3D printers have become indispensable in industry sectors such as biomedical and manufacturing, and are deployed as what is termed as a 3D print farm. They help reduce production costs as well as time-to-market. However, a hacker with access to these manufacturing banks can introduce defects such as microfractures and holes that are intended to compromise the quality of the printed component.
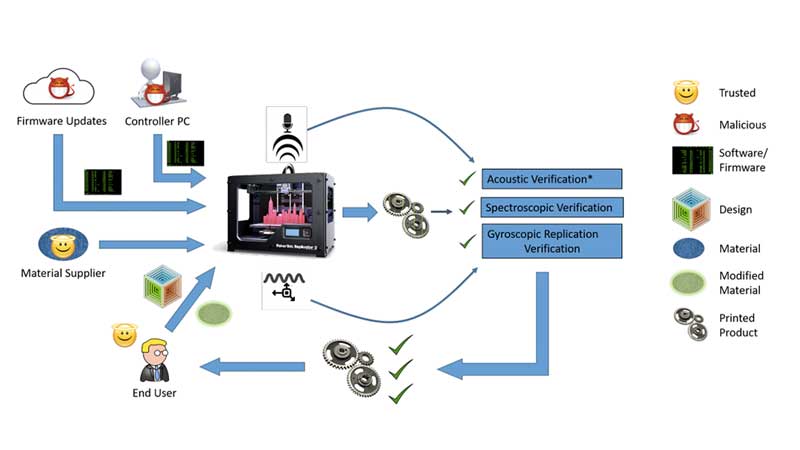
Researchers at the Rutgers University-New Brunswick and Georgia Institute of Technology have published a study on cyber physical attacks and their detection techniques. By monitoring the movement of the extruder using sensors, monitored sounds made by the printer via microphones and finally using structural imaging, they were able to audit the printing process.
A lot of studies have popped up in the last year or so including papers discussing remote data exfiltration on Makerbots that talk about the type of defects introduced. In a paper by [Belikovetsky, S. et al] titled ‘dr0wned‘, such an attack was documented which allowed a compromised 3D printed propeller to crash a UAV. In a follow-up paper, they demonstrated Digital Audio Signing to thwart Cyber-physical attacks. Check out the video below.
In this new study, the attack is identified by using not only the sound of the stepper motors but also the movement of the extruder. After the part has been manufactured, a CT scan ensures the integrity of the part thereby completing the audit.
Disconnected printers and private networks may be the way to go however automation requires connectivity and is the foundation for a lot of online 3D printing services. The universe of Skynet and Terminators may not be far-fetched either if you consider ambitious projects such as this 3D printed BLDC motor. For now, learn to listen to your 3D printer’s song. She may be telling you a story you should hear.
Thanks for the tip [Qes]















Reasons to not use Windows #2308942
Add this to the pile of clever attacks that would be almost impossible to pull off without already having intimate knowledge of the network and what’s on it.
A frustrated employee and some $$$ will make it a lot easier…
A frustrated employee with a USB drive would be much more efficient.
And wouldn’t you need to know how the correct print sounds to know of its deviated? Wouldn’t you need to know what the correct model was to know if it matched the CT scan?
It is kind of a shame that there isn’t some sort of A-Team that goes and gets the human responsible for these attacks and finds a nice home for them at the bottom of the Pacific Ocean. The only real way to stop the machines is the people that control them.
Kind of interesting to see the acoustics being used as another way to verify proper operations.
I was wearing hearing protection, so actually makes it easier to pick up on the bone transferred vibrations/noises
Many moons ago, I was leaning against a machine, on my elbow, with my knuckles against my cheek bone.
Boss man walks up and asks why.
I gave an explanation of how many things I could pick up about how the machine was doing its job.
Cutter in the metal vs in the rust and scale. Kind of a growly hissing for the steel and gritty grind for the mill scale.
Noises change as the tool get dulled by the rusty scale.
Changes in the gear noises also can tell of tool loading/dullness.
Lots more but it’s been a long time and my memories have lost a lot now.
Hi, nice post. 3D printers have become indispensable in industry sectors such as biomedical and manufacturing, and are deployed as what is termed as a 3D print farm. They help reduce production costs as well as time-to-market. However, a hacker with access to these manufacturing banks can introduce defects such as microfractures and holes that are intended to compromise the quality of the printed component. Nowadays there are so many 3d printing and rapid prototyping Service Providers like Iannone 3D are available due to customers demand. Thanks for sharing the video with us. Hope all will be got the necessary things after seeing this video.