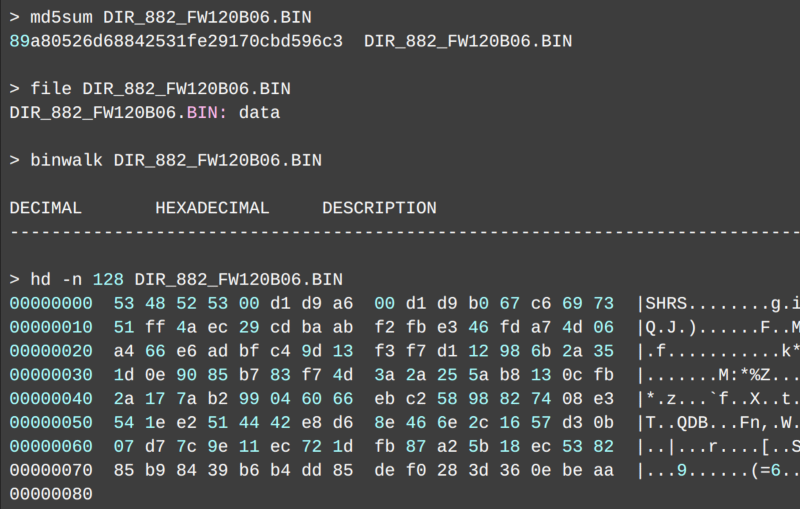
When [0xRickSanchez] found some D-Link firmware he couldn’t unpack, he was curious to find out why. The firmware had a new encryption method which was doing its job of preventing tampering and static analysis. Of course, he had to figure out how to get around it and is documenting his work in a series of blog posts.
Looking at the entropy analysis showed the data to be totally random, a good sign it was either encrypted or compressed. The target router cost about $200, but a similar cheaper router used the same encryption and thus this model became the hardware of choice for testing.
A console cable provided access to the router and an executable named imgdecrypt immediately caught his eye. Moving that file to a regular PC allowed the usual attack to see how it does its job.
You can follow along with part 2 which is in 2 different parts. The end result is on GitHub, but — honestly — the real adventure is in the story of how it came together.
We spend a lot of time thinking about reverse engineering things like this. We aren’t always looking at routers, either.















How ignorant can a network hardware company be. There will always be a guy who cracks your consumer device and reverses your FW. If you just make it open to begin with AND take bug reports from the community you can produce a better product. It’s not like routers are a super secret device at this point.
Ditto that
Very impressive, and I’m so envious. I wish I had kept up with my hacking skills.
The word “tampering” is pejorative, suggesting that there’s something wrong with changing the firmware on hardware that you own. I suggest “improvement”.
That could be said of any hardware (except for rental). Might hurt the resale value though since not everyone believes in your “tampering” skills.
I mean, tampering *is* a serious concern. I agree that you should have the right to access the firmware, but the downside is that someone malicious can tamper with your router firmware. Imagine a shady Amazon seller that installs a password sniffer on every router they sell before sending it on to you. There *should* be some sort of firmware verification mechanism in place, ideally one that an expert user can disable and install their own modifications on but with a prominent warning that the device is unverified firmware.
D-Link sucks though, so instead they take the minimum effort approach here.
Flash your own firmware when you receive the device?
To some extent, every firmware is unverified firmware.
How bizarre because I just ran across this project a few days ago! Encrypted firmware seems like a bad idea because it makes D-Link employees (and their families) a target for criminals who want the encryption key.
You watch too much spy movies.
Like they are the nuclear launch codes.. Still made me smile though. Half imagined a movie with Liam Neeson….
Criminal: “give us the key or else!”
Dlink employee: “why wont you believe me? I already told you its 123456789!”
That one was too long to type and required shift to be used, we shortened it to ‘dlink’
Speaking of D-Link, does anybody know of a FOSS firmware for their old DSC-G900 WiFi cam? I like the hardware, but the stock firmware is now old and, IIRC, doesn’t support modern streaming and cloud services.
I probably can’t be the first to notice this… but… ” Contains public.pem and the imgdecrypt binary from their root fs” That’s gonna get him in trouble. :(
Not to mention the -K and the -iv…. Sony anyone?
Great work! (really)