In the old days, a physical button or switch on the dashboard of your car would have been wired to whatever device it was controlling. There was potentially a relay in the mix, but still, it wasn’t too hard to follow wires through the harness and figure out where they were going. But today, that concept is increasingly becoming a quaint memory.
 Assuming your modern car even has physical buttons, pushing one of them likely sends a message over the CAN bus that the recipient device will (hopefully) respond to. Knowing how intimidating this can be to work with, [TJ Bruno] has been working on some software that promises to make working with CAN bus user interfaces faster and easier. Ultimately, he hopes that his tool will allow users to rapidly integrate custom hardware into their vehicle without having to drill a hole in the dashboard for a physical control.
Assuming your modern car even has physical buttons, pushing one of them likely sends a message over the CAN bus that the recipient device will (hopefully) respond to. Knowing how intimidating this can be to work with, [TJ Bruno] has been working on some software that promises to make working with CAN bus user interfaces faster and easier. Ultimately, he hopes that his tool will allow users to rapidly integrate custom hardware into their vehicle without having to drill a hole in the dashboard for a physical control.
But if you’re the kind of person who doesn’t like to have things done for them (a safe bet, since you’re reading Hackaday), don’t worry. [TJ] starts off his write-up with an overview of how you can read and parse CAN messages on the Arduino with the MCP2515 chip. He breaks his sample Sketch down line by line explaining how it all works so that even if you’ve never touched an Arduino before, you should be able to get the gist of what’s going on.
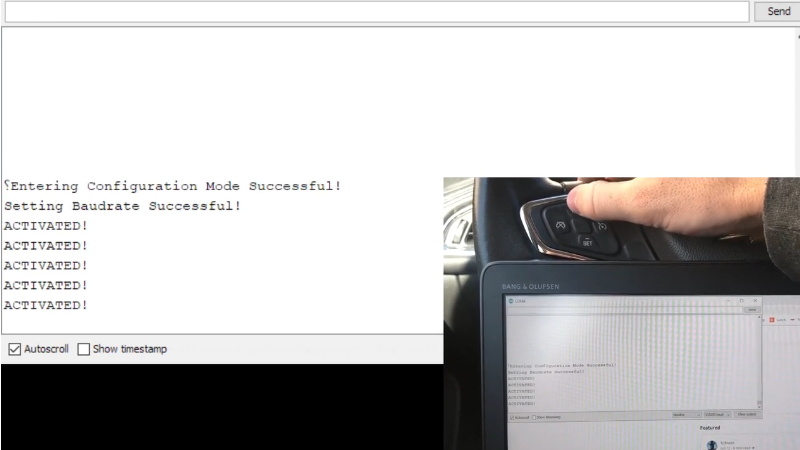
As it turns out, reading messages on the CAN bus and acting on them is fairly straightforward. The tricky part is figuring out what you’re looking for. That’s where the code [TJ] is working on comes in. Rather than having to manually examine all the messages passing through the network and trying to ascertain what they correspond to, his program listens while the user repeatedly presses the button they want to identify. With enough samples, the code can home in on the proper CAN ID automatically.
The upside to all this is that you can activate aftermarket functions or hardware with your vehicle’s existing controls. Need an example? Check out the forward-looking camera that [TJ] added to his his 2017 Chevy Cruze using the same techniques.















I’m wondering what the B&O device is.
HP laptops have B&O sound…
And this label improves the sound quality?
Kinda, sometimes is marketing blurb, but on my HP the difference between windows and Linux is like day and night, I wonder if they use some kind of tuning to make the cavity of teh laptop resonate…
Bang and Olufson
No. Olufsen. It’s Danish, not Swedish.
This is a fantastic idea. Great way to discover hidden information!
And you will not have to run your CAN bus backwards either. ;-)
So you modify your new cars software, the transmission goes and “Sorry no repair, you’ve voided your warranty.”
This doesn’t modify the car’s software. It is just listening for the button press event on the CAN bus.
Modifications do not void your warranty, this is flat out wrong. They have to prove that the modification caused the fault which would be difficult to prove. You may end up in front of a judge defending this however.
And if you, who make $50,000 a year end up in front of a Judge against a company that makes $5,000,000,000 a year how do you think that is going to go? If the company wants to screw you all you can do is grit your teeth and hope they use lube, that’s life.
Only in muhricah
Except for the whole, “arbitration” scheme so things don’t get even get as far as a judge.
Instead of “firewalling” the can bus (which would require cutting wires and so on) why not just get the arduino to send the same code again…. and thus switching off the factory feature milliseconds after the long press. But, be careful here because if your code goes nuts and send say brakelights off when they indeed were meant to be on it could cost lives. Test it really really well and make sure the power supply is well stabilised so no noise spike can play havoc with your micro.
well the usual use case here would be to hijack the factory play pause next track etc and send them to your own player (in my case android auto on a pi) without disturbing the factory unit. even if you send an opposite command a split second later it will still have undesiarable effects. in my case the can bus for media stuff is seperate to the can bus for powertrain/breaking etc so no safety issues, i just have to break the canbus at the stereo so the stereo doesnt see an of the controll messages, but everything else gets through.
I havnt watched the video yet, but i resume the author is doing similar.
I see, its good that the busses are separate, I didn’t know that. Makes a lot of sense.
its actually a fairly interesting topic these days, as cars get more complicated. here is an overview of an almost current bmw 3-series . Most cars I encounter are set up in a similar fashion .(im an auto electrician in the UK)
https://www.e90post.com/forums/attachment.php?attachmentid=185111
Hmmm did I count that right? 4 busses? I haven’t looked at modern cars since circa 2000. It figures.
this is superb, I manually went through my canbus logs to i-d the i-drive controller messages and steering wheel controlls it was very very tedious with all the other traffic on the bus. Interestingly I just bought a teensy with the dual canbus to do a man in the middle and sanitize certain messages. I think you have just saved me a tonne of work, thanks to the OP and author :)
Is the link available without me having to sign in and agree to god knows what in the terms and conditions?
I would like to read this but not enough to agree to give them my details.
It’s Medium, but you just have to click the little x in the sign-in hassler popup.
Cheers. I could not get rid of it this morning but clicking the X works this afternoon, go figure. :)
Does anybody find the source code for his CAN ID guesser (there is just a canano github project that is just a sniffer)?
Thanks!
For hacking CAN bus I recommend using this adapter and software: https://rs.canlab.cz/?q=en/usb2can_triple