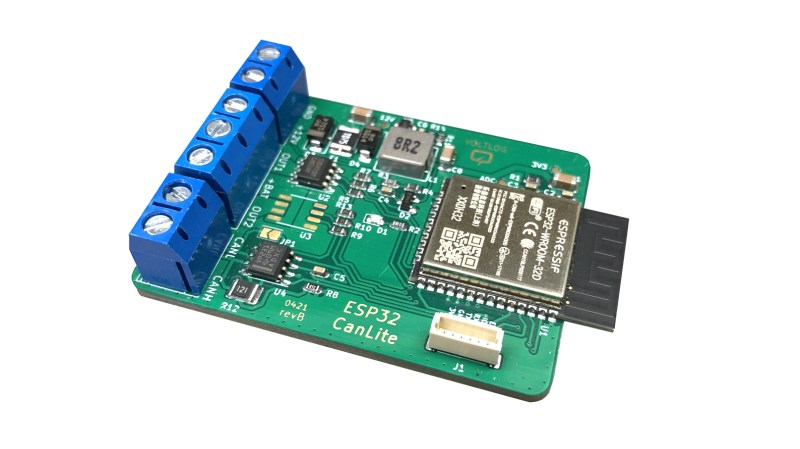
[Voltlog] has been hacking away at the CAN bus console of his VW Golf for quite some time now. Presumably, for his projects, the available CAN bus interface boards are lacking in some ways, either technically and/or price. So [Voltlog] designed his own wireless CAN bus hacking and development module called the ESP32 CanLite (see the video below the break). The board was tailored to meet the needs of his project and he claims it is not a universal tool. Nevertheless we think many folks will find the features he selected for this module will be a good fit for their projects as well.
In his introduction of the design, he walks through the various design decisions he faced. As the project name suggests, he’s using the ESP32 as the main controller due to it’s wireless radios and built-in CAN controller. The board is powered from the car’s +12V power, so it uses a wide input range ( 4 to 40 V ) switching regulator. One feature he added was the ability to switch automotive accessories using the ST VN750PC, a nifty high-side driver in an SO-8 package with integrated safety provisions.
The project is published as open source and the files can be pulled from his GitHub repository. We noticed the debug connector labeled VOLTLINK on the schematic, and found his description of this custom interface interesting. Basically, he was not satisfied with the quality and performance of the various USB-to-serial adapters on the market and decided to make his own. Could this be a common theme among [Voltlog]’s projects?
A word of warning if you want to build the ESP32 CanLite yourself. While [Voltlog] had intentionally selected parts that were common and easy to purchase when the project began, several key chips have since become nearly impossible to obtain these days due to the global parts shortage issue (it’s even out of stock on his Tindie page).
If you want to dig deeper into CAN bus hacking, check out this talk that we wrote about back in 2016. Do you have any favorite CAN bus development boards and/or tools? Let us know in the comments below.















Great project, would also be a nice fit for boaters with their NME2000.
Too bad its ST VN750PS (sic!) seems to be made from unobtanium, as quite a lot of automotive grade ICs.
NMEA*
With a few mods it could be used with the TJA1050 as well.
@Chris Lott said: “[Voltlog] has been hacking away at the CAN console of his VW Golf for quite some time now.”
I doubt [Voltlog] has been hacking away “at” the Controller Area Network (CAN) bus [1] in his VW, the CAN bus is an open standard (ISO 11898-X, ISO 16845-X) and plug-and-play chips and firmware exists for easily communicating with the CAN bus. What he’s probably hacking away at is what’s being carried on the CAN bus, the vehicle’s On-Board Diagnostic Codes (OBD) or Diagnostic Trouble Codes (DTC) [2], and that can be a tough job sometimes.
While some OBD codes (actually OBD-II these days) or DTC codes can be common, every automobile manufacturer can make their codes secret and/or proprietary. This where the hard part comes in, the Volkswagen-Audi Group (VAG) is quite secretive when it comes to some of their codes. Even the name of their OBD-like codes is different, they are called “VAG Diagnostic Trouble Codes”. “Generic OBD-II scanners aren’t recommended because they often will not show a (VAG) fault code even when a DTC code is stored in one of the modules.”[3]
I do not know how VAG handles this proprietary VAG DTC situation in places that have Right to Repair (RTR) laws, but I can envision fees and/or subscriptions required to access the information, plus fees associated with VAG certifying whether a device is interpreting their codes properly. Maybe that’s why the scanners I see that specialize in VAG codes are so expensive. For example see the prices of the Ross Tech VAG-COM Diagnostic System (VCDS) products.[4][5] And maybe that’s why [Voltlog] is hacking away over (not at) his VW’s CAN bus.
* References:
1. CAN bus
https://en.wikipedia.org/wiki/CAN_bus
2. On-board diagnostics
https://en.wikipedia.org/wiki/On-board_diagnostics
3. How to read VW fault codes
https://www.youcanic.com/guide/read-vw-fault-codes
4. VCDS (software)
https://en.wikipedia.org/wiki/VCDS_(software)
5. VCDS (VAG-COM Diagnostic System) Products
https://www.ross-tech.com/vag-com/
https://store.ross-tech.com/shop/cat/VCDS/
Automotive networks are far more complex than OBD – although they are required to support that for diagnostics they also use their own custom protocols for communication between ECUs and deeper diagnostics (usually UDS these days).
The UDS interface is what tools like VCDS will use and getting access to that is one challenge, but some partial or full databases do exist and some professional tools can support UDS on multiple marques.
The CAN protocol/architecture used between ECUs is what most want to reverse engineer (in passenger vehicles it’s proprietary and no manufacturer I’ve heard of makes this available to anyone except it’s OEMs) and this would include controlling windows and switches to airbags and the engine, indeed most vehicle functions. This is an incredibly complex job and the sort of thing this sort of device is very useful for.
Can bus is like ethernet, it is the physical layer, when it was said “[Voltlog] has been hacking away at the CAN console of his VW Golf for quite some time now.”, what would have been more accurate would have been “decoding and reverse engineering the protocol”.
As someone who reverse engineers automotive computer systems even different trim levels of the same model can have variations in scaling factors ( there aren’t floating point numbers is basic can protocols) and even message format.