The home may be the hearth, but it’s not going to be a place of safety for too long.
With the abundance of connected devices making their ways into our homes, increasing levels of data may allow for more accurate methods for remote surveillance. By measuring the strength of ambient signals emitted from devices, a site can be remotely monitored for movement. That is to say, WiFi signals may soon pose a physical security vulnerability.
In a study from the University of Chicago and the University of California, Santa Barbara, researchers built on earlier studies where they could use similar techniques to “see through walls” to demonstrate a proof-of-concept for passive listening. Attackers don’t need to transmit signals or break encryptions to gain access to a victim’s location – they just need to listen to the ambient signals coming from connected devices, making it more difficult to track bad actors down.
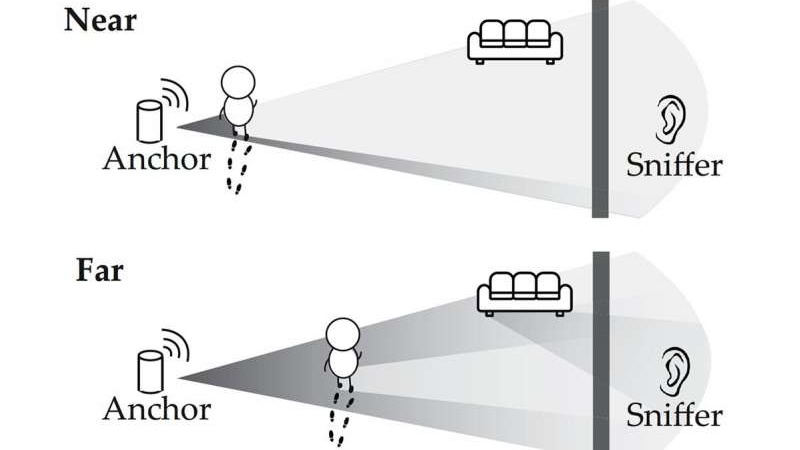
Typically, connected devices communicate to an access point such as a router rather than directly with the Internet. A person walking near a device can subtly change the signal propagated to the access point, which is picked up by a receiver sniffing the signal. Most building materials do not block WiFi signals from propagating, allowing receivers to be placed inconspicuously in different rooms from the access point.
WiFi sniffers are relatively inexpensive, with models running for less than $20. They’re also small enough to hide in unsuspecting locations – inside backpacks, inside a box – and emit no signal that could be detected by a target. The researchers proposed some methods for safeguarding against the vulnerability: insulating buildings against WiFi leakage (while ensuring that desirable signals, i.e. signals from cell tower are still able to enter) or having access points emit a “cover signal” that mixes signals from connected devices to make it harder to sniff for motion.
While we may not be seeing buildings surrounded by Faraday cages anytime soon, there’s only going to be more attack surfaces to worry about as our devices continue to become connected.
[Thanks to Qes for the tip!]















WiSee
https://www.youtube.com/watch?v=VZ7Nz942yAY
This seems like something that’s only relevant if you’re being hunted by mossad and it would be super easy to mitigate by randomly adjusting signal strengths on your wireless transmitters and switching various antenna pairs on and off to change the signal bounce patterns over time.
I would be more concerned about how to make people to stop using the same trivial passwords everywhere for all their online accounts.
Found a typo: “connectedd”
Hurray….
We have a winner in the “find the typo” contest.
Congratulations, you can now collect your award from the gift shop.
“we may not be seeing buildings surrounded by Faraday cages anytime soon”
Foil insulation isn’t common in America, but it certainly is in other countries. Normally it’s designed/installed to minimise any Faraday cage effect, but you can certainly use it to make a building that gives poor reception.
No, it is just unnecessary annoying to the reader of the comments (at least for me) to find comments about spelling or grammar mistakes or even obvious plain typos. In most cases the error does not hinder correct understanding of the text and my brain “autocorrects” it, most often in a way, that I even forget that it was there. And then some idiot has to write about it and I have to think “oh, here was an error. Was it important? Lets go back and look”
So: Anybody who finds an error should keep it for himself.
That’s nice of your brain. I’m not a native English speaker (or writer) and sometimes minor typos or grammar mistakes throw me for loop trying to decipher specific sentences.
I didn’t notice this one nor would it have disrupted me but still.
And I assume that an above average percentage of HaD readers have some (mild) OCDs.
haha… +1
But to be honest, I don’t care about the spelling mistakes. I care about the article. Although It might be considered helpful by some to point other people’s mistakes, it might also be considered by many others that it is slightly disrespectful to the person who wrote the article. And the negativity surrounding it gives me bad vibes. Keep in mind that there are many things done in order to write this article, lot’s of things went right, lot’s of effort was put into the writing or research. And when all is finished and it is published… all the commenter(s) can say is something like “I found a mistake in the spelling”, not, “wow what a great article”, not “thanks for the info”, nope, just a ” Found a typo: “connectedd” ”
Somebody typed one D too many, who cares, the world is on fire and all we care about is spelling?
