In a recent blog post Google announced that the early access phase of its Android Developer Verification program has commenced, as previously announced. In addition to this new announcement Google also claims to be taking note of the feedback it has been receiving, in particular pertaining to non-commercial developers for whom these new measures are incredibly inconvenient. Yet most notable is the ’empowering experienced users’ section, where Google admits that to developers and ‘power users’ the intensive handholding isn’t required and it’ll develop an ‘advanced flow’ where unverified apps can still be installed without jumping through (adb) hoops. Continue reading “Android Developer Verification Starts As Google Partially Retreats On Measures”
device security5 Articles
WiFi Hacking Mr. Coffee
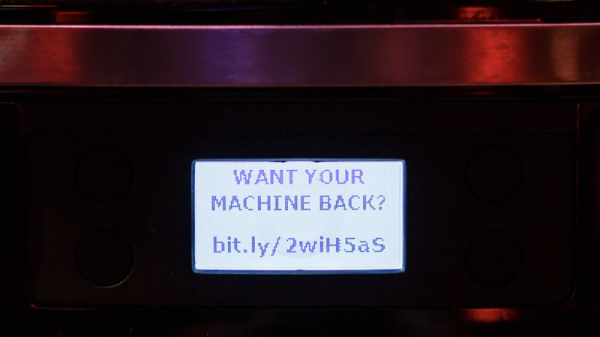
You wake up on a Sunday, roll out of bed, and make your way to the centerpiece of your morning, the magical device that helps you start your day: the coffee machine. You open the companion app, because everything has an app in 2020, and select a large latte with extra froth. As you switch open a browser to check Hackaday, the machine beeps. Then the built-in grinder cranks up to 100, the milk frother begins to whir, and the machine starts spraying water. Frantic, you look at the display for an error code and instead see a message instructing you to send $75 to a bitcoin wallet, lest your $300 machine become a doorstop.
Outlandish though it may seem, this has become quite a real possibility, as [Martin Hron] at the Avast Threat Labs demonstrates. In fact, he could probably make your modern macchiato machine do this without setting foot in your house (so long as it comes with a built-in ESP8266, like his did).
Building on others’ work that identified the simple commands that control the machine over it’s WiFi connection (nothing says “brew me a nice cup o’ joe” like 0x37), [Martin] reverse-engineered the Smarter Coffee companion app to extract and reverse engineer its firmware. He was actually able to find the entire firmware image packaged within the app- relatively uncommon in the world of Over-The-Air (OTA) updates, but convenient in this case. Using Interactive Disassembler (IDA) to sift through the firmware’s inner workings, he identified the functions that handle all basic operations, including displaying images on the screen, controlling the heating elements, and of course, beeping. From there, he modified the stock firmware image to include some malicious commands and ran an OTA update.
The mind-boggling part here is that not only was the firmware transmitted as unencrypted plaintext over unsecured WiFi, but the machine didn’t even require a user to confirm the update with a button press. With one quick reboot, the trap was set. The machine operated normally, while waiting for “Order 66,” causing it to turn all the heating elements on, spool up the built-in grinder, and beep. Constantly.
While a broken coffee machine seems relatively innocuous, there are some pretty significant lapses in hardware/firmware security here that, while avoidable, almost seem unnecessary in the first place. It makes us wonder- why does Mr. Coffee need a smartphone in the first place?
Your WiFi Signals Are Revealing Your Location
The home may be the hearth, but it’s not going to be a place of safety for too long.
With the abundance of connected devices making their ways into our homes, increasing levels of data may allow for more accurate methods for remote surveillance. By measuring the strength of ambient signals emitted from devices, a site can be remotely monitored for movement. That is to say, WiFi signals may soon pose a physical security vulnerability.
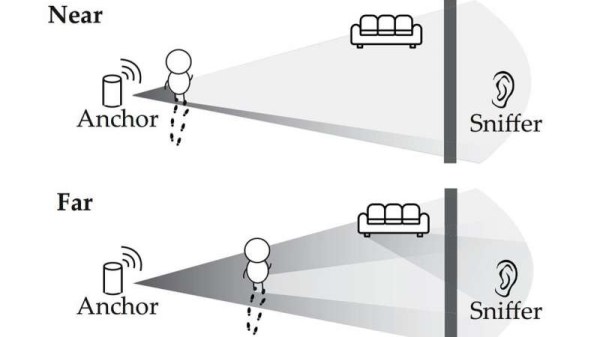
In a study from the University of Chicago and the University of California, Santa Barbara, researchers built on earlier studies where they could use similar techniques to “see through walls” to demonstrate a proof-of-concept for passive listening. Attackers don’t need to transmit signals or break encryptions to gain access to a victim’s location – they just need to listen to the ambient signals coming from connected devices, making it more difficult to track bad actors down.
