If you ever watch a spy movie, you’ve doubtlessly seen some nameless tech character sweep a room for bugs using some kind of detector and either declare it clean or find the hidden microphone in the lamp. Of course, as a hacker, you have to start thinking about how that would work. If you had a bug that transmits all the time, that’s easy. The lamp probably shouldn’t be emitting RF energy all the time, so that’s easy to detect and a dead give away. But what if the bug were more sophisticated? Maybe it wakes up every hour and beams its data home. Or perhaps it records to memory and doesn’t transmit anything. What then?
High-end bug detectors have another technique they use that claims to be able to find active device junctions. These are called Nonlinear Junction Detectors (NLJD). Spy agencies in the United States, Russian and China have been known to use them and prisons employ them to find cell phones. Their claim to fame is the device doesn’t have to be turned on for detection to occur. You can see a video of a commercial NLJD, below
Theory
The idea behind an NLJD is to flood a volume with an RF signal at a particular frequency. Normal insulators and conductors in the area won’t alter the signal. However, anything that has a nonlinear response — like a diode junction — will emit harmonics. They might be at a low level, but if you can detect the harmonics, you can identify these junctions.
Sounds simple, but the RF has to be powerful enough to get there and produce a harmonic you can detect. It also shouldn’t be so powerful that you can’t localize the volume or — extremely — that it would damage circuits. The other problem is that any dissimilar metal junction will exhibit nonlinear behavior. So in addition to bugs and cell phones, you’ll detect rusty nails and similar items.
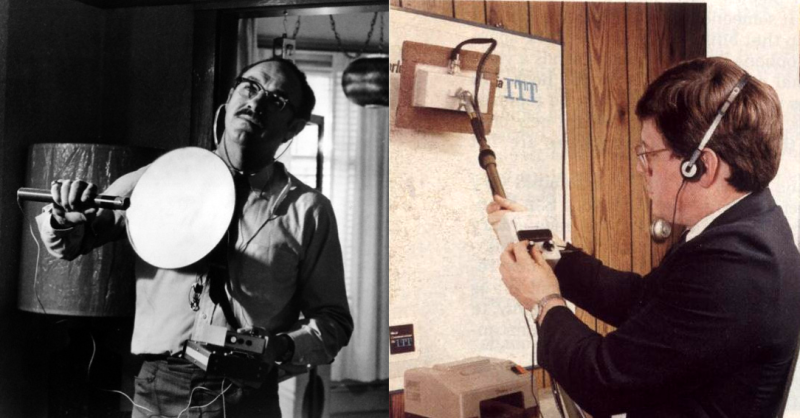
You can get an overview of how a pro uses an NLJD. It is a little more involved than in the movies. In broad terms, the operator gets an idea of any radio sources in the area first, to try to avoid false positives. Apparently, by looking at the ratio of the second and third harmonics, an experienced operator (or a smart computer) can differentiate between a rusty nail and a real piece of electronic equipment.
Off the Shelf
You can buy NLJDs off the shelf. They aren’t cheap though. Even on the usual Chinese import sites, the good-looking models run about $10,000. The more mainstream versions all want you to ask for the price and we decided not to get on any CIA watch lists by asking. We did see an Orion listed for over $14,000.
Of course, the commercial units have other features, but that’s still a lot of money. You’d like to think a clever hacker could do better.
Homebrew
 There aren’t many homebrew NLJDs and we don’t know why. The only clear example we could find was on an unusual site full of underground projects. It says under development and doesn’t show any examples of it in use, so we don’t know if it performs well or not.
There aren’t many homebrew NLJDs and we don’t know why. The only clear example we could find was on an unusual site full of underground projects. It says under development and doesn’t show any examples of it in use, so we don’t know if it performs well or not.
There are detailed photos of the construction, though and quite a bit of data, so it seems like the device exists.
Don’t forget to look at part two of the post. There’s some example software at the bottom of that page for the Basic Stamp II, so while it would not be trivial to replicate, it does look like there’s enough info there to experiment if you are interested.
Spy vs Spy
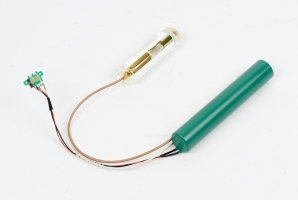 The NLJD wasn’t originally a spy device. [Charles Bovill] invented it during World War II for discovering corrosion below painted surfaces on airplanes. However, the spy use of it became evident. So much so that, since around 1968, CIA devices like the SRT-107 seen here have special filters in them to shunt the probe signal to ground.
The NLJD wasn’t originally a spy device. [Charles Bovill] invented it during World War II for discovering corrosion below painted surfaces on airplanes. However, the spy use of it became evident. So much so that, since around 1968, CIA devices like the SRT-107 seen here have special filters in them to shunt the probe signal to ground.
So for serious spies, the NLJD might not be very useful anymore even though more common bugging devices might still be susceptible to detection. However, there’s a bigger reason these aren’t as useful as they once were. With computers and cell phones everywhere, you really don’t need to plant a bug anymore, do you? You just need to compromise the subject’s device and in many ways, that’s even easier to do.
Covert bugging is nothing new. The amount of tech that goes into hiding them and finding them is a largely unknown race that might even dwarf the space race.















is that a bug in the lamp, or just an LED lightbulb…. could be both!
Yeah I can’t see how this would be effective in a modern house filled with electronic junk. Most people have semiconductors on the walls and tables in every room. And nowadays the “bug” is probably just software running on your laptop or Amazon Echo.
