Although we hackers will sometimes deliberately throw away our passwords and then try and hack our own phones / WIFI systems for self amusement, for many people including the actual inventor of the password, Fernardo “Corby” Corbató (1926-2019), passwords have become extremely burdensome and dis-functional.
Sadly, Fernando (according to the internet) died on July 12th, and equally sadly, part of his legacy was the ordeal of his “having a three-page crib sheet to stay on top of his own 150+ passwords”.
We’re all used to being badgered by websites to use complex passwords with a minimum length and a minimum number of upper case characters, lower case characters, numerical digits and non alphanumeric characters AND being told at the workplace to use different passwords than at other places AND to being told to change our passwords regularly. The fact that somebody like Fernando had 150 passwords is not surprising.
However, there is some hope, as according to
The research goes into quite a bit of detail about passwords and concludes that the biggest threat to password security is when criminals obtain data from insecure ‘breached’ sites, in which case it would not matter if your word was written in hieroglyphics, it would be of no consequence at all. Another interesting conclusion was that by making passwords so intractable this encouraged people such as Fernando himself to write them all down, only for someone to rummage through their office desk (technically known as ‘dumpster diving’) and copy them.
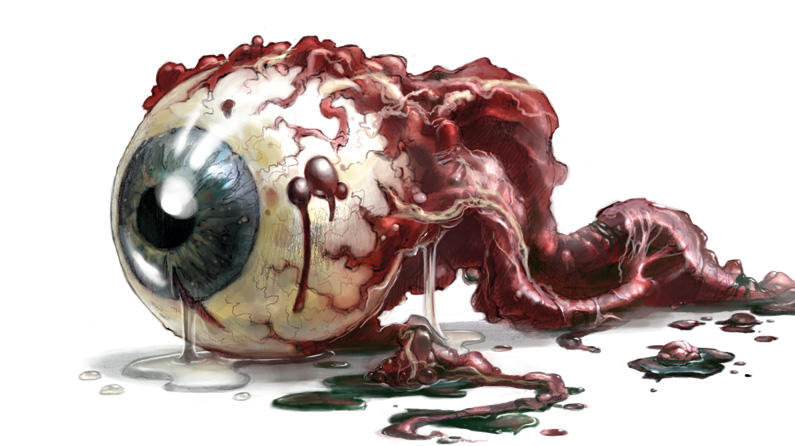
Maybe the end of the password will now swiftly be upon us as technology enables biometrics such as ocular based identifications to be more widely used, but then again we’ve all watched those films where the protagonist scoops the eyeball out of a person’s skull to gain entry to a secure area.
It’s easy to get carried away about passwords and security hype, but it should not be forgotten that Fernardo Corbató was an eminent computer scientist who pioneered ‘Time sharing’ on computers, as detailed in this Hackaday article: Retrotectacular: Time Sharing.















Invented the use of passwords with computers, maybe. I’m pretty sure passwords have been used since we could grunt.
Flintstone unlocking cave.
Proper security. When passwords fail! https://www.youtube.com/watch?v=p0Gwe5gKgjo
I was expecting that clip to be the ED-209 scene from Robocop.
Not only that, but one of Aesop’s fables covers what we’d call two factor identification today. A wolf overhears a lamb being told not to let anyone in who doesn’t know a secret phrase. When the wolf repeats the phrase, the lamb gets suspicious, and asks the wolf to slip his hoof under the door to prove he’s a sheep.
And that approach has the same vulnerability to the dismemberment of an authorised party.
> (technically known as ‘dumpster diving’)
Well…. No. Technically you’re wrong.
I don’t know if there is a term for rummaging through someone’s desk, but dumpster diving is going trhough the trash at a site to gain access to privileged information that was thrown in the regular trash. If you find the cheatsheet with passwords there, you’re in luck, but as long as the password list stays in the office desk, it’s not dumpster diving.
You’re quite possibly correct and it did make me blink when I originally read it. Dumpster diving is normally associated with scavenging for discarded physical objects such as cans of beer and frozen chickens, but could well have a wider meaning within the context of security. I guess we’d need to ask a security expert such as Alex Weinert for clarification on the terminology.
And now you don’t even need to look for thrown away (old) password lists, you can simply look for anything with fingerprints. Generally, the same fingerprint is used for a long time. Not only do you spread around hundreds of copies every day, every previous employer with uses them instead of passwords also has a copy, as do all the recent phones that you previously owned.
