Collective human consciousness is full of imagined or mythical dream-like utopias, hidden away behind mountains, across or under oceans, hidden in mist, or deep in the jungle. From Atlantis, Avalon, El Dorado, and Shangri-La, we have not stopped imagining these secret, fantastical places. One of these, Xanadu, is actually a real place but has been embellished over the years into a place of legend and myth, and thus became the namesake of an Internet we never got to see like all of those other mystical, hidden places.
The Xanadu project got its start in the 1960s at around the same time the mouse and what we might recognize as a modern computer user interface were created. At its core was hypertext with the ability to link not just other pages but references and files together into one network. It also had version control, rights management, bi-directional links, and a number of additional features that would be revolutionary even today. Another core feature was transclusion, a method for making sure that original authors were compensated when their work was linked. However, Xanadu was hampered by a number of issues including lack of funding, infighting among the project’s contributors, and the development of an almost cult-like devotion to the vision, not unlike some of today’s hype around generative AI. Surprisingly, despite these faults, the project received significant funding from Autodesk, but even with this support the project ultimately failed.
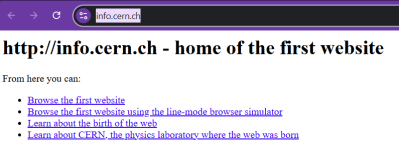
Instead of this robust, bi-directional web imagined as early as the 1960s, the Internet we know of today is the much simpler World Wide Web which has many features of Xanadu we recognize. Not only is it less complex to implement, it famously received institutional backing from CERN immediately rather than stagnating for decades. The article linked above contains a tremendous amount of detail around this story that’s worth checking out. For all its faults and lack of success, though, Xanadu is a interesting image of what the future of the past could have been like if just a few things had shaken out differently, and it will instead remain a mythical place like so many others.