Field strength. That’s why it looked as if he were vacuuming the wall. It is by design very short range as an aid to locating a bug you know is there. The circuit is very simple, a very clean transmitter and some very selective receivers. Easy to homebrew as was everything Hackman’s character used in the film.
@jon – http://www.upl.co/uploads/selfemitting-bug1505943229.jpg
@Jon – with this idea of mine above, a NLJD would scan over it and read positive for P-N junctions. However, the anti-surveillance technician sees that the bulb is a LED type and goes “Oh that’s why it detected that bulb!” and moves on.
If you are someone who would feel the need to sweep for bugs then you probably aren’t bringing such devices with you to your secret talks regarding confidential or classified information. In fact I would expect that a room that has been cleared of electronic devices would be the norm.
At least that’s what I would do if I were some sort of spy or diplomat dealing in state secrets. Wouldn’t you?
@me – Well if anyone is that paranoid about audio bugs at secret meetings just bring your laptop (with good speakers) with Internet connection to the secret meeting and play this YouTube 10-hour audio clip in the background at full volume. Be sure to talk near the laptop speakers in a low undertone facing each other. It is guaranteed to make the surveillance tech in the undercover surveillance van outside listening-in want to interrupt your secret meeting and strangle the both of you, as his graphic equalizers and DSP’s just can’t handle it: https://youtu.be/wzjWIxXBs_s
This will also help you sleep, study, and focus on work. If no Internet connection then use a YouTube stripper/downloader to bring it offline as a MP3 or something. Remember this is eventually defeatable with on-going common knowledge; so make your own home-brew version with randomization pitch changes one day.
I’ve considered attaching a speaker that is connected to an AM radio that is tuned to two competing stations to a window to foil laser listeners. But who wants to hear what I’m saying. B^)
Ren – The AM radio gambit may be distracting to your meeting participants like “WTH is that noise Ren? Turn it off!”. I was thinking of a less disturbing noise that your brain can filter out. And your GLG-20 employees may fall asleep listening to it if he’s not ready to go ballistic over this unexpected surveillance-thwart. GLG-20? You know this type of fictional US federal employee like Austin Milbarge (Danny Akyroyd). https://youtu.be/Gl1FHUIWNzY
Who’d want to listen to you? Well you’re already on THE LIST for just visiting HaD. So maybe the GLG-20’s want to get some new ideas from us for the next DARPA Challenge! :-D
As the coolest actor ever, Jack Black, said in E.O.S. (1998) – “We were told to write it up as a F.B.I. S.T.Op… standard training op?” GLG-20’s blame everything on “phoebe”. It’s called “plausible deniability…” (LOL) – just jokin’ & smokin’ phoebe…
Why not:
https://en.wikipedia.org/wiki/Cone_of_Silence_(device)#/media/File:Get_Smart-Cone-of-silence.jpg
@Al Williams – Yes you’re right. Your CONE OF SILENCE link did not resolve correctly but I got it anyway. Here is a REAL CoS for POTUS-44 the one POTUS-45 forgets to use when secretly talking to his buddy in KGB-land… :P
https://ichef.bbci.co.uk/news/660/media/images/51710000/jpg/_51710350_obamatent464.jpg
Ren – I think you meant FM radio. You get better whitenoise from that. AM will be just a lot of snap crackle pop QRN/QRM, hardly any WN. You can even get good WN from your water faucet tap (with aerator). But you’d both have to be almost face to face with it in the sink to be effective.
No way! White noise like that would be too easy to filter out. I’m thinking several non-networked ‘music’ players playing clips of the same people who are currently in the room talking about innocuous things on random shuffle. Or.. maybe that AND white noise. Hah! Pick me out of a whole room of mes!
But.. that’s only if I actually had something to say that “they” would be interested in.
@me – Actually white noise is not EASY to filter but yes you can do it with anti-phasing but you need the exact WN source the target is using. However, if you randomize the pitch programmatically with say an Arduino, you’ve made a extremely effective foil to the surveillance tech, and your face on his dart board in his surveillance van.:-)
The system you described here was invented about a few decades ago by an ex-convict looking for the perfect anti-audio surveillance method. I have to admit the resulting cacophony is daunting. Makes one wonder how two targets can communicate over such a noisy system.Remember, the basis for ENIGMA was invented by an ex-con too in 1901 and his idea was stolen by Americans and put under wraps for decades.
Right. Even easier is play more than one version and start subsequent version at different times. Would brown or pink noise be any different in complexity mixed in? I’m thinking unless the undercover surveillance knows or pattern recognizes the start time… they’ll be angry for longer. Amazes me how criminal the ES/TS/TSCM/PI world has become and turning more into an EW operation. Targeting non-criminal scientists and civilians to stealthy frame, pin and mug as scapegoats to compound and conceal their continuing criminal enterprises. I wouldn’t doubt if they even train on vulnerable adults and even go so far as to entrain children and juveniles so to groom as victims and be desensitized to the criminal operations.
If you’re worried about audio bugs at secret meetings, bring a laptop with good speakers and an Internet connection. Play this 10-hour YouTube audio clip at full volume in the background. Speak quietly near the laptop speakers, facing each other. The surveillance tech in the undercover van outside will likely be overwhelmed and want to interrupt your meeting. https://youtu.be/3nbXf29wZJA
You can use a YouTube stripper/downloader to save the video as an MP3 if there’s no internet connection. It’s important to remember that this method may not always work due to ongoing improvements in technology. Alternatively, you can create your own customized version by randomly changing the pitch.