Since secure network communication is pretty standard, the only way to steal passwords is breaking into the device where the (unencrypted) passwords are entered. The fingerprint scanner is usually connected to that same device, so it doesn’t really add any security.
Yes, that’s why I suggested eyeballs.
until someone starts pucking out eyeballs of their victims to gain access.
The bank that ask for retina scans will no longer get my business.
I wonder if there would be a way to fingerprint your neutral brain activity…
While I haven’t tried either method, I would imagine that cutting off a person’s finger or hand to gain access through a fingerprint scanner wouldn’t be much more difficult than scooping out their eye to get past a retinal scanner, though it’s probably many times easier just to find an errant fingerprint and gain access by lifting that instead of stealing body parts from people who probably want to keep them.
And now I’m reminded of that Avenger’s scene with Loki.
If you really think that’s better, try replacing “fingerprint” with “eyeball” in jaap’s comment. You’ll notice it all applies just as well to a hypothetical world where we use retinal scans routinely.
Hmmmmmn …… maybe yes ….
of course we don’t leave retina prints on everything we look at like we leave fingerprints on everything we touch. so there’s that…
still not perfect though.
But the identifying parts of the eyeball like the iris appear on every high-resolution photo and are as such even easier to obtain than fingerprints.
A retina scan is more difficult to obtain but also quite annoying to perform due to the bright light needed.
The most likely attack would be a breech of retina scan hash data that’s reversed with a rainbow table attack (these exist).. no need to hunt down someone and scan their eyeballs, just buy a huge database off the dark web and start attacking randos.. this happened in India to 2.8 billion people when the national Aadhar system was breeched.
The issue with biometrics in general is that unlike passwords that can be changed, once your biometric pattern has been obtained, it can never be used to secure anything again. Look at Aadhar, the Indian identification system. Over 2.8 billion people’s biometric data has been stolen from the Aadhar database and sold. Rainbow tables for biometric pattern hashes also exist. The ultimate insult of biometric systems is that they are accurate enough to identify anyone at any time even without their consent, but nowhere near secure enough to benefit the person being sampled and profiled. For example, police have been 3D printing fingers and thumbs from fingerprint records to unlock phones, and now dmv photos are being used to unlock facelocked phones. VivoKey implants that run cryptographic algorithms in vivo is the only solution that has the convenience of biometrics with the power and security of standards based cryptography.
That was the fun thing about Minority Report. Eyeball transplants.
So true – and a point that many people seem to miss. I can’t think of a biometric that won’t be hacked – and when it is hacked will cause more problems than a simple password.. Even if we go to DNA – ie Altered Carbon – it’s not going to be that hard to get someone elses dna and apply that to the device…
‘To rifle/riffle through’ something like a drawer, filing cabinet, or desk, is a term I’ve come across before.
Most often as ‘rifle’, but I think it’s an allusion to shuffling cards, so ought to be ‘riffle’, like the technique, IMO.
It’s the smaller scale, tidier version of ‘tossing’ a room when looking for something.
‘Dumpster diving’ is looking through trash. A more proper term would be ‘snooping’.
Yah; if it wasn’t for him, I wouldn’t currently have 94 passwords for 94 sites.
…everyone see that MS decided to finally ditch the regularly changing of passwords after time in the May update releases as the default thang.
Tis surprising that FB has never opted to force the changing of passwords every days.
* after X time.
* changing of passwords every X days.
I dont think we should blame Fernando, rather the website administrators / designers could more commonly use filters to block the use of all the common passwords like ‘123456’ rather demand hideous complexity from the user.
Administrators shouldn’t be able to see our passwords. They should be hashed and salted. I guess they could filter the hashes for common passwords.
Or God forbid have them agree on a standard for single sign on across sites. But then you can’t have a monopoly on every single facet of technology.
My favorite is sites (usually banks) that for “security” reasons forbid things that actually make your password more secure like length and punctuation.
“Security reasons” in these cases mostly translate to “our backend system was built in the 70s and your web front end is a layer on top of a 3270 terminal emulator”
…from a bank we inherited 3 takeovers ago (ex. midlantic->summit->BOA)
I remember a bunch of 32-character long base-password strings….
Then I derive passwords from those….
considering I remember 7 of those off by heart, I think the 224-character worth of references would take a long time to figure out…. Especially since none are written down…
Then they have to brute force the ordering of the segments of the 7 32-char long passcodes…. (with numbers, letters, special-characters)
Also, I have different passwords for different sites…. I have a low digital footprint (that is, I only use sites I defo need for communication, work, etc…), so for the rest of the sites that are just temporary blips in my life (use wise), I just use burner passwords like “SquarePointer3264” (Yes, go ahead, put that on the passwords list… it could give access to some temp-burner accounts, lol)
Password managers, how do they work?!
