[via Digg]
[via Digg]
Mozilla coder [Aza] is connected to the past and the present: he wanted to celebrate the release of Firefox 3, but pines for the days when one could use small amounts of code to make compelling art. As a way of addressing both things, he has released ContextFree.js, a javascript port of [Chris Coyne]’s Context Free Art. Users can visit Algorithm Ink, where they can draw various compelling designs with just a few lines of script. ContextFree.js compiles the scripts and turns them into visually arresting geometric designs. Users can also browse through designs made by others, easily save them as JPGs, or even modify them by adding their own bits of code. What’s more, it’s not out of the question to use this to generate random images on a website, creating a unique visual experience for every single visitor. You all know what we want to see, though: JavaScript gurus working some real magic with this. Better yet, said gurus can play around with the core open-source code and make something truly their own on the most fundamental level. Definitely check out the video above to get an idea of how easy this is.
[via Waxy]
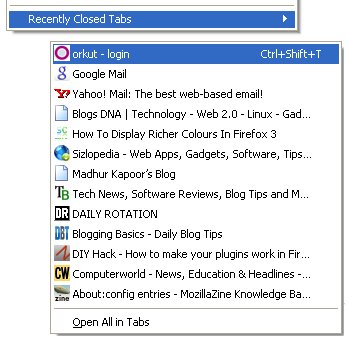
Plenty of USB storage keys are on the market, but Ironkey is the first to use military level encryption. Sold in 1GB, 2GB, and 4GB sizes, the key features a processor called the Cryptochip, which uses Public Key Cryptography ciphers linked to an online account to create encryption keys on the hardware. A Federal Information Processing standard 140-2 compliant true random number generator on the Cryptochip ensure that encryption keys are extremely secure and totally random.
Ironkeys come in different sizes, but there are also three different versions, each with unique features. The basic version has a very James Bond-esque feature to destroy the data on it in case of an emergency. The personal version is loaded with Firefox 3 with various addons that make browsing encrypted and anonymous. The enterprise version is made to order with no specific price on the IronKey site, just a form to order one built to your specifications. All of them support Windows, OS X, and a large amount of Linux distros, and they all come in tamper proof and water resistant cases with a brushed metal finish. We tend to think this level of security is overkill for the average person, but people can’t seem to get with our freewheeling approach to security; remember, we leave our WLAN open.
[via LinuxDevices]
TippingPoint’s Zero Day Initiative reported a critical vulnerability affecting Firefox 3.0 yesterday. It includes the 2.0 versions as well. It’s unreleased and Mozilla is working on a fix already. Whatever the exploit is, it does require the user to visit a malicious site or click a link to executed. It came in 5 hours after the FF3 release, but since it affects previous versions, we wonder if the researcher was just sitting on it to be first. The Zero Day Initiative pays researchers for the exploits they submit.
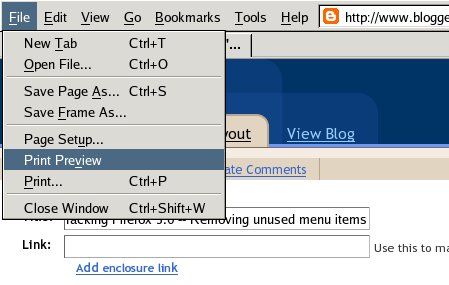
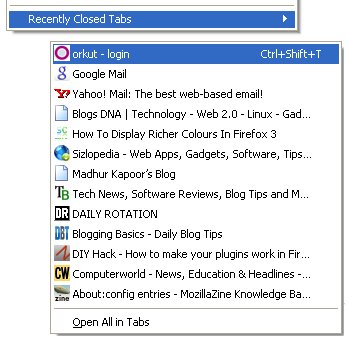
[Nick] sent in his quick hack for getting rid of extra menu options in Firefox 3, like the ever useless ‘Work Offline’ option. (OK, maybe modem lovers like it…) If you’re tired of seeing cluttered menu choices that you never use, [Nick]’s simple trick of editing the XML formatted XUL files in Firefox to clean things up. There’s some risk involved, but it’s nothing that a quick re-install can’t repair. The writeup includes a basic introduction to the XML tags, so you can probably do it. You can use a text editor right? (Just don’t forget to have the installer or a backup copy handy before you start playing around.)
[youtube=http://www.youtube.com/watch?v=mZTJbsUcdeU&hl=en&rel=0&color1=0x3a3a3a&color2=0x999999]
In honor of Firefox 3.0 download day, Waxy.org has posted the full Code Rush documentary. It spans March ’98 to April ’99, as the Mozilla team publishes the first source code and then the eventual AOL acquisition of Netscape. Embedded above is a short clip of [Jamie Zawinski] pushing the code live at 10AM on March 31, 1998. The hour documentary is well worth watching.
If you’re unsure about moving from FF2 to 3, MultiFireFox still works perfectly fine with the new release.

It’s five hours till the official release of Firefox 3. We know your hands are sweating in anticipation, waiting to click that download link and contribute to the greatest World Record known to man… What? You don’t want your browser to have all the notoriety afforded to fat twins? Well then, let’s just go grab the file now since they’re already on the mirrors.
First, pick out a mirror from the official list. Navigate to the the directory of the Firefox 3.0 release: /pub/mozilla.org/firefox/releases/3.0/ You’ll be greeted by a message that says, “We’re not quite ready yet!” and that “Downloading them directly can harm our ability to distribute Firefox efficiently.” Also, you won’t be in the world record count. Think about that, jerk. All releases are named using a consistent pattern. Looking at an earlier release you can determine that the Mac version of 3.0 will be named: Firefox 3.0.dmg Add on the OS and language directories and it will look like this: /pub/mozilla.org/firefox/releases/3.0/mac/en-US/Firefox%203.0.dmg
You can find out more about the new release by reading Dria’s Field Guide to Firefox 3.