Most people tend to enjoy a certain modicum of privacy. Aside from the data we all share willingly on the web in the form of forum posts, Twitter activity, etc., people generally like keeping to themselves.
What would you think then, if you found out your iPhone (or any iDevice with 3G) was tracking and logging your every movement?
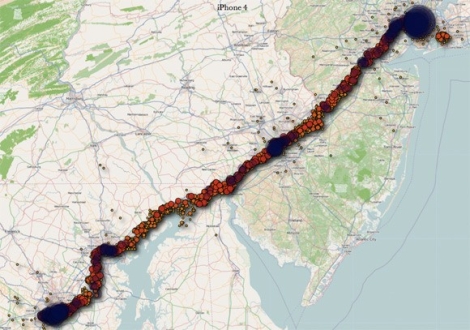
That’s exactly what two researchers from the UK are claiming. They state that the phone is constantly logging your location using cell towers, placing the information into a timestamped database. That database is not encrypted, and is copied to your computer each time you sync with iTunes. Additionally, the database is copied back to your new phone should you ever replace your handset.
We understand that many iPhone apps use location awareness to enhance the user experience, and law enforcement officials should be able to pull data from your phone if necessary – we’re totally cool with that. However, when everywhere you have been is secretly logged in plaintext without any sort of notification, we get a bit wary. At the very least, Apple should consider encrypting the file.
While this data is not quite as sensitive as say your Social Security number or bank passwords, it is dangerous in the wrong hands just the same. Even a moderately skilled thief, upon finding or swiping an iPhone, could easily dump the contents and have a robust dataset showing where you live and when you leave – all the makings of a perfect home invasion.
Continue reading to see a fairly long video of the two researchers discussing their findings.
[Image courtesy of Engadget]
[youtube=http://www.youtube.com/watch?v=GynEFV4hsA0&w=470]















So exploiting this vulnerability requires physical access to a jailbroken iPhone, and people are complaining about lack of encryption?
*Think* gang.. if the apps that use location services want access to the information in the cache, they’ll need to decrypt it, yes? That means they’ll need a key, yes?
That key will be stored (wait for it).. ON THE PHONE.. you know, the jailbroken one the attacker has physical access to, and whose filesystem he’s already scraped to get the location cache in the first place?
Seriously, when your panties are twisted so tight they cut off the oxygen to your brain, it’s time to stop talking.
this is irresponsible of Apple. If they’re going to collect the info with user’s permission, then why create these massive archives of it where Blackhats can get to it? They should upload the most recent info and delete the rest. Geez, Apple, way to endanger your users.
This is great! Now start pulling in the call girls and cross reference their data with the homes (or data) of congressman and MP’s… Wait. Forget call girls. Try male prostitutes and ‘straight, married’ MP’s…
@mstone
It’s not only on the device, it’s also in your backups on iTunes.
The problem is the fact that they’re doing this without telling anyone, and having the data recorded and easily available on both the phone and your backups (which are stored on your computer), all unencrypted…
So no, it doesn’t only require physical access to the device, they can also get it from any computer you have iTunes installed on and plugged your iPhone into… And even still, encryption on the phone (and backups on the computer(s)) would still be an extra layer of protection that the attacker may not know how to bypass, because lets face it, it doesn’t take a genius to extract the file needed, it’s dead simple, so having some type of encryption is better than having everything in plain text.
I suggest that the next time you decide to post, you actually think for a moment and possibly watch the video and read the article… Ohterwise, it’s you who needs to stop talking.
Personally I can think of tons of cool things I can do with this kind of data about myself, data that it would be tedious or expensive to collect any other way.
I am not self centered enough to be under the delusion that my geospatial history is valuable enough to anyone to go to the trouble of stealing it, and lawful access to it is of no concern to me.
Sadly though I don’t own an iPhone, and I suspect the pointless moral outrage will result in apple eliminating this or encrypting it in a way beyond my reach before I could build up a useful dataset.
I just want a spoofing app to fill the database with huge amounts of data copied from the worst charles dickens novels.
To the guys who are against the police accessing data the phones of criminal suspects, quite frankly you are wrong.
If a guy is pulled in a suspision of murder, rape or crimes against children, I would prefer the police to take his phone and get the proof. Rather this than let him go free to commit more crimes.
The only reason I could think for someone wanting to hide this kind of data from the police would be if they were the people commiting such crimes?
Seriously chumps you are ok with law enforcement having the power having the power to pull you over at a traffic stop and download every where you have been. The have the ability to to do this. They are already doing this in Wisconsin. “We’re cool with that.” indeed. for you leftys out there imagine religious nuts have taken over and are making sure you are attending church and not associating with any known homosexuals. As for right-wing pro-law enforcement types out there imagine that the new socialist government has outlawed religion. My point is before handing the government new power imagine that the group that worries you most has taken control of the government and imagine how they might misuse it. Remember all of the new anti-terrorism laws, they are now being used for different things. Obama’s Justice department is discovered it likes these new powers.