I mean seriously, until we have password managers, built into browsers, by default (oh wait….) which sync to other devices (oh wait….) meaning that users don’t have such a hard time anymore, people won’t stop using insecure passwords.
If the W3C etc want to actually do something useful? – Create a scheme in which a password manager program and a website can communicate nicely, without the user intervention that’s currently required. Make the whole thing ‘automatic’ from the moment I sign upto a new site – creating an account, generating and saving that new secure password, and supplying it every time I visit the site, without me having to click specifically into a password field to activate the password manager or something else equally annoying.
Do you mean cookies?
yea how do password managers work? rather poorly as in any minor change on the page and they loose all track of whats going on
Combined with how poorly they deal with any corrections by you. One inevitably ends up with a database clutter with old passwords. And some apps present nothing but the root. e.g. internal sites, meaning password stacking.
Every time I look into password managers I get the same feeling of impending clutter and maintenance. What happens if there is a major update to the manager, will my password file always be compatible/readable, how do I keep it synced between devices without using some 3rd party server?
>multi-factor authentication (MFA)
Unfortunately that means giving up your phone number, street address, and the name of your firstborn to Google. Somebody has to manage these “factors”, such as sending you a text message whenever you want to sign in, and that costs money and loses your privacy.
Password: I have control over it.
2FA: Someone Else (TM) has control over it.
Guess which one I prefer (at least for important things — those random web sites out there are cattle to me, not pets: I tend to use throwaway passwords on those, like pwgen -n 16 and then forget).
In utterly unrelated news: Microsoft is now beneficently offering their own services for:
“…multi-factor authentication (MFA), or great threat detection.”
All you have to do is let them spy on you with that gross, disembodied eyeball pictured above and make Bing your default search engine! And it will never work right because it’s Microsoft!
The literature is full of these discussions, and there is little agreement as to best practice. TFA is strongly in the lead, but biometric has takes a significant hit over the last several years for a number of reasons (including that biometric is forever/unchangable, or it wouldn’t server the purpose, so a compromise is shattering). There are issues with TFA, as well, but it seems to be in the lead.
In the last year I have run into, in my own life, TFA failures due to: spoofed cellphone, system lag timing out the TFA process (at the ATM… this really, really sucked, lead to lockout by the fraud detection scheme, and there was no recourse at the time), biometric factor failure (couldn’t read the fingerprint due to contamination, at work. The contamination was work related), and several others.
I am not cursing TFA, but noting that there is still a good way to go here, and that I really dislike biometrics on theoretical grounds, as well as practical.
TFA by phone is actually a huge breach of privacy, because you have to give a great deal of personal information to third parties, who then get to spy on you whenever you use the authentication.
For example, password lists to access a web bank are/were common. You had a running number, and you’d pick the next code from the list. Only you and the bank knows the list.
Some banks changed that to mobile authentication and -outsourced- the authentication service elsewhere. That means, now a private company in Denmark knows my cellphone number, my account number, and they know whenever I make an online payment or money transfer of any sort. Even worse, if I wanted to use NFC to pay with my cellphone at the cash register, I would have to give up all that information to Google, because my bank uses Google Pay as the payment processor. Now why on earth would I want to do that?
It doesn’t have to be that way. The outfit in Denmark could be made to know just a *hash* of your bank account number along with your phone number. The essential message they need to convey to the bank is that you got the TFA correct or not. They don’t need to know more than what’s necessary to perform the actual TFA act.
It doesn’t make much difference. They still know it’s me, and the time of the transfer. If they’re colluding with somebody else, let’s say Google, they’ll know exactly what I purchased based on the website I visited etc…
UNfortunately, in many cases, there are no other options. If I want to have the bank account, which means if I want to get paid, any access, ATM or online, requires the cellphone for many banks, and seems to be trending to more as time goes on. The biometric is also trending toward unavoidable, as it is being pushed for corporate and site security hard in the US. The reliability is not great.
Any votes for chip in right hand or forehead? ;-)
Only if it’s a VivoKey! dngr.us/hddg
+1
It is only a matter of time before fingerprints and retina scans will be copied and misused, good luck changing yours.
“And what will you use to change password? Sandpaper?”
To change a password you might try to use a keyboard. What do you use to change a (compromised) retina or fingerprint? Just the idea to give, say facebook and others, access to my biometrics makes me sick.
