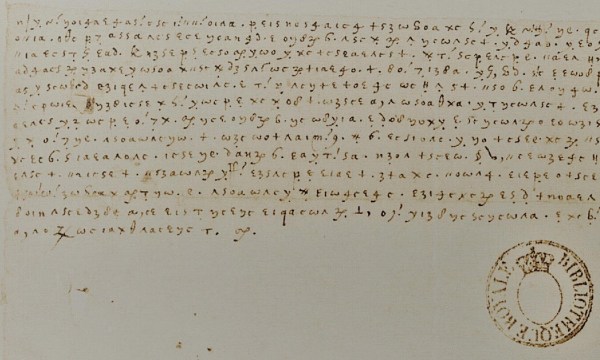
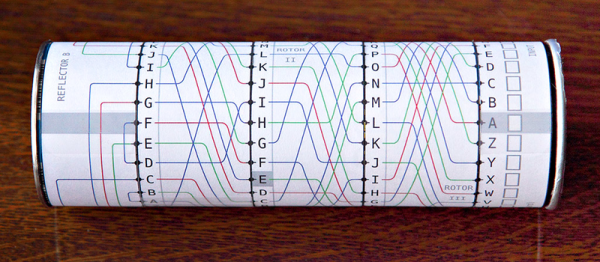
Communications by important people over the past thousands of years have been regularly encrypted, making the breaking of this encryption both an essential and also a fascinating historical field. One recent example of an important historical discovery by codebreakers are letters dating back to 1578 through 1584 by Mary Stuart, the Queen of Scots in the 16th century. While deemed lost for centuries, researchers came across them in a stash of encrypted letters that were kept at the Bibliothèque nationale de France’s (BnF). After decrypting these 57 letters, they realized what they had come across.
Even in digitized form, they could not simply be OCRed, leaving the researchers to manually transcribe each character into the software they used to assist with the decrypting. Only during the decrypting process, they began to realize that these were not Italian communications – matching the rest of the collection of which they were part – but in fact letters by Mary and her allies. Of the 57 letters, 54 are from Mary to Castelnau, the French ambassador in London at the time.
Supporting evidence for these decrypted letters being from Mary and Castelnau came from British archives, which had clear text versions of some of the encrypted letters, dated to the years when a mole within the French embassy was leaking translated texts to the English, as part of the usual political pastime during those centuries of getting onto thrones and making other people leave them. Mary’s attempt to become not only the Queen of Scots but also Queen of England came to a tragic end with her execution in 1587 after a politically motivated show trial.
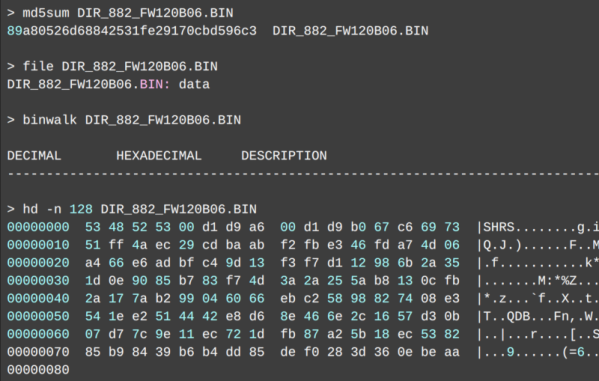
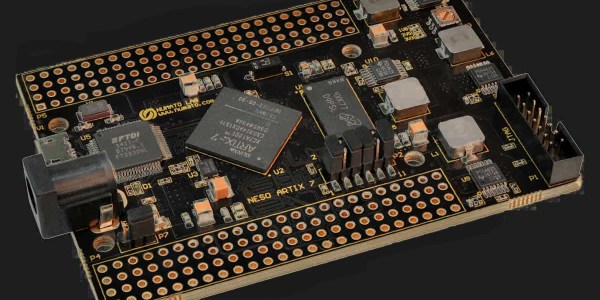
The software the researchers used primarily is called CrypTool 2, which is an open-source project that provides cryptoanalysis and related functionality. The access to the documents themselves was enabled via the DECRYPT project, resources which taken together enables virtually anyone to undertake such historical sleuthing from the comfort of their own home.
(Thanks to [Stephen Walters] for the tip)