Work on HaDge – the Hackaday con badge, continues in bits and spurts, and we’ve had some good progress in recent weeks. HaDge will be one conference badge to use at all conferences, capable of communicating between badges.
Picking up from where we left off last time, we had agreed to base it around the Atmel D21, a 32-bit ARM Cortex M0+ processor. To get some prototype boards built to help with software development, we decided to finish designing the HACK before tackling HaDge. HACK is a project that [Michele Perla] started that we have sort of assimilated to act as the prototyping platform for HaDge. We wanted a compact micro-controller board and hence opted for the SAM D21E – a 32 pin package with 26 IO’s.
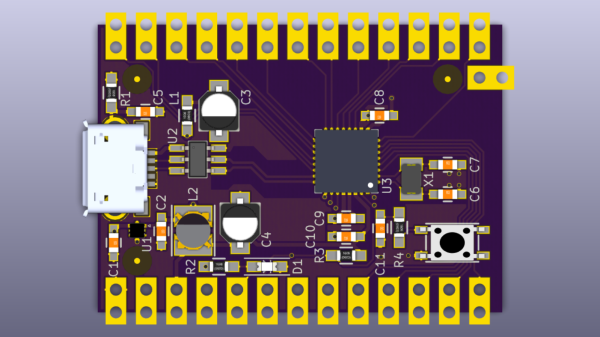
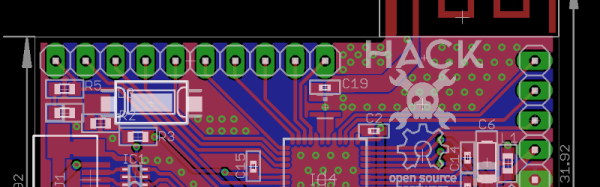
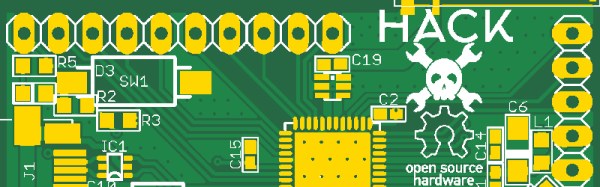
[Michele Perla] had earlier designed HACK based on the larger 32 pin SAM D21G and used Eagle to 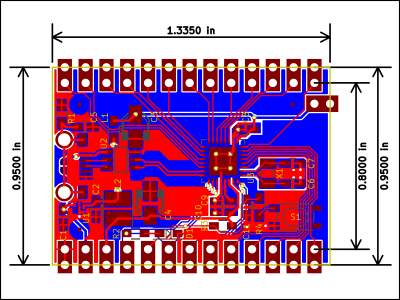 draw the schematic and layout. Using the Eagle to KiCad script, he quickly converted the project and got on to making the board layout. I took up the rear guard, and worked on making his schematic (pdf) “pretty” and building up a schematic library of symbols. While [Michele] finished off the board layout, I worked on collecting STEP models for the various footprints we would be using, most of which I could get via 3dcontentcentral.com. The few I couldn’t were built from scratch using FreeCAD. The STEP models were converted to VRML using FreeCAD. Using [Maurice]’s KiCad Stepup script, we were able to obtain a complete STEP model of the HACK board.
draw the schematic and layout. Using the Eagle to KiCad script, he quickly converted the project and got on to making the board layout. I took up the rear guard, and worked on making his schematic (pdf) “pretty” and building up a schematic library of symbols. While [Michele] finished off the board layout, I worked on collecting STEP models for the various footprints we would be using, most of which I could get via 3dcontentcentral.com. The few I couldn’t were built from scratch using FreeCAD. The STEP models were converted to VRML using FreeCAD. Using [Maurice]’s KiCad Stepup script, we were able to obtain a complete STEP model of the HACK board.
HACK is now ready to go for board fabrication and assembly. We plan to get about 20 boards made and hand them out to developers for working on the software. The GitHub repository has all the current files for those who’d like to take a look – it includes the KiCad source files, PDFs, gerbers, data sheets and images. The board will be breadboard compatible and also have castellated pads to allow it to be soldered directly as a module. Let us know via group messaging on the HACK project page if you’d like to get involved with either the software or hardware development of HaDge.
In a forthcoming post, we’ll put out ideas on how we plan to take forward HaDge now that HACK is complete. Stay tuned.