It’s time to do your best impression of [Comic Book Guy] as you make your case for trash or triumph in big screen hacking scenes. We watch a lot of movies, and it’s hard not to groan when the filmmakers cut corners by doing zero research into what using a computer actually looks like. But then once in a great while you have a team that does its due diligence and puts up a scene that makes sense to those of us in the know. So we’re wondering, what movies do you think have the best hacking scenes, and which ones are the worst offenders? Leave your opinion on the topic in the comments section.
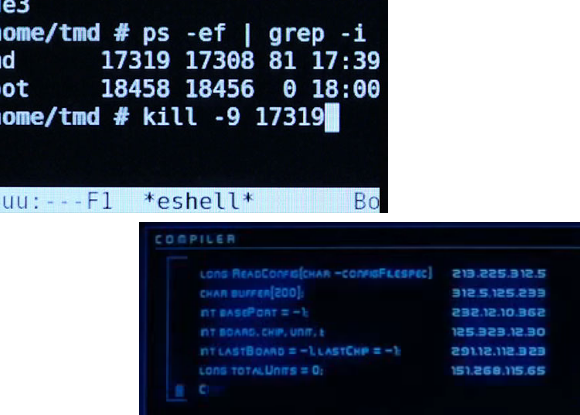
We realize that you can come up with tons of poorly done ones, what we would really like to hear about is who did it right. We’ll get you started with a couple of examples. The image on the upper left is a scene from Tron: Legacy which we think did a fantastic job of portraying actual computer usage. You can read more about the huge amount of work that went into it in this article (via Reddit).
In the lower right is one of the most shady movies scenes that comes to mind. [Hugh Jackman] is compelled to do some ‘hacking’ by [John Travolta] in the movie Swordfish. The caption at the top of the screen is “COMPILER”, and who the heck knows what the rest of that is supposed to be?
On the hardware hacking side, it gets a little more difficult, we would LOVE some examples of hardware hacks or mods done right.















For a real oldie, how about Frankenstein? Hard to say if it’s about hardware or wetware hacking, though.
And how about Pump Up the Volume, remember that one? Cheesy, but fun. I liked how Happy Harry Hardon set up his transmitter in his neighbor’s shed (which got its door kicked in instead of Harry/Mark’s house) and later drove it around in a Jeep so the FCC couldn’t triangulate their signal.
Primer isn’t exactly a hacking movie, but I think it deserves a mention.
Oh, and a wild movie with some interesting hardware hacking (and drilling, and smashing, and bypassing) is Street Thief from 2006.
Meant to mention that Street Thief has some excellent social engineering scenes…
No noms for Takedown?
Sure it’s a biased and fantastical take on what happened with Kevin Mitnick, but some of the scenes get you to thinkin…
oh my god HaD, the comment system is so so bad. so bad. Please, just go ‘steal’ reddit’s. Seriously though, it’s open source, and a great comment system. Even scrap upvotes and downvotes, and just use replies and minimizing comments.
Yeah. I’ve found it awkward to use. Is it not the standard comments functionality from WordPress though? Perhaps someone can update the WordPress code so it can turn up here when they next update?
For hardware hacks
Saw as most of the traps actually work!
Ferris Bueller’s Day Off
I’m sure changing grades in the computer system from home was easy in 1986.
Not that I’ve seen any hacking scenes as such in it, but the TV series The Big Bang Theory is pretty spot on when it talks about computer related stuff. Seems well researched enough to not make me cringe.
My favorite sorry its not from a movie its from NCIS tv show
two people on one keyboard… so funny
http://www.youtube.com/watch?v=u8qgehH3kEQ
It’s not quite “hacking,” but in the terminator movies, the code that’s shown in “terminator vision” is 6502 assembly.