Typically, connected devices communicate to an access point such as a router rather than directly with the Internet. A person walking near a device can subtly change the signal propagated to the access point, which is picked up by a receiver sniffing the signal. Most building materials do not block WiFi signals from propagating, allowing receivers to be placed inconspicuously in different rooms from the access point.
WiFi sniffers are relatively inexpensive, with models running for less than $20. They’re also small enough to hide in unsuspecting locations – inside backpacks, inside a box – and emit no signal that could be detected by a target. The researchers proposed some methods for safeguarding against the vulnerability: insulating buildings against WiFi leakage (while ensuring that desirable signals, i.e. signals from cell tower are still able to enter) or having access points emit a “cover signal” that mixes signals from connected devices to make it harder to sniff for motion.
While we may not be seeing buildings surrounded by Faraday cages anytime soon, there’s only going to be more attack surfaces to worry about as our devices continue to become connected.
[Thanks to Qes for the tip!]
Teardown Of USB Fan Reveals Journalists’ Lack Of Opsec
Last month, Singapore hosted a summit between the leaders of North Korea and the United States. Accredited journalists invited to the event were given a press kit containing a bottle of water, various paper goods, and a fan that plugs into a USB port.
Understandably, the computer security crowd on Twitter had a great laugh. You shouldn’t plug random USB devices into a computer, especially if you’re a journalist, especially if you’re in a foreign country, and especially if you’re reporting on the highest profile international summit in recent memory. Doing so is just foolhardy.
This is not a story about a USB fan, the teardown thereof, or of spy agencies around the world hacking journalists’ computers. This a story of the need for higher awareness on what we plug into our computers. In this case nothing came of it — the majority of USB devices are merely that and nothing more. One of the fans was recently torn down (PDF) and the data lines are not even connected. (I’ll dive into that later on in this article). But the anecdote provides an opportunity to talk about USB security and how the compulsion to plug every USB device into a computer should be interrupted by a few seconds of thoughtfulness first.
Continue reading “Teardown Of USB Fan Reveals Journalists’ Lack Of Opsec”
France Proposes Software Security Liability For Manufacturers, Open Source As Support Ends
It sometimes seems as though barely a week can go by without yet another major software-related hardware vulnerability story. As manufacturers grapple with the demands of no longer building simple appliances but instead supplying them containing software that may expose itself to the world over the Internet, we see devices shipped with insecure firmware and little care for its support or updating after the sale.
The French government have a proposal to address this problem that may be of interest to our community, to make manufacturers liable for the security of a product while it is on the market, and with the possibility of requiring its software to be made open-source at end-of-life. In the first instance it can only be a good thing for device security to be put at the top of a manufacturer’s agenda, and in the second the ready availability of source code would present reverse engineers with a bonanza.
It’s worth making the point that this is a strategy document, what it contains are only proposals and not laws. As a 166 page French-language PDF it’s a long read for any Francophones among you and contains many other aspects of the French take on cybersecurity. But it’s important, because it shows the likely direction that France intends to take on this issue within the EU. At an EU level this could then represent a globally significant move that would affect products sold far and wide.
What do we expect to happen in reality though? It would be nice to think that security holes in consumer devices would be neutralised overnight and then we’d have source code for a load of devices, but we’d reluctantly have to say we’ll believe it when we see it. It is more likely that manufacturers will fight it tooth and nail, and given some recent stories about devices being bricked by software updates at the end of support we could even see many of them willingly consigning their products to the e-waste bins rather than complying. We’d love to be proven wrong, but perhaps we’re too used to such stories. Either way this will be an interesting story to watch, and we’ll keep you posted.
Merci beaucoup [Sebastien] for the invaluable French-language help.
French flag: Wox-globe-trotter [Public domain].