Amazon Echo is pretty much a ready made bug.
Alice – Actually GOOGLE is listening to you right now through your microphone in your laptop, PC, or Mac. They admit to it too. They are using it to send you pertinent adverts. Ever wonder why a n advert popup in YouTube and other venues seems to mysteriously be something about what you were talking about out load not too long ago? Could have been a telephone call, a family conversation, talking to yourself, or it was picking up your TV or radio in background. Google In-Q-Tel and see who they are really. They helped Google develop all of their clever apps.Plug in a dumy mic into your side port or run whitenoise to your internal mic with this: https://www.youtube.com/watch?v=wzjWIxXBs_s&feature=youtu.be It’s 10-hours long!
I notice that turning off the feature listening for me to say ‘OK Google’ or whatever the trigger words for a Samsung Android device are makes my phone more responsive, cooler and the battery last longer. This makes me thing that whatever listening Google (or Samsung) does for other purposes probably turns off with that.
Even regular businesses now ask participants to meetings to leave their phone outside.
So if you are someone, like a big company, that needs to guard against spying you already did your initial effort to not be full of false negatives. and then after that you might do a sweep of some sort.
Smoke alarms are a good example. Piezoelectric element can receive sound, quite simple to listen to you talk in your sleep. Then again most people charge their phone by the side of their bed.
CRJEEA – Enemy of the State (1998) Smoke detector bug discovery by Brill (Gene Hackman)? http://www.swssec.com/gene-h.jpg
I’ve tried this with several models of piezo element and a high quality amplifier, and it didn’t work.
The piezo element could only pick up vibrations conducted through the concrete or anything else it was strongly mechanically coupled to. It did not register any sound transmitted through the air.
So you would be able to tell every time someone shut the door, walked loudly, or flushed the toilet but could not overhear what was said. Possibly also detect earthquakes but I haven’t tested that.
On the other hand, it made a great and cheap contact microphone. Attached to your throat, it picks up only your voice and not others in the room. Attached to many musical instruments, it makes an electric version possible. Coupled to a combination lock… well, you get the idea.
How do I know you are not really a government agent trying to throw me.off the trail. I’m on to you and stopped drinking floranated water years ago. My mind is clear as a tack and my tinfoil hat is double lined. Don’t mess with me and my precious bodily fluids.
Uhhhh? Sean did you leave the door open again? Look what the cat dragged in… %-) https://youtu.be/mr6XHJ7qcSE
But what if you’re trying to catch someone whispering sweet nothings to the concrete?
Hmm, you couldn’t make it even with your best effort, but how many billion dollars is your budget, and how many hundreds of PhDs do you employ?
Absence of proof is not the same as a proof of non-existence. Some fancy DSP technique and/or specific knowledge about characteristics of human voice and speech we are not aware of may be needed to extract useful signal from apparent thermal noise. You probably did a proper signal acquisition, but that may be not sufficient for the purpose.
100s? To paraphrase the Tao of Programming:
A manager went to the Master Engineer and showed him the requirements document for a new design. The manager asked the Master: “How long will it take to design this system if I assign five engineers to it?”
“It will take one year,” said the Master promptly.
“But we need this system immediately or even sooner! How long will it take if I assign ten engineer’s with masters degrees to it?”
The Master Engineer frowned. “In that case, it will take two years.”
“And what if I assign a hundred PhDs to it?”
The Master Engineer shrugged. “Then the design will never be completed,” he said.
###
I once broke up a fight at a major company I worked for between two PhDs. The technical argument had degenerated to which one’s PhD was from the most prestigious school. More is not always more. I’d rather have one smart PhD working on something than 100 of them. I’d rather have someone who knows what he or she is doing over any number of other people regardless of credentials.
Just sayin’
Oh, and for the record, I have a very nice MSEE from a very prestigious school and I’ve considered getting my PhD, so I’m not saying there’s no value to it or that it is intrinsically bad. I’m just saying, that’s not really the measuring stick is how many PhDs you have.
[Al]
Back in the early ’90’s some report on Computer programmers or System Administrators showed an inverse relationship Education v. Wages. Something like High School dropouts had very high paying jobs and Ph.D.’s apparently were in it for the joy, not wages… [citation needed]
B^)
On the other hand, thanks to phones we can now get microphones so small that they actually fit in the black plastic piezo holding capsule together with a beeper.
Imagine LED power supply so bad that it has microphonic properties. Is it a bug?
I’m not sure it’s fair to say that these are not well known. Gene Hackman is seen using one (it looks as if he is vacuuming the walls) at the end of “The Conversation” after being bugged by a laser based system. Neither device is mentioned, but even as a teenager I recognized what was going on. Part of why I like the film so much is that it’s technically accurate. He uses a bucket brigade delay line to synchronize the recordings of the target walking around the park. I learned all this from reading Popular Electronics and various books like “The Electronic Invasion”. Of course, now a “martini olive bug” would be a “grain of rice bug” using SMD parts.
I really loved that film! If I remember well, the main character was in an expo and they were talking about a MOSFET based amplifier. I would really never expect to hear about MOSFETs in any kind of movie!
@Reg – I too thought Harry Cauly (Gene Hackman in THE CONVERSATION (1974)) was LASER BUGGED but once I watched the movie again I realized that could not be true? Why? Because Harry was supposed to be the best bugger in the biz. He knew about Laser Bugs because a prototype IR lamp version was invented by (Soviets) Theremin in 1947. By mid 1960’s everybody in the community knew about LASER bugs, except the general public. So how’d they do it?
