There’s long been much handwringing around Halloween around the prospect of pins, needles and razor blades being hidden in candy and passed out to children. On the very rare occasion this does happen, the outcome is normally little more than some superficial cuts. However, for 2019, [MG] has developed an altogether different surreptitious payload to be delivered to trick or treaters.
Consisting of a small USB device named DemonSeed, it’s a HID attack gadget in the genre of the BadUSB devices we’ve seen previously. When plugged in, the unit emulates a USB keyboard and can be programmed to enter whatever keystrokes are necessary to take over the machine or exfiltrate data. Files are available on Github for those looking to replicate the device.
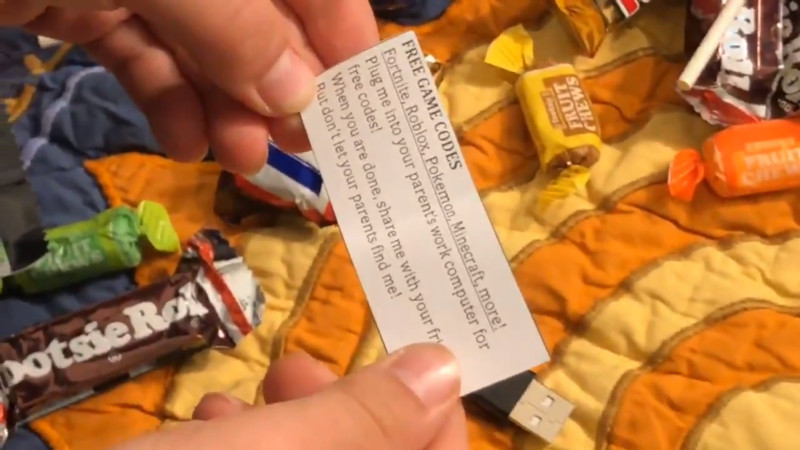
The trick here is in the delivery. [MG] has produced a large quantity of these small devices, packaging them in anti-static wrappers. The wrappers contain a note instructing children to insert them into their parent’s work computers to access “game codes”, and to share them with their friends while hiding them from adults.
The idea of children brazenly plugging hostile USB devices into important computers is enough to make any IT manager’s head spin, though we suspect [MG] doesn’t actually intend to deploy these devices in anger. It serves as a great warning about the potential danger of such an attack, however. Stay sharp, and keep your office door locked this October 31st!















Quick dirty solution to most HID attacks is to perform a test for each new keyboard/mouse that is plugged in.
For example, we can require it to enter a randomly generated string of characters, or navigate a “puzzle”. Before it can be used for anything else. (The OS informs the user of what needs to be typed/clicked in. Ie a rubber ducky doesn’t know it.)
Then the device will be added to the OS’s list of “trusted devices”, since devices typically have serial numbers, manufacturer part numbers, etc to identify them with. Meaning that you don’t need to perform this test for devices that has already passed it.
Ie, a USB “thumb drive” looking device can’t get passed our test, therefor it can’t perform its attack.
In the end, IT security 101, Don’t just blindly trust a new device.
This is similar to bluetooth pairing — makes sense, and probably cuts a vast majority of malware devices out of the loop. If you plug in a USB drive and it’s asking you to type a pairing key into it, most people would be puzzled at the very least.
It wouldn’t stop compromised keyboards (i’ve wondered what would happen if someone bought a bunch of cheap keyboards, then carefully opened / compromised them, and returned them to the store / amazon… slow going, but guaranteed compromising of a random computer).
Yes, Bluetooth devices largely do this already, so why not do the same for USB.
It isn’t hard, and it vastly increases the security.
Though, making a rubber ducky as a keyboard, and then “waiting” for the user to authenticate it, is though a trickier problem. But at least we got rid of the USB rubber ducky problem.
2fa for a mouse would be such a nuisance to the average user, people would complain until it was patched out or an option that defaults to off.
Frankly speaking, it would likely be as trivial as “click this button to authenticate the device”, but it is just in a random place. And too many clicks elsewhere would make the OS dismiss the device as untrustworthy.
It would likely only take a couple of seconds more most users, and it is a one time affair for each device.
And don’t forget that in Windows, you already have to make a single click to dismiss the “This device is ready” notification.
[zee]’s argument that a user can’t do what they all have to and already do isn’t that convincing to me.
Then don’t frame it as a security measure.
“It looks like you plugged a mouse in. To make sure that it is compatible with MS Windows, please click the ‘use this mouse’ button.”
Alternate phrasing: “to make sure it works”, “to ensure it is properly installed”.
While the popup is open, disallow clicking on anything else (except maybe a “don’t use this mouse” button). Maybe have a visible countdown, which ends by disabling the mouse.
“In the end, IT security 101, Don’t just blindly trust a new device.” True enough but most 8 year old trick or treaters aren’t IT Engineers (and usually their parents aren’t either.)