Hack the Planet!
http://nmap.org/movies/
They even have Pron movies now with hacking scenes
http://nmap.org/nmap_haxxxor.html
NCIS as just painful to watch, for me the tipping point was in an episode they connect the harddrive of a dead victims harddrive to see what is on it and start getting video chat from a fat lady who is “Hacking past their firewall”.
Seriously their “secured” terminals must double as free public internet terminals for anyone and be infected past its eyeballs.
http://www.welcometothescene.com/
OK OK not a main stream movie but it seams to choreograph the trials an tribulations of pirating movies (first series) I was first saw metasploit used in one of the episodes…
better than hollywood this mite be filed under educational entertainment that good I think…
kcim aka napervillin
later
I think the bogus IP addresses (whether they are invalid, or just private address ranges) are done for the same reason they use 555 phone numbers in movies, although I do remember reading about a movie where an IP address is mentioned in the movie (I think it was Cloverfield) actually went to a legit website that was somehow related to the movie.
Best: Whiz Kids (http://www.imdb.com/title/tt0085110/)
Not a movie but a TV series. Has lots of realistic hacking scenes, especially in the first chapters.
The best are:
Wargames
Sneakers
Real genius
The Americans (even though it’s a tv show)
In the episode of Numbers with the malfunctioning laser firing drone aircraft, in the scene with the blasted van… one of the investigators looks at the pile of damaged equipment and says something about highly advanced technology.
Setting on top of the pile is a completely undamaged old PC motherboard, 80386 or early 80486 with 8 and 16 bit ISA slots and 30 pin SIMM sockets.
If that’s what was operating the drone, it’s no wonder it hit the wrong target.
30 Rock, when Alec Baldwin’s character had a childhood picture of himself looking into a box at a present that he had received. He wanted to remember what was in the box, so he called in one of the techies and told him that he needed the image rotated so that he could see what it was.
“We can’t do that.”
This is probably how Hollywood and most “Muggles” see hacking Ha ha ha
http://hackertyper.com/
alt 3 times = Good
Caps Lock 3 times = Bad
enjoy the look on people’s faces when you do this in public Ha ha ha
That supercomputer inside Silva’s lair in 007 operation Skyfall… very interesting…
No reactions to Hacker 2 – Operation Takedown
How about the portable Atari used on the ATM in Terminator 2
In Paranoia 1.0 (2004 cyberpunk science fiction) the virus code shown is from the source code of viralator that is an antivirus.
A bit off topic, but if you’re looking for movies with clever hacks, The Manhattan Project (which is a seriously underrated movie) does a nice job of showing how someone like a HaD’er would go about building a nuclear device if they got their hands on some plutonium.
Steven Seagal, Driven to Kill… for sure..
http://www.youtube.com/watch?v=laJChNL6xJ4
Hacking with Windows Media Player:
http://www.youtube.com/watch?v=HyDXEik3mH8
That article about Tron Legacy… there are some serious formatting issues going on…
Also, worst font choices EVER. Leave browser fonts alone. Never ever do that. Ever.
Seriously, I’ve not had to disable styles to make an article readable in… forever!
Surprisingly Numbers is pretty accurate. Sure a lot of stuff is exagerated, but they mention real things like backscatter and not something like “He’s using a computer, so I hacked into his computer and got his IP. Using it, we can triangulate his position on his mobile phone”. Despite it being quite accurate, the biggest thing that bugs me is there was one scene where they were like “look at this number: ‘169 23 56 258’… Oh it’s an IP address!” I facepalmed so hard at that scene
If it hasn’t been mentioned yet…. most accurate movie: WarGames.
It actually shows a modem(Acoustic Coupler), a WarDialer(named such for this movie), The Voice Box(It was a real thing in the early 80’s), social engineering(lying to people over the phone to get information), Phreaking(the soda-can tab thing with the pay phone), researching a target to get a password…
You actually used to be able to dial-up a bank, school, or an airline and do things because network security hadn’t been invented yet.
hacking nukes with tic tac toe.