Look at Harry’s apartment’s windows. They are covered in metal tape for his security system. A little known surveillance trick is to irradiate that tape with microwaves or ultrasonics and the window becomes an audio diaphragm. Since no one still uses this tape for burglar alarms it just faded into history.
Just saw Robert Baer (former CIA) on CNN with Jake Tapper talking about that really mean-spirited audio gadget that destroys your hearing in Cuba. He let slip that you can use LASER and even microwaves to irradiate a common Styrofoam coffee cup and get room audio from it (from any angle too). That was a WTF moment for me. Leave it to Bobby for sharing good stuff… (Watch Syrianna (2005) – one of his consults).
Now here’s another face-palm WTF device invented by David Schwartz in 2009. It involves a LASER bug but uses SMOKE as the reflective particulate matter to irradiate with a LASER https://www.youtube.com/watch?v=Gqe79RpbPxU read his comments section too. Also Google this guy. Plenty of interesting stuff.
.
Certainly plausible, but there’s not really anyway for him to detect a laser bug if it’s been turned off. He didn’t find a bug in his apartment despite ripping up the floor. Yes, RF would have worked with the foil. And finding a resonant cavity (Theremin’s embassy seal bug) would be tough if you didn’t have the right gear at hand. I interpreted it as a laser because there was a recent article in Popular Electronics showing how to build one. In point of fact, a good shotgun mike (the multiple resonant tube type) would have worked just as well. That was described in another article about that time.
Reg – Caul (Hackman) would have found a cavity resonator during his tear down. Caul used shotgun mics himself in the beginning of the movie. He would have looked outside for a open window across the way. LASER mics back then (before optical metamaterial reflectors) would have to be straight across the way from Caul’s window on same floor. He would have seen the telescope hidden behind an open window with a curtain or some sort of hide A microwave bug works the same way as a cavity resonator transmitter does, and can be hidden behind a solid brick wall. And the people Caul was messing with were not amateurs. I think they were the boys from Langley – not sure.
Today you can detect a LASER bug on your window by using a cheap digital (or toy) camera by removing the IR filter. Or if you can get one of those toy JAKKS night vision goggles from thrift store or your kid’s toy box (makes you look like a Borg), you can clearly see the IR LASER spot on your window. Back in 1974 night vision toys and digital cameras were not out yet.But there were those cheap TV repairman IR resolving cards for testing TV remote controls from the late Radio Shack but now MCM Electronics (Centerville OH). Strip glows orange in presence of IR light in a dark room.
If you want to defeat a LASER bug just get a bunch of cellphone vibrator motors (or a simple electric shaver), and tape them to your windows with a 9V battery attached. Or do like the Langley boys do and use double hung windows with white noise from speakers injected into the space. Be sure to hide all Styrofoam cups and plates and put buzzers on any mirrors too. Even your shiny aluminum toaster can be a target too.
I’ve even read where you put transducers directed at/on the wall, floor and ceiling. I suppose you could even couple them to microphones on the table or in the room and scramble all the internal and boundary sounds even more.
I thought at the time whatever was talking was using Power Line Communications or Earth Mine Communications from underground though not in the AM radio range and more-so in the hearing nervous system neuronal cluster hearing frequencies. You know… mechanical operations versus RF operations, i.e. e.g. sound waves as pressure versus sound waves as electric and magnetic fields/charges.
As I recall styrofoam when heated becomes risky for your health. Learn to avoid styrofoam coffee cups for that reason alone.
On the plus side, seems that meal worms can live from it and turn it into safe compost materials, allegedly.
You should not heat the cups to incineration in your living room. But for listening, any object capable of vibrations is sufficient. There was an article about recovering speech from a vibrating bag of potato chips in video footage. Requires some heavy number crunching though.
My favorite film of all time! My thought was that the bug was way up in his saxophone. If he were talking, the shape of the saxophone would amplify the sounds, and when he’s playing it, well he wouldn’t be talking then…
Buddy – good point. I never thought of that. But, the sax sound would be loud and distorted.
The point isn’t where the bug is, the point is that there is no defense and if you know that and you are the target you are in inescapable anguish.
Whatnot – I, however, think there is a defense if he knew where the bug was. He could either rip it out, play white noise to it, or play a long disinformation tape recording toward it. I think every potential “target” should have the later tool in their anti-surveillance arsenal. They could make an HD one in a hotel room with a friend playing cards for an hour or more.
James Bond did it in the movie A View to a Kill (1985). Look for the scene in the hotel where he scans for the bug, finds it in a hotel lamp, then plays a long play tape recording of himself talking to a friend about boring nothing stuff, then goes on the balcony to talk the real secret stuff.
https://www.youtube.com/watch?v=_44MTHVlAw4
BTW the top left hand photo is NOT an NLJD. The one on the right is. An NLJD only appeared at the very end of “The Conversation” as I recall. It’s been quite a while since I last watched the film. In the 70’s NLJDs were used to locate a bug that had been detected via a directional antenna and a spectrum analyzer. Only very high value targets could afford to have an entire room scanned inch by inch. Think about the GPR wall scans in “In the Line of Fire” with Clint Eastwood.
@REG – Re: IN THE LINE OF FIRE – you’d be surprised how much STUFF the USSS advanced team does 2-weeks ahead of POTUS visit to a place (getting normal baseline to compare on POTUS day 1 – to defeat R/C IED’s and stuff). Spectrum analyzers, you name it, they even temporarily weld down man hole covers.
