I was off at the Chaos Communication Congress last weekend, and one of the big attractions for one who is nerdily inclined is seeing all of the personal projects that everyone brings along with them. Inevitably, someone would ask me what my favorite is. Maybe it’s my decision paralysis, maybe it’s being forced to pick a favorite child on the spot, or maybe it’s just that I’m not walking around ranking them, but that question always left me drawing a blank.
But after a week of thinking about it, I’m pretty sure I know why: I don’t actually care what I think of other peoples’ projects! I’m simply stoked to talk to everyone who brought anything, and bathe in the success and failure, hearing about the challenges that they saw coming, and then the new challenges they met along the way. I want to know what the hacker thinks of their project, what their intention was, and how their story went. I’m just a spectator, so I collected stories.
The overwhelming, entirely non-surprising result of listening to a couple hundred hackers talk about their projects? They’re all doing it for the fun of it. Simply for the grins. And that held equally well for the supremely planned-out and technical projects as well as their simpler I-bought-these-surplus-on-eBay-one-night relatives. “We were sitting around and thought, wouldn’t it be fun…” was the start of nearly every story.
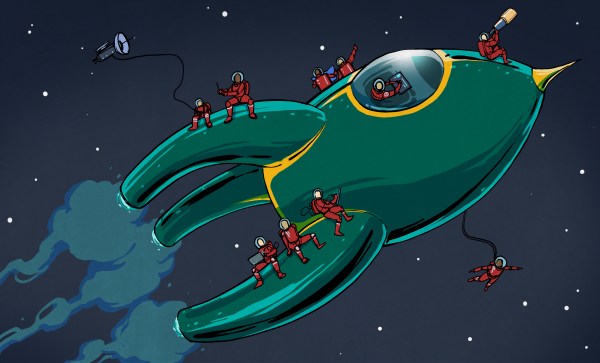
That’s what I absolutely love about our community: that people are hacking because it makes them happy, and that the amazing variety of projects suggests an endless possibility for hacker happiness. It’s hard to come away from an event like that without being energized. Some of that comes from the sharing of ideas and brainstorming and hanging out with like-minded folks, but what I find most important is simply the celebration of the joy of the project for its own sake.
Happy hacking!