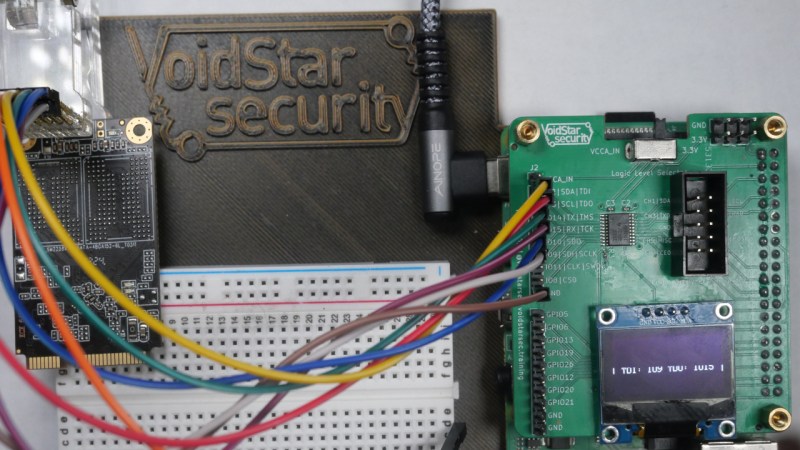
[Matthew “wrongbaud” Alt] is well known around these parts for his hardware hacking and reverse-engineering lessons, and today he’s bringing us a JTAG hacking primer that demoes some cool new hardware — the PiFEX (Pi Interface Explorer). Ever wondered about those testpoint arrays on mSATA and M.2 SSDs? This write-up lays bare the secrets of such an SSD, using a Pi 4, PiFEX, OpenOCD and a good few open-source tools for JTAG probing that you can easily use yourself.
The PiFEX hat gives you level-shifted bidirectional GPIO connectors for UART, SPI, I2C, JTAG, SWD and potentially way more, an OLED screen to show any debugging information you might need, and even a logic analyzer header so that you can check up on your reverse-engineering progress.
 The suggested software workflow pulls no punches either, proposing ease-of-use features like USB-Ethernet gadget mode and Jupyter notebooks. [wrongbaud] shows us how to find JTAG among the dozen testpads left on the SSD, get the SSD single-stepping through code, and dump some of its memory space as a test. Full of tricks of the trade like reverse-engineering devices on a sheet of paper you can leave markings on, this write-up gives you a solid background in JTAG hacking, even if you only have a Pi and an old SSD.
The suggested software workflow pulls no punches either, proposing ease-of-use features like USB-Ethernet gadget mode and Jupyter notebooks. [wrongbaud] shows us how to find JTAG among the dozen testpads left on the SSD, get the SSD single-stepping through code, and dump some of its memory space as a test. Full of tricks of the trade like reverse-engineering devices on a sheet of paper you can leave markings on, this write-up gives you a solid background in JTAG hacking, even if you only have a Pi and an old SSD.
So how can you get your hands on one? [wrongbaud] says the plan is to open source both the PiFEX hardware and software in the near future. Until until then, it looks like at least the hardware it wouldn’t be too hard to re-implement it yourself if you wanted to get the hang of reverse engineering with the Raspberry Pi.
[Matthew “wrongbaud” Alt] is a good friend of Hackaday community. He’s stopped by to host a reverse engineering Hack Chat, and ran a HackadayU class on Ghidra. His reverse-engineering journeys are always an informative read, from using arcade machines as a Linux hacking primer, to hacking a cryptocurrency wallet through glitching attacks.















Enterprise SAS SSD drives have a tiny connector on the front, I’m curious if those are related.
A lot of old school hard drives have serial consoles for debug (first one I encountered was on a 20MB Conner IDE drive way back when they were a huge amount fo storage), Seagates famously had a bug which bricked some drives and the recovery used that console.
I’d be surprised if there weren’t at least some SSDs with them too, if you can lay hands on one why not try it out, never know you might even end up featured on HaD?
Go-jtagenum is a rewrite of jtagenum, which is a rewrite of Arduinull. Always wanted to make a web interface for it on top of an esp8266, but now Jupyterlab does it:
https://github.com/cyphunk/JTAGenum
https://github.com/zoobab/arduinull
ohhh nice! is fun to see personal projects grow into something else down the line =D