HAh, well if I want to know what the POTUS said during a top secret meeting I just read it in the papers the next day.
Whatnot – +1 :-D
“and we decided not to get on any CIA watch lists by asking” – self-censorship.
Don’t ask or you get on list :)
In that case, paraphrasing the door gunner in Full Metal Jacket, you’re on a list of people who are a threat because they’re very well trained threats who appear to be non-threats.
Though I think it’s safe to assume people who visit (much less write for) publications like Hack-A-Day are on a list.
A few years past, the company that was trying to recruit me said their HR manager was concerned because my “internet footprint was very small”.
And the ultimate lists are of those that our government and corporations fear the most – those that show up on very few, or no lists. So those of you that have managed to stay off of any lists are probably on the list of people that bear the most close scrutiny. Paranoid yet?
So there is a list of people not on any lists?
There are many, many such lists. My goal is to get my name on all of them.
:D
ROFL!
So….
That explains the black Pizza van outside… you know the generic Pizza delivery company with that spinning pizza box on the roof? Yep, one of their couriers.
Mr Mannering – No this is the one to look out for:
https://img.buzzfeed.com/buzzfeed-static/static/imagebuzz/web03/2010/9/20/21/worlds-best-undercover-surveillance-van-16658-1285032078-49.jpg
Now I have to start an actual food delivery service called ‘Undercover Surveillance Van’.
Company policy will be to loiter suspiciously.
Like this one.
http://pleated-jeans.com/wp-content/uploads/2012/05/TheSimpsons.jpeg
Creepy is now days as my Dad used to tell me when I was in middle school or about that time to keep my grades up as high as I can (counter to my Mom trying to keep me “fitting in”) because I was supposed to either get a good job or figure you’re going to have to go into business for yourself. Then consider that all the business’s are most likely owned in most of our markets at least by Sheriff’s or some form of law enforcement or attorney network trying to get “into” anything they “can,” Amazing the leaches that don’t earn anything and steal in strange corrupted legal systems ways and means. So who knows in some jurisdictions who’s not somehow either a confidential informant, undercover, operatives surveillance target or who knows something higher up the sgt. or officer rank and files “whatever they can.”
More recently a moment I had was that in the early 1900’s amateur radio operators would aid law enforcement in recoverying stolen vehicles and other items. Now days, the law enforcement networks as well as attorney networks and some select hospitals poison victims so they have a 30 day isolation period and their vehicle can be “salvaged.” Some states even are more a pain to get information regarding what happened after salvage title change status. Law enforcement doesn’t even investigate stolen items including vehicles anymore. I don’t even think they perform forensics anymore yet scam everyone’s tax dollars for budgets and equipment they hide or hock for more money. I’ve even spoken with repo men who are threatened by law enforcement they can or are hired to repo vehicles from.
Amazingly, ridiculous how malicious the standard government models have become and really the worse role models for civil society that is advanced domesticated complex and even is simple… humane versus being pan troglodyte.
It’s a good practice to keep the digital footprint of you real identity on the Internet relatively small because putting every little thing you do out there attached to your real name for everyone to see is how you end up a victim of identity theft.
It makes the job of black hat hackers exponentially easier as the more they know about you the easier it’ll be for them to crack your passwords.
Not just identity theft is possible,
Handle theft is also possible… i.e. TheMadHatterMansion could have an email of TheMadHatterMansion at Gmail.com and a test by trying to create said email checks it to be valid. Take their handle and rinse for trolling purposes, especially if they’re low digital-footprint types (Don’t often post stuff online).
Take Unferium for example. Well *Cough* somebody *Cough* rinsed off that persons’ handle around the HaD commenting sections…. Still can’t tie any facebook account to that email though.
Alice – Don’t believe the hype. As long as THEY use NSL’s to your ISP’s and web sites, there is no way to hide. Your ISP and web servers worldwide have SERVER LOGS. They record all metadata like VOIP calls made/received, web sites visited, IP addresses, MAC addresses (the true gotcha’ address people forget about), time stamps, browser type, and maybe even handles, etc. A not so famous Bletchley Park, and later NSA employee (then summarily burn noticed) , perfected the use of radio intercept quasi-metadata to effectively track the Nazis movements during WW2. That later was put to use today by NSA to track people by their metadata recorded habits.Couple that with facial recognition software and then you have a TRUE Big Brother state. That fictional TV show PERSON OF INTEREST starts to look valid. Today’s so-called Artificial Intelligence computer networks don’t look so far-fetched today in 2017.
There’s a really spooky NSA facility in Bluffdale Utah that would just stagger your mind as to how much metadata it sucks up hourly. And couple that with all of our 5-Eyes friends worldwide, like the Australian Pine Bluff facility in the middle of the frickin’ outback (coincidentally ALICE Springs) doing the same thing. Just like in that movie SNEAKERS – “No more secrets!”. And they mean it too. :-|
I’m pretty sure Alice was just talking about reducing your risk of criminal identity theft, not hiding yourself from government spy agencies (which seems futile).
I was complaining one time about being targeted (even after 4 guys that armed robbed me were caught and sent to prison) and the person I was speaking with mentioned that the best victim (more so in regards to being a homicide or reality theft victim) is the one who has no connections. I read in “Access Denied for Reasons of National Security” that when stalked, one of the best defenses is to explain to as many people as you can. Reminds me of marketing… canvas to as large an audience as you can for the best sales.
