The concept of cryptography touches our lives many times per day, and that’s probably a conservative estimate. We have a pretty good idea of how it works, having dealt with public-key cryptography for things like remote git repositories or ssh tunneling without a password. But we still enjoyed reading [Tiberiu Barbu’s] primer on the subject which he calls From 0 to Cryptography.
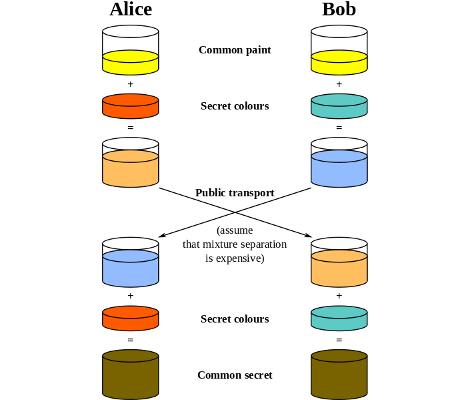
He begins the discussion with a definition of terms but quickly moves to the topic of key distribution. If you’re using a key to decipher data, how can you make sure that key only makes it to the person whom you want reading the data? One way is to use a Diffie-Hellman key exchange. The diagram above illustrates the trade, which uses an agreed upon value (color in this example) as a common starting point, then goes from there. After working our way through the key exchange scenario [Tiberiu] then runs the gammut of other options, include Public-Key, RSA, Hash, Digital Certificate, and a few others. It’s not a long post considering how many topics it covers. If you don’t have time today, make sure to save it for the weekend.
[via Reddit]