My statement were in regards to OS design, not about the user.
The OS itself shouldn’t just trust a new random human interface device and allow it to input whatever it desires.
Now, this isn’t the case when it comes to most OSes, but seeing a change for the better here would be nice.
Well I can’t argue with you there this is a security hole, but as of today this halloween hack is a good method of attack, the only thing worse would be giving out USB killers.
Easy. In the accompanying note for how to hide the device from their parents, include instructions for the kiddies for how to bypass the OS security.
Not a bad idea however, I’ve had a few usb keyboards that don’t have anything unique about them but the USB port they are plugged in before. Seems some cheap keyboards at least just have the same hardware and firmware all the way down even in different cases. (How true that is, hard to know. Also possible I missed read something as I wasn’t actually looking for that just verifying they all worked before passing them on to a computing charity,)
So it wouldn’t work that well as they can just pretend to be common devices and keep cycling through the list till they hit one you have trusted – at least if they don’t have true unique ID’s just make/model/hid type descriptors
best simple solution I can think of is to just not having the now ubiquitous port available on your machine directly. A simple hardware cable modification to change the ports on the computer to anything else with enough pins as an adapter would work (so of course you keep your adapter cable with you). But one step better would be to have the ports but only have them live if you unlock the usb ports manually – either with a software command to enable them or a physical key type system.
Seems like overkill to me all the way around as direct physical access to the machine being required means the risk is low. No child of mine would get anywhere near my important computers hardware, these days who doesn’t have a computer for the young/technically challenged members of the family/house to use.
Of course if you need to be that paranoid about somebody else plugging unsafe devices into your computer then by all means live with the slight inconveniences. I like the Idea of HID pin checking. Just not sure it actually solves the problem at all the way the keyboards are made..
Yes, manufacturers being lazy and not adding serial numbers to their products would be a problem.
Though, the list of trusted devices shouldn’t be universal. Ie, there is no golden key. (since then all rubber duckies would just use that.)
So instead, the list would be made on each individual computer. It is simply the bluetooth paring idea, but for USB devices.
So scanning through a list of “common” devices would be fairly futile. And the OS could then just inform the user that the device acts suspiciously. (in case the user didn’t consider the endless pling/plongs the OS would make as a direct result from the repeated attempts at gaining access.)
After all, a lot of computers see 1 keyboard in their whole life….. (ie, the list of trusted keyboards would have 1 entry.)
The noise might be the deal breaker assuming the folk using the computer are not either in ear shot or not going to turn the sound off, but with all these things it only has to work a small percentage of the time to be really worth it. Not like the chip actually costs anything meaningful.
An OS should detect and stop trusting constantly hotpluged.. but windows won’t do anything that smart by default. Also not like it needs to work in seconds.. Give a kid something to plug in as in this scenario and it could potentially stay in the computer for hours or even for the lifetime of the computer unnoticed, so one bong every 15-90 mins and it would probably get there in a few days..
For me though I’d make this device a pass-through with instructions to plug it in between the usb hub/keyboard and PC if such pairing systems came in. An extra usb hub listed isn’t going to be noticed at all i’d say. And a hub skimming and inserting fake key presses with authenticated hardware is easy to do. Could even make it it more fun but adding the cheapo LCD screen so there is a game you can play with that keyboard – then odds are the parents wouldn’t consider it to be untrustworthy – it is what it says it is a little usb powered games box that uses keyboard input.
The thing with a test is that is can quickly become mindbogglingly impossible to brute force one’s way past.
For an example, if the string only contains alphanumeric values. Lets say A-Z and 0-9, and cap sensitive too. That means we have 62 different characters to pick from for each position in our string.
If our string then contains a casual 8 characters, then we have 2.1834×10^14 combinations. Or about 220 trillion. So making attempts 1 million times a second would on average only succeed once every 3.5 years. (Except, detecting USB devices is far slower then this, so it would likely take thousands of years.)
Faking a device ID on the other hand, then we need to find the correct manufacturer ID, model number, and serial number. (Here the lists are far shorter, but there is still a few hundred manufacturers, each having tens of models, and tens of thousands of serial numbers. (if they actually apply unique serial numbers to their products.))
So finding the correct ID is also hard, not to mention that now we likely have two USB devices claiming to be the same device. That isn’t suspicious at all…….
To solve the problem of making a pass through rubber ducky on the other hand is a different kind of problem to fix, it falls in line with an exploited keyboard. There are non user friendly ways of fixing this, like doing the alphanumeric test each time one does something in regards to system settings, opening the command prompt, or install applications, runs scripts, etc, etc….
Though, in the end, the most powerful method of defeating security is to fool the person using the computer. This is sometimes excessively trivial.