Leithoa – Lists? I don’ need no stinkin’ lists! https://youtu.be/VqomZQMZQCQ – Oh that was “badges” – don’t need dem’ either :0)
Leithoa – You mean this door gunner? https://youtu.be/S06nIz4scvI “Ain’t war hell??!!” These sociopaths are now in the community don’t ja’ know… (Said in the Kansas accent of Gunnery Sgt R. Lee Ermey) also in the same movie…
we the free people You mean this list? https://firstlook.org/wp-uploads/sites/1/2014/07/watchlist-cover.jpg
This wouldn’t detect “The Thing”.
Basically a cavity resonator with one side a membrane which would oscilate due to sound waves. This membrane was connected to an antenna.
Just a hunk of metal and wire but when illuminated it begins radaiting an FM signal of any nearby sound.
https://en.wikipedia.org/wiki/The_Thing_(listening_device)
You’d still have a tuned circuit so there would either be a peak or a dip if the detector dials in on the right frequency?
… and then you have your passive devices and methods such as the device that was found in the US Embassy in Russia (correct me if I’m wrong) which was basically a metal tube with an antenna that, when “bad actors” directed a focused rf signal at it from the building across the street, would modulate the rf signal based on the vibrations (sounds) resonating inside it. remained undetected for quite some time. brilliant.
My fave is the fairly recent “optical demodulation of a vibrating potato chip bag” experiment from those wacky kids at MIT (I think).
Ha! I remember that! I wish I had a high quality camera like that.
Here is the experiment. Its a high speed camera not high quality. It is picking up sound from objects in a video NOT recorded by the original camera’s microphone. This means you can capture sound from old videos that no one knew was present. https://youtu.be/FKXOucXB4a8 The stuff you mentioned starts at time stamp 01:50.
Reminds me of the glass discs Thomas Edison recorded Mary had a little lamb on back in 1877 but had no idea how to play them back. The Smithsonian finally did in 2007 and we can here Edison’s voice: http://americanhistory.si.edu/press/fact-sheets/early-sound-recording-collection-and-sound-recovery-project
That would be a nice tool to find some of those SMDs dropped during assembly.
:o)
That was intended to be a comment, not a reply to a comment. I have no idea how it landed as a reply.
:o/
+1 true I never thought ot that. Like please find the frickin’ black hole my SMD component fell into dammit!
With that we can finally hear just how many shots were fired at the Grassy Knoll. All those leaves on the trees in the Zapruder Film were vibrating with every shot. This would make a great forensics tool for soundless CCTV cameras. Just leave a plant in the picture or a empty bag of potato chips.
If I’m understanding the technology correctly, doesn’t it require high speed video? With 24fps film the maximum frequency you could recover would be 12Hz, correct?
Fletcher – No 24 fps would yield higher than 12 Hz it would be 5x. A typical DSLR is 60 fps but according to the video you can resolve sound from it. It does not have to be high speed recording. You get best audio resolution with high speed recordings. Go to this website and click on PDF to read their white paper: http://people.csail.mit.edu/mrub/VisualMic/
I think the fact, that the image of the chips bag covers 1000s or 10000s of pixels gives you a very high effective “spacial oversampling”. On a standard analog TV signal, where the camera sweeps an electron beam across the light sensitive electrodes you even have real time delayed sampling with every pixel, you could even see this as a sampling rate in the MHz range. But the math to evaluate this could be extremely tricky.
I was thinking with 24fps you would be able to at least 24Hz and maybe double or more multiple if you can measure and accurately predict the transition of the diaphragm. I’ll have to read and watch the video. Musing at the moment.
oh… someone already mentioned the thing. I hate reading.
You mean this thing?
B^)
https://cdn.barrett-jackson.com/staging/carlist/items/Fullsize/Cars/63877/63877_Front_3-4_Web.jpg
Ren – No he meant this “thing”… but some how I think you knew that wise guy… 8-)
https://intelligencenews.files.wordpress.com/2016/01/first-post-h2.jpg?w=630
The rusty nail has to be making a poor connection to some larger metal surface like aluminum siding or gutters. Pipes and ductwork touching each other, or other large metal objects. At least large in relation to wavelength. This can be a useful device in trying to find such radio reception ruining crap.
A completely out of context anecdote: visiting a famous radio telephone factory in the mid 80’s they intertained me with a story from one of their customers that complained about intermittent breakdowns of their fleet radio system. It turned out, after weeks of troubleshooting, that in one office there had been put up a metal coat hook and its screws had penetrated the antenna cable inside the wall going to the roof. However the screw and coat hanger itself was not able to detune the cable, it only happend when it had been raining and the coat hanging there was wet.
I dunno…. there’s a plague or LED bulbs making lamps release a deluge of RF all over the place.
Plague OF… thank you, HAD for STILL not having the function of editing a post in 2017.
Mystick – Open your email and open a new compose. Type your HaD comment there, use spell checker, proof read it, Then when ready on your keyboard press Ctrl-A, Ctrl-C, then come to HaD and click in new comment field and press Ctrl-V. And there you have it a perfect HaD post. If you have a MAC then you’re screwed… (just kiddin’)
OR, HAD could move into the current era. Even CompuServe allowed you to edit posts.
Don’t leave CFL’s out of the conversation.
https://www.researchgate.net/publication/266201167_Characterization_of_compact_fluorescent_lamp_RF_emissions_in_the_perspective_of_human_exposure
Indeed.
