USB devices are now ubiquitous and, from an information security standpoint, this is a terrifying prospect as malicious software can potentially be injected into a system by plugging in a compromised USB stick. To help get some piece of mind, [Cesare Pizzi] created USBValve to help expose suspicious USB activity on the fly.
The idea behind USBValve is to have the onboard microcontroller advertise itself as a storage device, pretending to have a filesystem with some common files available. When an unknown USB device is first inserted into the USB port on the USBValve tool, USBValve displays usage information, via the attached OLED screen, on whether the USB device is accessing files it shouldn’t be or immediately trying to write to the filesystem, which is a clear sign of malicious behavior.
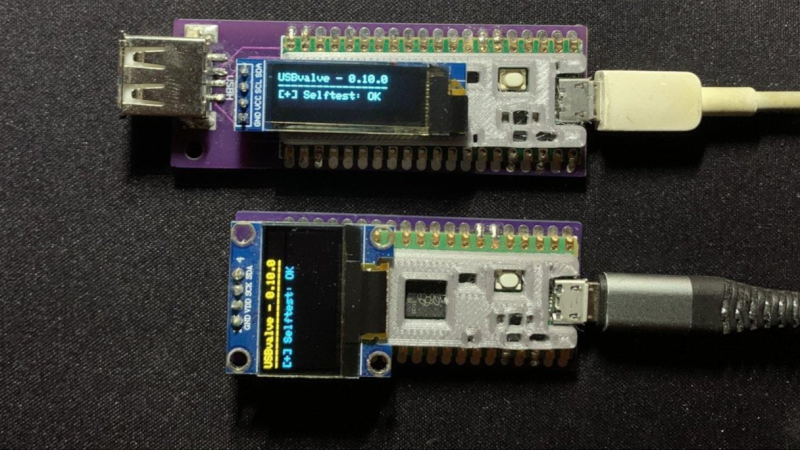
The USBValve hardware is a straight forward composition of a Raspberry Pi Pico, an tiny I2C OLED screen and an optional PCB carrier board with a 3D printed spacer. The software uses Adafruit’s Tiny USB library along with the SSD1306AsciiWire library to drive the OLED display. And it’s all open source, including the code and PCB design files.
There’s a lot of security fun to be had with USB, from DIY dirt cheap Rubber Duckies to open source hardware Rubber Duckies, to discussions on the BadUSB exploits. The simplicity of the USBValve project allows it to be low cost, easy to use and can provide concise, critical information for a variety of real world threats.
After the break, be sure to check out [Cesare Pizzi]’s talk about USBValve at the SCC Insomnihack conference which has a wealth of information on how it fares against some known malware attacks, discussions on some of its shortcomings and potential avenues for improvement.
Thanks to [watchdog] for the tip!















Would be nice to have one of these that restricts a device to a single type (e.g: A USB Drive cannot become a mouse later on). Then you could log both malicious hosts and badusbs. Could also make a tester that acts as a virtual USB host and logs all traffic from a client device, so you could take a BadUSB and leave it sitting there for an hour.
The single type thing could be implemented at the driver level. Every motherboard could have one or two dedicated host ports for mice & keyboards, and the others could all be handled on a per-device basis, asking the user for confirmation each time a new type of USB endpoint appears on a port.
It could, but isn’t. Simpler as an end user to create a single device dongle
The second paragraph is a little unclear in my opinion.
The USBValve can act either as a device or as a host
– as a device it can detect if a malware, on the host is connected to, is trying to write something to the fake drive
– as a host it can detect BADUSB devices.
This IS a small Pi connected via USB cable…this can be a very good thing for monitoring any shady cable HOWEVER a small Pi can also write and deploy malware. Host or device, the underlying hardware has no bias, pick your poison. Many such ‘gadgets’ are often made, produced, and sold with good implications but of course…hackers gonna…HACK! ;)
yes, but this is not the case ;-)…being completely opensource you can get your firmware, check, modify and compile…no hidden tricks here, you have the complete control ;-)
Just over explaining the value of mitm
Not sure If I’m getting this correctly, what you say is exactly how it works:
– USBvalve (the version with the host port version) can actually acts as virtual USB Host and it’s capable to take a BadUSB and wait for input for minutes/hours/forever :-)
– From the other side it can acts as USB Drive and monitor all READS and WRITES on it
Is it susceptible to a KillerUSB? If not, can it identify the threat to other devices?
Never tested to be honest. Chances are that it will be destroyed, so you can use it as a sacrificial device ;-) since its cost is few bucks.
But I’ll try to test it, interesting point. Thanks.
A “KillerUSB” does nothing else than killing the computer with too much voltage…
Yes – the USBvalve is susceptible to a KillerUSB and also will be killed – but not your computer…
By the way: hell these KillerUSBs got cheep meanwhile…