For those who say that ID4 wasn’t any good, consider the following:
1. The aliens was studying earth for a long time before they actually invaded. Being that they needed a way to synchronize their activities without line of sight required the use of our satellites. As such, their communication system needed to be compatible with our telecommunication system to even work.
2. David (Jeff’s character) used a spectrum analyzer to figure out a way to filter the “distortions” caused by the aliens’ communications system. Figuring this out allowed him to know partially how their systems communicate with each other (kind of like packet-sniffing to find which packet is disrupting a connection). But he didn’t have the complete knowledge necessary to disrupt their systems till….
3. He got to Area 51 where he was able to get that info from the scientist there. There’s a delete scene where he’s showing them the countdown signal and how similar it is to the now-powered craft’s control systems (they might have tapped into the com bus to analyze the feed but needed the info he had). With this info, it’s just a matter of analyzing both signals to find a way to create a denial-of-service attack of whatever system controls their shields. The “virus” just disrupted the shields from working by giving the aliens’ system a signal that will “distort” that part of their system.
4. As for the skull thing, if the countdown timer was analyzed enough, it is possible they can send a signal that can interpret the signal to show it on the aliens’ screens just as their countdown timer showed up as regulated distortion in the tv screens.
I remember one phreaking/social-engineering scene in Three Days of the Condor. I think Turner first stole telco technician kit and then dressed as telco technician he went into central office to make a call or something like that. It wasn’t really that authentic but much better than some hacking scenes nowadays. (Btw this movie is why Kevin Mitnick choose handle Condor in his early hacking days)
In the late 90s, there was a TV series called “La Femme Nikita” (http://www.imdb.com/title/tt0118379/) spun off from the French movie of the same name and/or the American remake “Point of No Return”.
They had lots of gadgets, both for tech and for weapons. When they occasionally showed/said details of some of the tech stuff, it was realistic Unix.
I remember one scene where the brainy guy back at HQ asks one of the guys/gals on a mission to point their camera at a monitor while he tells them what to type to disable something or other in the bad guy’s systems. First, it’s some variation of “ps” and it’s followed a bit later with “kill -9 ….”
Maybe they liked it because, “heh, heh … you said ‘kill’ … heh, heh”.
I think the best hacker movie to date it Reboot https://www.youtube.com/embed/uB-gw5CmaCg
I forgot all about this one! Takedown: The Kevin Mitnick Story. There’s a lot of social engineering in it.
Brainstorm is a personal all time favorite.
I would say that this sums it all:
http://i.imgur.com/IFQzu.gif (johnny mnemonic)
Hackers… the director actually approached “us” hackers back in the day. My g/f and I at the time helped with some of the details. Details like it was a big thing to make your compute rmore than an “almond” box, how geeked-out excited we got over new hardware, personality types, the retarded-social behavior within the dating scene with the one “alpha-female” and hordes of desperate guys. I was told, but did not confirm, that the relationship was based on me and her (my g/f, not Angelina) which is unfortunately accurate (and as most phaccv relationships were it ended poorly). We had lengthy conference calls with her (the director about this). The majority of the technical information came from the guys at 2600 Magazine. So, when you see something accurate, they got it from them, but they also had fun with some of the concepts.
The reason being that hacking is actually kinda boring unless you are into it. I mean, what do you do? Show the back of some dudes head as he types away into a terminal window as he drinks mountain dew, smokes cigarettes, and eats hot pockets? That’s the reality. Now, I guess you could have multiple VMs tied to different physical NICs -perferably WiFi adapters joined to WEP networks that you cracked in 30 seconds- and you start hacking your way in. But, that’d be a bit more eye candy, I guess you could capture the screen as it gathers packets and tries to crack WEP, I find that fun. But, anyone else who sees it is bothered by the “text” and wants to see something animated. I dunno.