I was wondering if V2K can somehow be used using the environments CFL ~10 to 20kHz emission as a carrier frequency somehow superpositioning to increase amplitude if the phase is in sync, i.e. to not negate or alter the signal and only amplify.
You can defeat Nonlinear Junction Detectors with good Faraday Shielding – however that means your bug can’t RF transmit or receive either. The Soviets are the one’s who invented this thing and the Americans figured out how to defeat it. But if you can figure out what type of bug and how Russian diplomat Stanislav Gusev got into a wall molding on 7th floor US State Dept in Wash DC conference room, then you have my utmost respect. It evidently was a MPEG memory store and forward bug that was activated by a close radio signal to download it’s audio captures – and live mic capability too. It was 1999 technology, but for the Russians that is not so bad.
http://www.cnn.com/2017/08/23/us/spyhunter-russia-bug-us-state-department-declassified/index.html
Another NLJD defeat is to not use P-N semiconductor materials for your bugs. Use the new METAMATERIALS instead. Bring back the old valves (vacuum tubes):
http://jacobsschool.ucsd.edu/news/news_releases/release.sfe?id=2060
The SRT-107 was designed to be difficult or impossible to detect via a NLJD by very careful shielding and filtering. If the harmonics can’t get back out via the external leads because of narrow bandpass filters it won’t be detectable. Expensive, but not rocket science.
If someone has unobserved access to a room for even a few minutes they can plant a bug of any type. I lived in a motel room for a long period with an airplane ticket two days a week. I don’t care for TV so for amusement I pondered the problem and came to the conclusion that it was impossible without POTUS level resources. I was able to dream up dozens of ways to hide video and audio bugs. That’s why POTUS has a tent in his rooms when he travels.
I was very unhappy with Snowden for revealing the USB cable bug. Very slick little trick. All the programs he was so outraged about were obvious to anyone with any real technical ability. The irony, of course, is that he will probably spend the rest of his life in a state which is far more aggressive about surveillance. We all get what we deserve whether we want it or not.
Reg – I’m not 100% convinced that the explanation for how the SRT-107 does it’s thing is bona-fide. It sounds made up to hide something else more impressive (which the DS&T geeks are very good at doing). 3-resistors and a circulater? WTF? I’m sure the Russians at MIT (Moscow not Mass) eyebrows are raising right now. Saying in deep Slavic accent: lzhetsy!
A guy name Rustastu Magarajev from Slovakia claims he has the answer to defeating NLJD and has a YouTube video to prove it: https://youtu.be/-aIp6pvh72Y He may be making it up too but who knows…
Yeah I feel the same way about Edwardo too. Just wait until he has to tell The Gray Cardinal NYET comrade!
I think I ran into that USB Cable thingy once. They must have used potting to hide the damned thing. I do not like epoxy resins. I once dissected a Vietnam 1970’s era SIDR VHF seismic detector (looks like animal poop). I had to use solvent for all the potting. The reveal wasn’t worth the asphyxiation potential. :-(
REG- “That’s why POTUS has a tent in his rooms when he travels.”
Someone should have told POTUS-45 about that “tent” when is colluding with the Gray Cardinal. I guess Mueller appreciates this oversight.
some neat njd patents out there. very fun concept to explore and experiment with.
as informative as gbppr’s archive may be, the individual expresses so much hate
for other human beings in just about every issue of his zine and every page in the archive
that I have a very hard time getting through the data. He does offer a great deal of
educational material for amateur’s interested in basic electronics and he makes it fun and
easy to learn by focusing on the more clandestine and grey area uses that aspiring brilliant
minds will find interesting…. if you are a person with sensitivity towards hate speech (race, politics,
sexuality, etc) then I encourage you to skip the introductions to most of the articles hosted
on the link in this article but please don’t pass up a chance to learn something new if the topics
interest you.
measure & know -WJS- it’s a WarJustaSocialize
NLJ WJS – Yes the “individual” you alluded to is “on the surface” a very nice guy and very genius-like with electronic gadgets like some frickin’ Q from 007. I even believe he was one at “you know who” at “you know where” (what I like to euphemistically call a DS&T geek?). However, his personal radical political affiliations got him into deep trouble and was probably asked to leave. But his stuff is really uber-hackaday-ish. Just look at his call sign as a quasi-anagram and you can see his warped mindset. Why he asked the FCC for that particular Amateur Radio call sign is baffling. I’d think that’s something you’d want to keep quiet.
He has a two-part series on how to build your own Non Linear Junction Device, but it is so way over my pay grade my eyes fog up from my brain overloading just trying to read through the 2 articles… :-/
What, no mention of the well-known bug involving neon lamp with a parallel LC tank that “hoots” at RF in the low MHz band and modulates audio from a micro electret. Saw a mention of this in a very obscure journal in 1995, plus you can even tune it so that it “looks” like an LED lamp.
Very short range though, less than 100 feet but works whenever the target is using their oven, power strip etcand it fits inside a standard panel mounting neon using its wiring as the antenna.
The newer versions even incorporate a micro randomizer into the “electret” and can’t be distinguished from background noise easily even using an SDR and crypto gear.
Got home from work and immediately watched The Conversation, and I was not disappointed.