Yet again an excellent reason to laugh at Apple. Simple devices for simple people. If the products would be known to steal your wallet at night, people would still buy them.
@holly_smoke – Correct! I totally object to my location being continually tracked and stored, and also to the police being able to take this information without reason. This is because I am a paedophile and murderer, and such data tracking will invariably curtail the pursuit of my hobby.
I will now get rid of my iPhone and get a Kiddy Fiddler Safe Nokia.
“Two Apple users meet in the park … Apple knows this.”
@holly_smoke sorry, it’s the other way round: The police won’t find one and check his phone. They will check all phones (guess who has access to the data) and find some evil guys.
Who cares, people check in to foursquare and facebook places everywhere they go, leave their gps location on their twitter posts, allow half the apps they install to report their location… if you don’t want your location known, maybe you shouldn’t walk around with a radio device that’s constantly transmitting it’s location to towers… let alone a gps device that’s doing the same.
Haha, all those BS-made-for-TV ‘oh it’s to capture kiddy fiddler’, in reality it’s used to fuck up ‘enemies’ of sony and supporters of wikileaks and people at the pentagon who speak out against illegal actions.
And that’s just the western users, what if you had an iphone in one of those shifty countries in the middle east? Or in asia or a former soviet state? Nice to have the data to find the meeting places of any rebellion and rub your opponents out isn’t it..
And @simon it’s not a few locations, it’s every damn location every few seconds after installing the iOS update, and it’s copied to new iphones if you use the restore after losing one, so it’s every few seconds for as long as you have an iphone, ten and tens of thousands of locations over many many many weeks.
And yeah many people will find it neat to have and use that data, but in actuality there are no apps that do use all that stuff, and you aren’t given the damn option to determine if you are such a person, nor given the option to delete stuff if you feel it might be compromising.
Most GPS units also have the tracking but it’s always a setting so you can turn it off and you can delete the data easily because it’s made available clearly and is known to the user.
You daily life is NOT one of servitude to the holy state and its minions.
And the US is NOT (officially) a totalitarian state, just so you know.
Police are downloading this and more from phones, without a warrant. Not just iPhones either.
http://news.cnet.com/8301-17938_105-20055431-1.html
how do the cell networks NOT keep logs of which towers your phone has contacted at what time and with what db signal? Every single cell phone is tracked in real time and can be displayed on an interactive map, probably with a little moving avatar with your mug on it. Child’s play sheople.
@m1ndtr1p
i’m quite aware, that android doesn’t do this by default, AND it’s not hidden as in iOS.
i found the talk, actually: http://events.ccc.de/congress/2009/Fahrplan/events/3600.de.html
as far as i know, skyhook is built into googles android as well and should be off by default. But it’s a “feature” … and let’s face it…if it’s a feature, most people will turn it on.
Nobody mentions how accurate this data is, I think that if the researchers actually did a full job and looked at this they would find that the geographic area included in the file is huge.
For instance my cleaned and restored iPhone contained information about a cell tower 22KM away and I hadnt even left my office with it. It also contained Wifi data that covered 1KM in radius.
At no point has anyone ever explained how the data contained in consolidated.db translates into real life usage of the device.
Just a lot of sensationalist media crap based on half arsed research.
See chapter 10 of “iOS Forensic Analysis” by Sean Morrissey published in December 2010, Apress. Mr. Allan and Mr. Warden failed to cite at least this and in fact failed to cite any prior work. For example “Third Party Application Forensics on Apple Mobile Devices” by Levinson, Stackpole and Johnson, hicss, pp.1-9, 2011 44th Hawaii International Conference on System Sciences, 2011.
What Allan and Warden reported is well known and old news.
It becomes or has become just another element a criminal has to consider while committing crimes. A criminal wears gloves to avoid prints, a mask to avoid photography identification, false ID to fake access, vests to avoid getting shot, more powerfull guns to effectivly shoot back, proxys to mask IP, drive vehicles not linkable to themself to beat traffic camera evidence, burner phones to not get linked to a device under your own name and for a along time now keep location trackers aka. Cell phones at home. The only people that suffer an invasion of privacy are honest citizens. As LE is depending more on this technology it may serve as an aliby for the criminal “Your honor, the iPhone .db clearly show my client never left home at the time of the murder…”
@klaus Not every criminal is into violent crime, many do not carry guns, and getting a vest isn’t that easy, they are expensive and stick out like a sore thumb and incidents with criminals wearing vest are not that abundant.
Plus there are many dumb criminals and only in TV shows and in reports of dumb cops that failed to apprehend one they are dubbed ‘geniuses’ but that’s not the reality of it.
@wiregeek
I don’t think you even understood what you linked to or exactly that is about. They never explained what the “Program” is about. So your speculating that scores of cops are going to be driving around with devices that cost 2k each just to down load cellphones from people who are speeding. I think your screaming the sky is falling while wearing a tin foil hat.