Hackers is a pretty accurate depiction of the 90’s era hacker scene, that I was part of. We (as in me and my g/f at the time) met the director of the movie (that we met at HOPE ’94) and we exchanged a lot of information over the phone. They wanted to make it accurate for the age group they were portraying so we gave them examples of stuff we did, like customizing computer cases, geeking out over the latest hardware, the off-center sense of style, etc. The primary source of info, and the source of anything technical, was the guys of 2600 Magazine (who are based out of NYC). They provided somewhat accurate information on some things but then had fun with other concepts. But, I mean, what can you do? Show the back of the head of some anemic, pale-faced dude, who smoked cigarettes, drank mountain dew, and ate hot pockets. As he’d work a terminal window and try different methods to “hack” in while he muttered to himself. That’d get old after 2 seconds. So, they had to make it entertaining, and, they did. After all it is a movie. Even now, i guess you could have someone with a QHD monitor, with multiple VM, tied to physical wnics, each on a cracked WEP network, hacking away. More eye candy but still boring even if used something known like BTR.
Another item that is accurate, and as I have been told was based on the relationship I had with my g/f at the time, was the relationship between the two main characters. You have the alpha-female that is highly coveted by a swarm of sexually deprived males and is constantly bickered over. As with most p/h/a/c/c/v relationships it did not last and the last guy that dated her is “ousted” from the “pack”. In case you are wondering, I was not the guy who won her in the end, Loki did (congrats dude, you got your dream girl).
The personalities, the club scene (they left out the major drug component) is accurate of the NYC and DC-area “hacker-scene” of whence the movie was filmed. Clubbing, partying, hanging out, geeking over computers and the latest NeXT and how the pipe key was in the wrong place (I remember when NeXT went color), etc. Going to raves and the associated drug culture was also a big thing, and there were newsgroups and IRC channels dedicated to it. We’d rent buses and go from DC to NYC, etc, for clubbing. All part of it, not everyone did, but a lot did. Overall, though, the fact that everyone had each others back, is not accurate. There was a lot of paranoia, caused by certain people (Noel), and it was common to get bullied. But, then again, it was a mish-mosh of non-governed HS kids mixed with older guys and even older guys who watched in a mix of dismay and comic-relief.
So, is Hackers technically accurate? No, a hacker movie never will be because it’d be more boring than someone using Windows or OSX. But, did movies like Hackers and War Games portray an accurate, albeit fictionalized, “hacker-scene” of its era? Yes.
If you go to the 2600 page, and look, you’ll find a pic of me and my g/f at the time.
Ok, there is a HaD post about hacking in film and TV and not a single mention of one of the ultimate hackers, McGuyver?
And to someone like me some of the hacks actually seem like they would actually work in the real world…
“Blankman” had some hilarious hardware hacks. :-)
I was surprised it took so long for “The Net” to be mentioned. Ugh…
http://www.youtube.com/watch?v=iSr7kOCdPTc
Surprised to see that the TV show leverage hasn’t been mentioned. Some good ideas and some, I use the word some sparingly, of the tech jargon was legit. Some of the hardware hacks seemed plausible tho :) also a fun show to watch
Also hackers was an awesome movie, and despite some of its short comings alot of it was near bang on i.e. phreaking and that a worm could be mining funds. And obv Angelina ;)
Anyone else watch haxxxor? its a softcore porn with actual real info on linux. Pretty odd combo, but it works :)
How about ANY COMPUTER THAT MAKES NOISE when logging in, typing passwords, starting up, etc!
we had this one yet?
http://www.youtube.com/watch?v=tVQsxLfKPNI
In the last episode of the 5th season of NUMB3RS, Amita is shown “hacking” into the servers of a credit card company. The only problem is that the code she’s typing is for a UITable in an iOS app.
Some of my favorite movies have already been listed, but the ones left out, Masterminds = hack via gaming. Also on the series side, Leverage and Continuum?
Mentioning hacks via gaming reminded me of the Atari-era “Cloak & Dagger”, with secrets hidden in a game cartridge (though these days it would be easier to just read the ROM than play the game!)
There are lots of movies with fault hacking scenes. Die hard has something like this too.