I see it two ways, if you use an Oscope with probe and then over a speaker play a tone, if you scan the room with the probe first and then play the tone and scan while its playing you will be able to pick up on any microphone by the electric field it would create. this will detech anything with a mic and as per military standards, you remove all recording devices from sensitive areas. this will still find burst and self contained recorders or even items that are turned off because the mic is still creating an electric current and thus a field that can be deteched.
sean – I think this scenario would apply to dynamic mics from the old days. Maybe even carbon mics. But bugs today like the electret electrostatic mics that use capacitance instead of a electromagnet which would cause a field even when off.
https://upload.wikimedia.org/wikipedia/commons/5/57/Electret_condenser_microphone_schematic.png
A typical electret microphone preamp circuit uses an FET in a common source configuration. The two-terminal electret capsule contains a FET which must be externally powered by supply voltage V+. The resistor sets the gain and output impedance. The audio signal appears at the output, after a DC-blocking capacitor.
As mentioned above, a simple NJD can be defeated by a bandpass filter between the antenna and the first junction (amplifier or mixer). Most radios include such a filter to prevent front-end overload in the presence of a strong out-of-band signal. A better junction detector looks for two-tone intermodulation products, because those mixing products will be next to the probe signals in frequency. If you sweep the probe signals in frequency, you will see the intermod products only when you are within the passband of the front-end filter. This provides good differentiation between radios and rusty fences/LED lights/etc.
One of the reasons there are not many amateur NJDs is that your probe signal needs to be relatively harmonic-free (for the harmonic version, intermod-free for a two-tone version), but the transmitter will have much higher powers than the junction you are trying to find. At a fixed frequency this can be done with sufficient shielding and a good filter, but it becomes an interesting design problem if you want to make a swept probe. YIG filters make great swept filters, but they saturate at a relatively low power, so you would need an amplifier after the filter, which brings you back to where you started. One implementation is to monitor the output spurs and actively cancel them. You will also want to suppress the probe signal(s) in the monitor circuit to prevent the monitor from generating spurs–if you ‘cancel’ the spurs generated in the monitor, you will make the output spurs worse instead of better. Alternatively, you can take advantage of the amplifier linearization techniques developed for cellular basestations, but making those methods work over wide tuning ranges is difficult.
You are the master! Could you give some references to me at juzhang74(AT)foxmail.com? THANKS
@bentwookiee says:
“September 21, 2017 at 6:33 am
Got home from work and immediately watched The Conversation, and I was not disappointed.”
————————
Yes when I listen to Harry Caul play that sweet sax it brought back fond memories of this https://youtu.be/xpC2hYK8dyU You’d have to be 100% mashugana not to be moved by this very gifted artist… Steven Eugene Grove aka Euge Groove.
If anybody would like to watch the full-length movie right here, it’s about 2 hours long. If you have a $1.99 USD (1.47 BP 1.67 Euros) kicking around in your wallet (i.e. credit card or PayPal) YouTube will let you watch it right now. Very good movie!
https://www.youtube.com/watch?v=lOM73aguxMA
you’re on the list, because you’ve visited an unusual site: http://67.225.133.110/~gbpprorg/mil/
A really great book, must-read: “Odyssey of an Eavesdropper”, autobiography of Martin Kaiser, about his career in early electronic surveillance. There’s a CSPAN interview of him around. The inspiration for The Conversation and Enemy Of The State.
Anyone thinking about working for the Feds might benefit from reading about his ordeal with the FBI. The government gets more like the mob and less professional year after year.
http://martykaiser.com/index.htm
One of you HD folks should do a review of it. I found it just as compelling as Clark’s “Ignition!” in its technical content.
Mikey – Here’s Marty’s website: http://www.martykaiser.com/
Mikey – Sorry Mikey I don’t read to well :-<
hope i can harness the power of NLJD ,for detecting IED and remote triggered road side bombs,How far can the NLJD pick signals from if improved
Gehsma – Not that far I’m afraid. You’d have to be right over the IED. You could use a robot with a NLJD mounted on it to protect personnel. Just put a cellphone jammer on it to protect your expensive robot too. Or if you have the multiple $$$ (deep-pocket budget) go out and purchase this new LASER TDLAS gadget (developed for you know who) that can spectrum analyze particulate gasses (i.e. explosives) from a long way away. http://www.sciencedirect.com/science/article/pii/S058485471500021X
There are NeSSI projects and other MEMS systems that last I recall were lapel size so could be worn out in the open and not be so obvious. I recall watching at seminars back around 2005 or so though were for military applications and maybe others in government and I am not finding links at this time to reference. I see there is an electronic nose wiki and I was thinking of investing in a Z-nose, though they’re not much unlike the Phazir or Truscan devices I’ve used and developed methods for that are rather large compared to the microsize or maybe even nano-size tech market. Thanks for your links also, info and work around for posts. Interesting info.
Jesus H. Christ! HaD is using targeted URL domain blocking? WTH – Why???!!!
This is the 4th posting of the same topic involving a HACK workaround to allow on the fly post-EDITABLE HaD postings – I had to use Google Shortener to get it to work – MAYBE! https://goo.gl/bzkFYy
Moderator – don’t bother posting the other three posts now. It’s now moot and it will just clutter this thread. I think this was a bad judgement call to block URL domains. Fix the post EDIT problem and we won’t need to hack workarounds like this…
The link doesen’t work for me
Tried the Wayback Machine? We don’t control the Internet, we just post the links.
Hi all. Are there any laser guided non linear junction detectors?
Can NLJD be modified to detect smaller, micro or nano, semiconductors?
“check lamp for RF emissions”
🤔 But aren’t a lot of lamps WiFi now? Do I have to run a WireShark scan and port scan and vet the firmware now too?
I think I’ll just use the ‘cone of silence’