(This isn’t directed at you specifically [visserslatijn])
Please for the love of all that is holy, repeat after me: identification is NOT authentication!
These people need to write that on a blackboard a thousand times after school.
Biometrics are not under a persons control, they can never ever serve as authentication, only identification.
Identification would be akin to your email address or your username, and by intent it is perfectly acceptable for others to know your identification. I couldn’t email you specifically without knowing your email address for example.
Authentication is separate, and proves you are that identification. Only you should be able to authenticate to that email address to read what was sent there.
Using a fingerprint as authentication is no different than using just your email address as proof you are the owner of said email address.
It’s also important to understand identification only needs to be unique within a scope, and the only purpose of changing identification is when that uniqueness fails. Using your full name in a small company as identification is likely fine at first, but once you have multiple “John Smiths” there needs to be a change to uniquely identify each of them separately.
Presuming retina patterns and fingerprints really are as unique as claimed, there wouldn’t be any need to have them changed.
Passwords do suck, and shared secrets generally are not ideal, but they serve a completely different purpose from identification. If we are going to replace passwords as authentication, at the very least let’s replace them with another form of authentication!
The issue isn’t confusion between the two. Using identification to authenticate is fine *PROVIDED* that the identification is “impossible” to falsify.
For “impossible”, read that the cost of the effort exceeds any possible value extracted. In that same meaning, credit card smart chips are “impossible” to clone.
I use a fixed function to generate the password from the server name/id. Each password is therefore unique, so compromising one doesn’t compromise the rest. It’s not useful for people that suck at math, but for techies like me it’s worked pretty well. Here’s a sample function conceptually similar to what I use:
Start with an ‘X’ (some systems require passwords to start with a letter)
Take the hex value of the first two characters of the server’s DNS name. i.e. 6861 for ‘hackaday.com’
Add 4 more fixed characters you can easily remember. i.e. DA42
Using this formula my password for hackaday.io would be: X6861DA42
I’ve been using something conceptually similar for a few years. Recently more and more systems have been adding stupid rules that have forced me into exceptions to the point where my “system” is basically broken now.
Must include upper and lower case.
Must include a special character.
Cannot include one of these special characters.
Had a fun problem at work last week. I had to change my password. There is a tool that changes the password on every system that I need to log in to. (It’s potentially a lot, I work for a company that owns 1/256 of the whole IPv5 space). They have recently changed tge rules to mandate a “special character”.
Several days later I found that a system I use no longer worked. It runs on a remote Linux machine using X-windows and Exceed. Nobody had any idea what the problem was, until on a hunch I changed my password again. It seems that having a “£” in the password was a problem. Windows, Outlook, Exceed itself, even ftp into the remote machine were all fine with it, but one of the deeper layers was apparently not coping with the £ sign. (I swapped back and forth a few times to be sure)
So, we had a system that _requires_ a special character, but that does not work with some special characters.
IPv5?
Either one lower or one higher than 5 makes more sense.
Ah, yes, IP v4. One of the top left quadrant here: https://xkcd.com/195/ (where a small number of companies have bagged more IP space than all of Africa)
i see obscure password complexity requirements as diminishing potential entropy. simply requiring a lowercase letter as a starting point reduces the potential entropy of that character. you can also use password complexity requirements for pattern matching code to help break hashes faster and more efficiently. i think it would be better to simply require longer passwords, a passphrase or even a block of data that need not conform to printable character standards.
i mostly see two/multi factor as a crutch for people with poor password management skills. i personally hate it, especially the requirement to have a phone or multiple email accounts, which means more passwords. i also worry about cascade failures where having one device get compromised allows hackers to break others. like having your phone stolen today can lead to your bank account being infiltrated tomorrow.
One more against biometrics : My mother has almost to no fingerprints anymore, probably due t age they weared off. And the only ATM in the bank she can use is one old machine ( green screen … ) that still works with passwords. Or she has to endure long lines … And of course, the young dumb interns that try to help people do no understand this kind of problem … “lets try another finger…. clear the finger and try again …. ”
Also, I do not like the use of biometrics for things out of our control. Too much of it remembers me of that scene in Demolition Man, with Stallone & Snipes.
Maybe, for some things, we need to revisit **why** do we need too much logins and passwords. It seems that many sites ( Youtube, news sites, ec ) just use logins because they want to be able to profile its users and use the email details to spam us.
TRUST. Or about as close as we can without bodily dragging you there.
