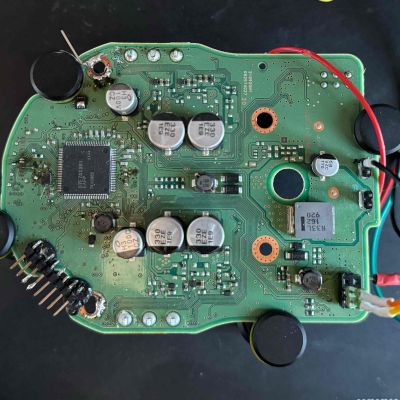
If you find yourself working with CANopen CC networks, you might find yourself in need of a tool for monitoring what’s happening on the wire. [Michael Fitzmayer] whipped up a piece of software to fulfil just that role.
CANopenTerm might be named after the CANopen standard, but it’s really a terminal-driven tool for working with CAN buses in general. The software is built for real-time use, allowing sniffing raw frames on the wire, tracing, and probing of nodes, all from within the console. It’s also possible to add scripting via Lua or Python for more advanced work, as well as do protocol-aware inspection if that’s relevant to your use case. The key idea of the software is to be fast and scriptable to suit a given need, rather than bogging everything down with a heavy GUI interface that’s slower to work with.
If you aren’t afraid of getting into the nitty gritty with CAN and like lightweight text-based interfaces, this might be the tool for you. We’ve also explored some other CAN visualization tools lately, as well. Ultimately, there is a lot of machinery out there running on some variant of CAN or other, so it pays to know how to work with it. If you’ve got your own projects cooking up in this space, don’t hesitate to let us know on the tipsline!