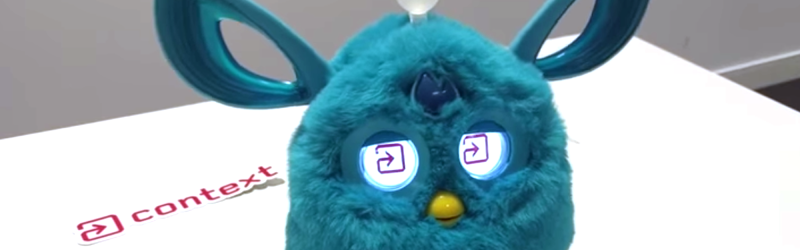
Long before things “went viral” there was always a few “must have” toys each year that were in high demand. Cabbage Patch Kids, Transformers, or Teddy Ruxpin would cause virtual hysteria in parents trying to score a toy for a holiday gift. In 1998, that toy was a Furby — a sort of talking robot pet. You can still buy Furby, and as you might expect a modern one — a Furby Connect — is Internet-enabled and much smarter than previous versions. While the Furby has always been a target for good hacking, anything Internet-enabled can be a target for malicious hacking, as well. [Context Information Security] decided to see if they could take control of your kid’s robotic pet.
Thet Furby Connect’s path to the Internet is via BLE to a companion phone device. The phone, in turn, talks back to Hasbro’s (the toy’s maker) Amazon Web Service servers. The company sends out new songs, games, and dances. Because BLE is slow, the transfers occur in the background during normal toy operation.
Looking at BLE services, there was a common DFU service for uploading firmware and an interface for sending proprietary DLC files. They found an existing project that could send existing DLC files to the device and even replace audio in those files. However, the format of the DLC files appeared to be unknown outside of Hasbro.
Attacking the DLC files with a hex editor, some of it seemed pretty obvious. However, some of it was quite elusive. The post has a great blow-by-blow detail of the investigation and, as you can see in the video below, they were successful.
Hasbro didn’t seem too concerned about the security ramifications because an attacker would have to have proximity to the toy. It isn’t hard to think of cases where that’s not a great excuse, but we suppose it does cover the most common things you’d worry about.
We talked about the partial exploit of the Furby Connect earlier. If you have an older Furby in the attic, you can always turn it into your next robot.















I think you killed their site…!
When the original Furby came out, it spoke up in style that reminded me of a certain overly cheerful Muppet. Whose toys were equally difficult to find.
It happens the Feds were worried that someone would buy one for his kid, and instead of giving it to the kid, he would keep that one, and buy another. He’d leave it on his desk at a certain TLA (Three Letter Agency), and it would listen to everything that would happen there. The cleaners would then ask it to talk, and then record that.and its recordings would be sent to various and sundry agencies out there who would want such information.
Naturally since most officers of that agency do have common sense, even if their bosses do not, and the things were not seen at work.
Not to mention that the Furby never really learned anything. It was all programmed.
Now I want a machine learning furby with natural language processing picked up from interaction and also facial recognition of its user. For a start, it wouldn’t be hard to hook it up to a pi with alexa and a voice mod. Still creepy.
[blockquote]On January 13, 1999, it was reported the National Security Agency of the United States banned Furbies from entering NSA’s property due to concerns that they may be used to record and repeat classified information, advising those that see any on NSA property to “contact their Staff Security Officer for guidance.”
Roger Shiffman, the owner of Tiger Electronics, stated that “Furby has absolutely no ability to do any recording whatsoever,” and would have gladly told the NSA this if he was asked by anyone from the spy agency. Additionally, Dave Hampton demonstrated that Furby’s microphone can’t record any sound at all, and can only hear a single monotonous beep if a loud sound is produced around Furby, and no words or waveforms can be made out at all. He too was never questioned by the NSA, and he could have answered both questions easily. The ban was eventually withdrawn.[\blockquote] Source: Wikipedia
That went well (/sarc) Next will use carets rather than brackets… :(
Indeed. However, it was originally the CIA first. Technically the NSA has the management of the military, despite the fact that the CIA has administrative rights over them.
drwho8 – I admit that the No Such Agency (ideally CSS division) was extremely paranoid about this toy when it was trendy. They were really paranoid about PRC (China). They were not far off as their MSS is really sneaky and not beyond such shenanigans. Ft Mead (The Puzzle Palace?) is full of overt employees who might do something careless like this. However, Langley has some overt employees too to but are a bit more savvy about this kind of stuff, as this would be something they might construct too for their NCS folks. Their DS&T geeks would have scanned these things and figured out how to send disinformation back to Beijing. Hell, they probably gave NSA the intel that they might be bugged (as a really stupid cruel joke of course). There is an ongoing TLA rivalry you know…
I would think the 7th floor would have a holy fit if this happened at Langley and heads would roll. It would make the firings back in the late 70’s to early 80’s look like child’s play. Almost as bad as the unauthorized chat room on the mainframe incident. So maybe you’re right and it did happen at Langley first, but they just sanitized it out of any news media reports. I heard it happened at the E-Ring too (Pentagon?). It was a cute toy any secretary might think was wholly innocent. Here’s a E-Ring GLG-20 employee that decoded a Furby transmission to PRC in Mandarin with Droggin’s decoder wheel… See below for that (/humor)
Tiger Electronics is correct. The ones they made WERE innocent. It was just the ones the MSS (China?) modified and got into targeted people’s houses/jobs were the ones that were suspicious. Remember Tiger Electronics had them made in China. Who knows how many were tampered with and infiltrated into USA some how.
This may make for a cool HaD project to use as a baby monitor or senior citizen thing. Or even a Echo Dot or Google Home/Alexa gadget. Maybe just use a remote speaker/mic in the Furby and connect it to your Windows 10 Cortana?
GLG-20 Employee
https://www.youtube.com/watch?v=Gl1FHUIWNzY
And no I did not butcher this one L. :-)
If your into hacking Furbies check out this project: https://www.facebook.com/openfurby/