is a (US) link to the item.
https://www.ikea.com/us/en/catalog/products/00429619/
Most exciting “AS3911 > NFC Initiator / HF Reader IC”
In the docs it says:
—
The AS3911 includes several features, which make it
incomparable for low power applications. It contains a low
power capacitive sensor, which can be used to detect the
presence of a card without switching on the reader field.
—
Bit confusing :) yet, i haven’t seen before battery powered NFC devices that can last for long. I didn’t think there is “Initiator” chip :) I definitely have to make something with this :D
The mentioned AS3911 is actually the ST25R3911B from STMicroelectronics and is a full blown NFC reader device. You can find out more here: https://www.st.com/content/st_com/en/products/nfc/st25-nfc-rfid-tags-readers/st25-nfc-rfid-readers/st25r3911b.html
Probably uses this sensor to detect when an object is held up to it so it doesn’t have to power and poll the reader field 100% of the time
The connector very obviously has the SWD pins on it. These would be the primary way to reprogram the board and would probably not require boot0 to be touched unless the SWD pins are disabled by the exiting firmware.
So just buy a cheap STLink dongle and you’re all set to reprogram it.
Absolutely correct – Using an STM32 discovery board STLink works perfect, but I never got that far in my writing due to the vacation ending.
Thank you for the mention!
His disassembly/debug story of the Rothult seems to be ongoing, apparently he is (looking into) writing a new firmware for it now, posts on his blog:
https://blognamn.wordpress.com/
You can extend the antenna cable a bit, with coax or just regular cable. But NFC antennas are usually not 50 ohm matched so I think it wouldn’t work for over 1 meter or so.
What do you do, when the batteries run out, while the door is closed?
It beeps at you before batteries run out, and if you don’t replace the batteries it unlocks itself with its last breath.
https://www.ikea.com/hu/hu/manuals/rothult-intelligens-zar__AA-2103153-6_pub.pdf
So a possible attack would be liquid nitrogen, if it is mounted somewhere, were it could be sufficiently cooled to disable the batteries. E.g. in a drawer.
yeah, or you could just use a large screwdriver or a little crowbar to force the thing open.
This thing is more of a convenient tamper proofing against the casual fridge raider or office supplies borrower that a serious security device..
You could extend the battery contacts outside of the cabinet, to a hidden location. If I did that, I would also use protection diodes and a couple capacitors to protect against a high or reverse voltage applied to such contacts.
You’d have to be careful not to freeze the mechanism too. Also, when it loses power, it erases the extra key card data, so it’s still apparent that someone tampered with it.
But what am I talking about, this is a $20 cabinet lock, it’s not designed to be particularly strong or secure. A stern enough look at it is also a possible attack.
Xiaomi also has a similar lock, it features nicer design but also looks more fragile. Oh, yeah, and you use an app to open it. :)
https://m.banggood.com/Xiaomi-Smart-Drawer-Cabinet-Lock-Keyless-Bluetooth-APP-Unlock-Anti-Theft-Child-Safety-File-Security-p-1365478.html?rmmds=search
Yes Yes. An interesting problem. Data security concerns are always more important than ever. Especially if you store important information in the cloud. Suddenly he is hacked. Recently I bought here the https://litslink.com/use-react-native-be-like-jean-claude-van-damme experimental program, which promises to secure data with a 99.9% probability. I want to test the program and write reports on my blog.
Hello – does anyone here have a contact at IKEA responsible for the Rothult Product? Would be great if I could get in touch.
Hello,
I really love these locks but I usually make them open all with the same rfid card for not have to use 10 different cards on my cabinet. This is one of the features I love Rothulst but I would like to have an extra and spare key in case I lose the main one and not having to go back to 10 different keycards, but the locks only allow to program one extra card.
And my problem is exactly there on how to get my main keycard succesfully copyed and having a spare card since I already bought different rewritable cards and a copier and the copyed cards dont get to be recognized on any of the locks.
Can someone please advise on the correct keycards and copier, preferably with links, in order to get this done?
Thank you
NFC (13.56MHz) isn’t a good option for making multiple copies. There is some dark magic with inexpensive tags which allow the UID to be rewritten, but you probably need a $300USD Proxmark just to get started. Low frequency RFID (125KHz) is meant for that sort of thing.
Thanks Brian. I may try once again with another copyer (maybe a lower cost Proxmark) and if I succeed I’ll post it here
Yes please! Good luck, R.
Yeah or an good android phone for $300 which can write the UID to mifare classic clones too ;)
I continued this work, making an Arduino compatible. https://github.com/jetpilot305/Rothult-Arduino