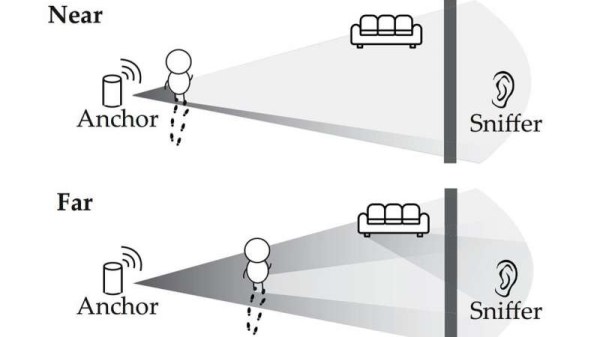
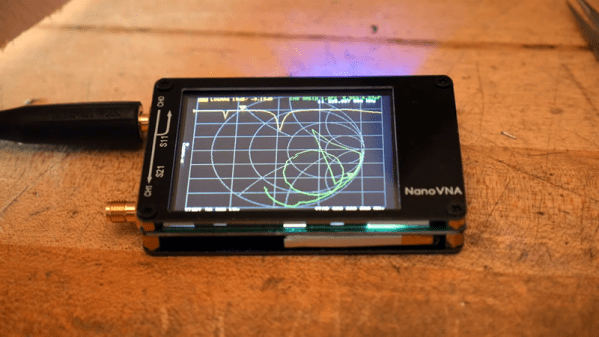
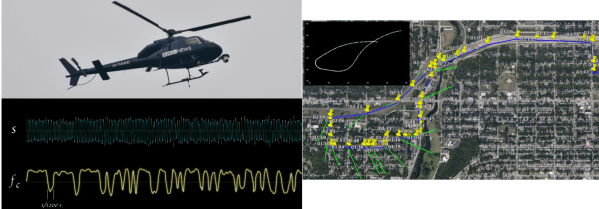
Signals and systems theory is a tough topic. Terms like convolution and impulse response can be hard to understand on a visceral level and most books that talk about these things emphasize math over intuition. [Discretised] has a YouTube channel that already has several videos that promise to tackle these topics with “minimum maths, maximum intuition.” We particularly noticed the talks on convolution and impulse response.
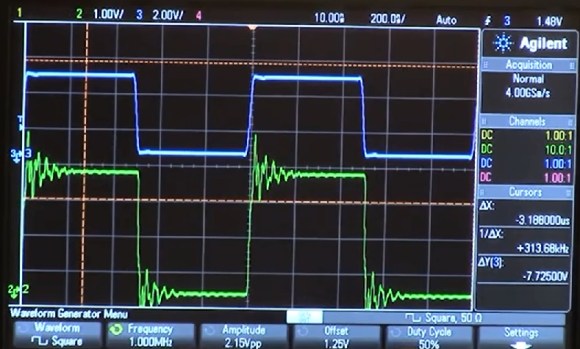
We think that often math and intuition don’t always come together. It is one thing, for example, to know that E=I times R, and power is I times E, but it is another to realize that a half-watt transmitter delivers 5V into a 50Ω load and that one watt will take just over 7V into that same load.
The example used is computing how much smoke you can expect to create by setting off fireworks. We presume the math models are notional since we imagine a real model would be pretty complex and involve things like wind data. But it still makes a nice example.
If you don’t know anything about the topic, these might not be the right ones to try to learn the basics. But we do applaud people sharing their intuition on these complex subjects.