I loathe TFA. Logging in used to be a simple matter of typing in my password. Now for work I have to have apps installed on my personal phone to generate token codes and/or keep walking from my office to a window where I can get a signal so I can receive the message with my new code. All this after changing passwords on a regular basis that our all complicated and 14+ characters. I’ll be working along merrily then suddenly I have to reauthenticate and hope my phone is right there.
Here’s an idea. How about I continue to do my job by not telling anyone my password, and they hire competent IT folks who don’t keep password laying around in plain text for hackers to steal.
Reading this article and all of the comments leads me to believe that the very biggest problem of all is the one that nearly all of these companies that require ever more and more convoluted passwords refuse to deal with: Their own ridiculously insecure systems. Instead of punishing their users, these companies/web sites should be investing in protecting them instead. One should be able to trust their personal information with these places.
… What? Why is everyone laughing?
In other words, I won’t hold my breath. I have realized that in life there is a vast difference between what should be and what actually is. This is especially true when dealing with companies that only care about their shareholders, not their customers.
While I’m only partly onboard with your rant, I fully agree with what the actual threat to your password-protected account is: incompetence / mismanagement of the password database by the company that you’re logging in to.
Sad to see the article quote Microsoft touting 2FA/MFA.
I travel a lot and find that sites with 2FA let me down when I need them most. I’ve yet to encounter a 2FA implementation that can or will work with a phone when overseas. It seems like these systems are all designed and written by kids in the Bay Area who spend so much money on their iPhones and avocado toast that they can’t afford to travel.
CapitalOne is a particularly egregious example. Their system refuses to text to an overseas number, or to a US number overseas, or to a virtualized US number, like google voice.
Exactly, but you need to emphasize the point about control: identification is involuntary; authentication is, and should always be, a voluntary act. Going to an ATM and withdrawing cash should require a conscious choice on my part as to whether or not I authorize the transaction. Providing access to information locked in my phone should require a conscious choice on my part. Authorization should not be automatic.
I’m hoping Steve Gibson’s last four years working on SQRL will take off and it gets adopted. Check it out. No more passwords. No more server side information to be stolen.
https://www.grc.com/sqrl/demo.htm
Alright, I’ll say it: I found the feature image for this article disturbing in a way I don’t expect to see on Hackaday. I’d rather see this site remain gore-free, please.
Good luck getting a retina scan out of the unfortunate disabled person who has lost their eyeballs (or never had them in the first place) for whatever reason… or a “fingerprint” off a quadruple amputee… or a “voice” fingerprint off someone who has got a sore throat (or is mute)…
These people exist, we are required to cater for them.
Plus, fingerprints get left everywhere unless you’re in the habit of wearing gloves 24/7, and there’s no guarantee your biometric data will be disposed of once you leave a particular site/organisation.
Then there’s false positives/false negatives to consider and equipment costs.
As for other forms of biometrics… what next, pull your trousers down and scan the inside of one’s sphincter muscle? No thanks!
I think the “something you have” is more reliable for the really important stuff. It’s not like someone banks with 150 banks on a regular basis. Maybe there’s a market for a device that can act as a OTP device for multiple places so you’re not carrying hundreds of tokens with you.
Otherwise I’ll just rely on my P2P password manager (GnuPG+git) thanks. Fernando may be gone, but while I still have to interact with sites that require password changes every few weeks and one that expects a 6 character password (without special characters/case insensitive no less!) I don’t think his legacy is going anywhere.
About 10 years ago, My other bank on the other hand, show me my pre-selected picture after I entered the user account number. That at least reduces the chance of a phishing scam. I had a very hard time explaining to my main bank that their idea of asking me for two passwords won’t help. And yes, the lady taled about passwords showing up as *** and don’t understand the reasoning of classic spy countersigns.
My main bank imposed the 2FA tied to SMS without any opt out or more reliable 2FA hardware token. The ATM swallowed my card on a trip and I had no way of accessing my account on their phone banking without a card. At least I was able to cancel the card. Even my investment brokage have gne the crappy SMS 2FA route.
The phone service here is horrible, so I don’t bother paying $50 a month to just use it for 2FA. Even if I had one, I would use local SIM card anyways. Getting the mobile stolen is gameover for these type of 2FA.
Next time before my trip, I probably have to set up a VPN server at home and VPN into my LAN to avoid the mess.
I’m not so sure the eyeball harvester is a protagonist…
It doesn’t seem to the best picture to illustrate the content
“..the biggest threat to password security is when criminals obtain data from insecure ‘breached’ sites..”
Seems to be very true according to guys that crack billions of passwords https://medium.com/@ScatteredSecrets/how-to-crack-billions-of-passwords-6773af298172.