@ArthurPint
I agree.
I just tested this myself as did some others on some backups. Some of the points are pointing into the ocean. It gives you a rough idea but I sure wouldn’t want stake my life on its accuracy. and I definitely wouldn’t want to use this as some sort of evidence in a criminal case.
Photos taken with an Iphone have exif data with gps locations as well.
As it has been mentioned it more of a GPS aware getting triangulation from cell towers and not exact coordinates.
So we can all remove our tinfoil hats now, aliens aren’t coming for us…. YET
Never in his wildest nightmares did George Orwell suspect that people would wait overnight in the rain to get the latest government tracking device, pay for it and then pay a monthly fee for it.
2/3 of people are sheep.
This wasn’t news till two mediocre researchers who make six figures found it..typical
@xorpunk They don’t seem like the six figure types to me, brits who write for o’reilly publishing? I don’t know, doesn’t sound like a million dollar setup.
As for the other commenters on accuracy, why don’t you watch the damn video and they mention that and show the errors plotted even, geez.
Enjoy your inedible fruits!
@m1ndtr1p
mhhh…i’m wondering, did you read about this interresting database on android phones? ok…it’s not as easy to access, and your phone has to be rooted, but…didn’t you state, android doesn’t do that, not even close, i imagine…omg, i’m really shocked…NOT
i’m happy with my freerunner :)
MSNBC and abc totally misused this information! They made it sound as if anyone could find these data points whenever they want! It made me mad that the place that most people go for news was leaving out important details!
Conversation at work with an Apple fan boy:
(9:26 AM) S: http://hackaday.com/2011/04/20/iphone-watching-every-breath-you-take-every-move-you-make/
(9:26 AM) J: lol i heard about that
(9:26 AM) S: uh huh – evil
(9:26 AM) S: evil company
(9:27 AM) J: LOL
(9:27 AM) S: Seriously as someone who owns an Iphone, are you ok with it logging your every location to a plain text folder on your pc, which then updates to any new iphone device you buy?
(9:28 AM) J: sure, nothing in my life has changed
(9:28 AM) S: so, the fact that someone could hack in to your pc, obtain the file and work out the most common times your are out of your house to then go and rob it doesn’t bother you?
(9:29 AM) J: nah
(9:29 AM) J: i don’t have much to steal lol
(9:30 AM) S: So that’s how you justify that even though they may not think you are home you’re wife might be?
(9:30 AM) S: After all not having much to steal doesn’t prevent people from looking
(9:30 AM) J: she has an iPhone too LOL
(9:31 AM) S: still doesn’t justify why they have the right to track you.. What about the right to personal privacy and this being a degredation of civil liberties?
EOL – No Responce Recieved
Just to clarify on my above comment.. I understand it’s not that accurate I just wanted to troll him to show that, most apple fan’s will try and explain away anything just to have their fix.
@Simon: please present us an exemplary conversation with an imaginary coworker who has an iPhone but is not a fanboy. I’m really curious how you imagine goodthink.
@svofski : Not at all imaginary :
https://picasaweb.google.com/112668747311221384895/Work?authkey=Gv1sRgCKfGsNvioaGcdw&feat=directlink
M owns an Iphone and an Ipod that is it. J pretty much lives for apple products, he’s even so far as having the Apple tv setup.
@Simon: I didn’t express myself clear enough. I mean, what would you expect from someone in place of that fanboy coworker of yours? Should he have thrown his iphone in trash immediately, or what?
(lol @ apple tv setup though)
@ svofski, I wouldn’t expect anyone to throw it away, they are took expensive for that. I would have at least liked to have seen some sort of concern for personal security, rather than just saying oh that’s fine and glossing it over. Seems most fanboys like to ignore possible security implications just because it’s Apple (for the sake of making others aware, I am not an Apple hater)
@Simon: thanks. I just think that I would hmm to myself and then likewise ignore similar problem in a whatever device I have (I have Android, just in case), for example. Maybe Apple fanboys get too much attention from non-fanboys because they’re easy targets? :)
F**K THAT!!!
On law un-enforment getting your phone I say get an old phone gut it and then place a photo strobe hooked to the data port and give them that.
Then when they plug it in their little machine from Satan’s workshop gets 280V put to it.
That or just give them a dead ass phone and hide your real one.
If you are dumb enough to have given them the real one then at least file a law suit ASAP.
“On law un-enforment getting your phone I say get an old phone gut it and then place a photo strobe hooked to the data port and give them that.
Then when they plug it in their little machine from Satan’s workshop gets 280V put to it.”
Sounds like a great project for hackaday, Nitori!!
I have had my phones hacked by spyware, my computer hacked……….all from ???? No one has owned up…………..so if someone would help me do the same and turn it all around and end my miserable existence………..let them see what it is like……….I am ALL FOR IT>