Be honest, do you type everything 100% correct? Nope, nobody does, because we are human. If you want to bitch about something then concentrate on the content of the article, this way we can all learn from it. Pointing out that somebody typee one ‘d’ too many does not contribute to something positive in any way.
PS: for those who want to, feel free to find the mistakes in my comment, I’m sure there are lots. But it’s hard to type with tears in my eyes as these grapes are indeed a bit too sour for my taste.
You are allowed to keep it, especially keep it for yourself.
It’s really not that tragic to point out some fixes. A developer/engineer/etc. shouldn’t mind that, as long as this isn’t the only kind of feedback.
Wow, good for you. You are so special. Just like everybody else.
Thanks. Fixed.
interesting stuff, but from a practical point of view, what’s new.
Homes have windows… homes have lights… light shines through windows… obersvers outside home monitor shadows or silhoutettes. Technically the only change between wifi and visible light is that wifi uses a lower frequency.
And you have more – and less obvious – windows for that range.
Could it be possible to find voids inside the Great Pyramid with this methodology ?
Based on the inscriptions, those light reflecting dishes used to light up the tomb in “The Mummy” are 802.11, so it sounds feasible.
https://thumbs.gfycat.com/GrossFearfulHarborporpoise-mobile.mp4
Now we just need to get ESP8266s/ESP32s to pull off this trick, and you’ve got yourself presence detection in your home automation set-up. Perhaps a burglar alarm too.
Check out the Nzyme WiFi project. It’s a passive monitoring framework which has a pretty gray log front end. I use it to keep tabs (for fun only) on who’s in my area. Think passive forensics + deauth/evil clone detection plus more based on the alerts you specify
I can see if some one is on my couch right now by looking at the signal reported by the sonoff (esp) behind the couch.
20% drop in signal when some one sits on the couch.
I’m trying to figure out what’s news here. We’ve had radar since WWII, and 2.4 GHz is well known as a frequency that works well for radar. I have a pair of Eimac 2.4 GHz “radar” vacuum tubes from the 1960’s in my collection, so to me that’s proof that people have been using 2.4 GHz for radar for at least the last 50 years.
How is this anything other than one more slightly interesting (and only useful to dark operators) thing that can be done with radar? The only thing that’s new here, IMHO, is the fact that so many of us are using 2.4 GHz radios in our homes to sling data off into the ether, basically lighting our homes up like a Christmas tree at radar friendly frequencies.
Uh, because it’s not radar? My stereo produces audible sounds but that doesn’t make it sonar.
It’s a type of RF direction finding though, which has also been around forever.
Isn’t it? The first UK attempts at radio direction finding that became radar were using the aircraft reflected or shadowed signals from the Alexandra Palace BBC transmitter IIRC, passive detection rather than active pinging.
YDRC.
a. that’s not passive because the BBC shortwave transmitter was transmitting as part of the experiment; my AM/FM radio does passive detection
c. the phenomenon of EM radiation being reflected was demonstrated by Hertz in the 1880s
c. you’re describing a POC experiment built on later work done by Marconi, Hülsmeyer, and Watt
One ping only, Vasily.
Sorry Milo, RW is spot on. I was about to make the same comment. Initial ‘radar’ was conceptualized on just what he stated, in that observations where being noted by receivers tuned to a existing transmitter. If you are old enough to remember analog over the air TV, you yourself may have observed picture flutter caused by a aircraft flying overhead.
Possibly the confusion is that initial experiments were passive, but showing some promise the BBC later allowed use of the transmitter for active type experiments.
In what universe is using a spark gap to create EM “passive”?
Analogy:
passive sonar, just listening, no pinging
active sonar, pinging and listening for the return.
In “passive” radar, where does the EM come from? The BBC transmitter makes it active ipso facto.
Okay so if the sun is illuminating what you see, it’s passive, if you’re holding the flashlight and pointing it at what you want to see, it’s active. If someone else is holding the flashlight and pointing it at what they want to see, but you can use scattered or serendipitously pointed light to see what you want to see it’s passive again.
So, if you are in not in control of the flashlight, BBC transmitter, it’s broadcasting regular programming, it’s passive, if at a later date you are, that’s active. But later using the same transmitter or flashlight actively does not mean that prior passive use is made retrospectively active.
And I’m not saying anything about spark gaps that’s all you.
