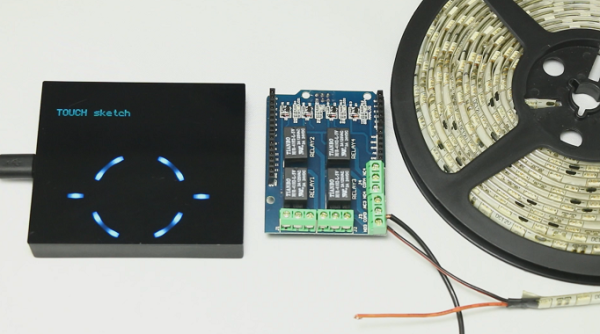
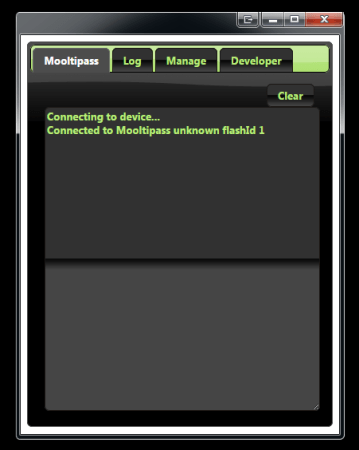
For a little less than a year open source enthusiasts from all over the globe got together to work on an open source offline password keeper. We narrated our progress here on Hackaday and always asked our readers’ opinion when critical decisions were to be made.
Today, the wait is finally over: the Mooltipass crowdfunding campaign finally arrived.
In some of our Developed on Hackaday series posts we noticed that it was tricky for us to convey the benefits of the device we were developing. The first 3 minutes of our video therefore explain good security practices and how the Mooltipass can help users with their credentials security. For our readers that may not have followed our adventure since its beginning, the campaign’s text will provide them with a simple (yet detailed) explanation of what the Mooltipass can do. Finally, our geeky readers will find at the end of our write-up a few links supporting our claims. We would have liked offering cheaper pledges but we unfortunately need to hire professional javascript developers to finish our app & extension.
Our Mooltipass Developed on Hackaday series therefore come to an end. We would like to thank you for your support and hope that you enjoyed seeing an idea materialize into a crowdfunding-ready product!