“Passive” as in the signal is already there, i.e. the WiFi AP the article discusses. There is a spelling thread you might also want to join.
OKay, show me where my understanding is wrong:
Passive: the object to be detected emits the signal by which the object is to be detected
Active: the object to be detected is slapped with a signal whose return is used to detect the object
Seeing objects by flashlight? Active.
Seeing objects illuminated by sunlight? Also active
Smelling objects” Passive
The argument some folks are using here seems to be “The signal comes from a different building therefore it’s passive.”
“And I’m not saying anything about spark gaps that’s all you.” No, that’s Marconi. He did work in this area. Hertz, Marconi, and Watt laid the foundations not just for radio but radar specifically.
““Passive” as in the signal is already there” Unless you’ve perfected time travel, the signal has to be “already there” for you to detect it. No need to be Mr. Insulting Guy, Jeff King.
Active, the seeker emits the rf that then bounces off the target for detection.
Passive, the seeker relies on RF emitted by other sources to detect the presence of the target.
Simpler definition: Can an enemy aim an rf seeking missile at your emissions while you look for the target? If so, active. If not, passive.
“The only thing that’s new here, IMHO, is the fact that so many of us are using 2.4 GHz radios in our homes to sling data off into the ether, basically lighting our homes up like a Christmas tree at radar friendly frequencies.”
Never underestimate the power of ubiquitousness. The surveillance state wouldn’t be the same without it.
Nobody has to go anywhere near your house really, it’s probably possible to derive all this data from a beamforming router with 3 or more antennas (After compromise, full pwnage)
Cell towers and now I suppose WIFI too can be used to paint the sky to reveal with this type of passive third party device, what are called stealth aircraft. This a game changer!
With ground penetrating radar the US military can make an autonomous truck go up to 60MPH (100kMPH) by matching the patterns with a previous mapping of the area. No roads, no camera, no GPS, and snow cover or fog.
Again, this is NOT passive, and stealth aircraft can already be detected by some current radars.
Serbs shot down a U.S. stealth fighter back in the 1990s.
I’m not saying it was Tesla, but it was Tesla!
‚Most building materials do not block WiFi signals from propagating…‘ in the far east?
Didn‘t know that, really.
https://www.kaspersky.de/blog/watching-through-walls/5763/
Learned something new, thanks.
My signal gets blocked by my fireplace wall and the metal framed doors in my office. I have to use repeaters to get signal beyond those spots, plus outside.
For using the wifi as actual wifi it’s probably that straight line signal is attenuated enough that the crappy 3dB if you’re lucky, device antenna can’t distinguish between that and the multipath echoes etc, so timing is screwed and it refuses to connect. Quite often you’ll still get a connection if you force device back to a 2Mbit 802.11b mode or something but if you leave it on auto, it keeps stepping up and losing it.
Doing some back of envelope spitballing, and using the technique that if you want an answer on teh interwebs, just say it completely wrong and someone will correct you…
So in an old b mode at 2Mbit you’re basically needing 2 million symbols a second to get through and that’s approx 500ns a symbol, and we can use the approximation of a nanosecond a foot, that means bounced multipath from 100 feet around you isn’t really gonna throw it off much, that’s a super big path length difference, and those signals will be too weak to pose much discrimination problem. However, if we crank it up to g speeds, now we’re at around 20 ns a symbol, may start seeing some problems if your LOS path is attenuating as much as stuff that’s bouncing off a wall and taking 20ft further to get there. Then n speeds, 150 and 300Mbit, you start wondering how they work at all when you’ve got around 7ns and lower per symbol, which is why I guess they got into multiple antennas and beamforming.
Something, Something, Quarter Wavelength… mutter… mutter…
My house has steel siding.
I had to put my router in the attic to get the signal to go through the shingles rather than the siding so it could reach my detached garage.
I use google fi for my phone service partly because it does voice and texts over wifi so it works in the house.
I live in a faraday cage, even if it wasn’t intentional.
This no news, you find research paper and example implementations using the AP as Sender and Listener to implement a kind of radar. By limiting the air-time of this ‘radar’ it is possible to co-exist with WiFi (limiting the throughput). Intended use for such a thing would be Smart-home applications. Fortunately this did not made it to market.
The legal implications selling a device that gives you the possibility to monitor your neighbors/people through walls killed the thing, afaik, By construction limiting the range of such a soho-radar on your own lawn is hard, when putting the end-user in charge is not sufficient. In addition it is hard, in terms of device set-up for a common soho-customer, to give precise positions as a result.
But with your leftover old WiFi devices you can hack yourself interesting things, e.g. https://people.csail.mit.edu/fadel/papers/wivi-paper.pdf – remember: more antennas!