But it doesn’t change the fact that Windows, Linux, OSx, and other operating systems should probably add a paring feature to their systems, since the HID attack is something plaguing the industry, and the simplest fix to the majority of the attacks is down right trivial.
(After all, tell a sysadmin that you have software on a USB key, they aren’t going to consider it out of the ordinary. Give them a USB passthrough game thing, or similar, well it isn’t confidence instilling… (though, the USB killer is also a problem…))
…says the person who has never worn out a keyboard, nor had one fail.
I am not saying that keyboards are indestructible.
Just that some people don’t use their computers enough for a keyboard to wear out before the user changes to a new computer and usually getting a new keyboard for it, starting at square one again.
Though, then there is also people who change keyboards just for the heck of it.
And others who spill coffee over it, or stab it with a soldering iron on accident.
Not to mention random failures, and actual wear.
But considering how most keyboard switches have MTBF values in the order of tens of millions of actuations, then that will equal quite a bit of typing for most people. Unless one hammers on the keys like it were a game of whack a mole of cores…
Only downside with this authentication method would be the bar code scanners that act as keyboards.
But one could add an option to add this device to the list of trusted devices since one knows what the device is.
One should probably also add a message to this pairing process, informing the user why the process is done.
Another “bigger” downside is that one can’t any longer pull the “hidden wireless mouse/keyboard” prank on people at work/school as easily.
Wow, that’s a really good idea. Complicates all the hacks but you could whitelist in udev rules if you’re on Linux
Reminds me of Soupy Sales back in the day, telling his TV kids to sneak into their parent’s wallets and send him all the little green pictures of George Washington they found in there.
Still promulgating the “bad treats” myth … get over it, it’s not a thing … https://arstechnica.com/science/2019/10/forget-poisoned-candy-and-razor-blades-heres-the-real-halloween-horror/
The article doesn’t say that it is being made, only that it is a reasonable possibility.
“The idea of children brazenly plugging hostile USB devices into important computers is enough to make any IT manager’s head spin, though we suspect [MG] doesn’t actually intend to deploy these devices in anger. It serves as a great warning about the potential danger of such an attack, however. Stay sharp, and keep your office door locked this October 31st!”
My office was in a very secured building. Only children allowed belonged to the CEO (his company). Only hardware allowed is what IT provided. Now if we had centrifuges downstairs, I’d be worried, but otherwise there’s something to be said about a controlled environment.
Su mortu mortu or is pnixeddas https://sardanews.it/images/2014/panixeddasbn.jpg is a tradition in Sardinia and looks like a lot the Halloween tradition of kids asking for sweets october 31st ‘ The traditional bisuit is called ossus de mortu, deadàs bone https://blog.giallozafferano.it/dolcesalatomiky/wp-content/uploads/2013/01/DSC_0088.jpg
Besides, yesterday I opened a chocolate box and the chocolates tasted a bit ‘dry’ – then i looked at the box and there was written ‘Best before: 01-12-2011’ – so I have a weapon to get rid of those pesky kids :-)
Any child touching my work pc’s reveives a proper spanking. They know and they don’t even think about it, besides that, they have their own pcs. No hardware solution needed.
Do you share a network with your kid’s devices? Once inside the network, cracking into your device would be trivial.
Depends a huge amount on your home network setup. Even if you do share with the right firewalls in place remote connection to the compromised machine would be almost impossible as would that machine compromising any further computers.. Now all the embedded crap gluing the network together is probably riddled with bugs the manufacturers are not patching or making any effort to draw you attention too. So trust of your switches, routers, extenders (damn the list is soo long) is a big issue even with more secure home network setups – Which means I still wouldn’t want hostile devices on the same network even with good security practices, but theoretically its not easy to exploit.
For myself stuff I don’t trust is on a guest network separate from the trusted stuff. As safe as feasible.
No, work machines have their own 4G/3G modem payed by the employer.
The private network uses a fritzbox with a guest network separated from the rest of the network and devices cannot connect to each other and of-course a pi hole with extra blacklists. Only registered mac addresses are allowed to connect anyway.
And no smart stuff / IoT things connected devices in this house, no exception.
RJ port of the smart TV is filled with hot glue just in case.
Usb devices dont have a unique identifier just a vendor en product id.
So you can only whitelist a for example microsoft keyboard and after that any microsoft keyboard wil work (this is simplified but you get the point)
https://docs.microsoft.com/en-us/windows-hardware/drivers/install/standard-usb-identifiers
On top of that since the vendor and product ids are know you can emulate any device you want. If its a work environment start with the ids of the big sellers like dell HP etc.
Bit of a creepy hack. Reminds me of the “wicked witch” (Fortune teller) that tricked a girl into stealing over $100k of jewellery from her parents.
But yeah. Kids would totally do stuff like this. They’re like the evil maids that you can’t fire, even though they don’t clean up unless you tell them 1000 times, & there’s no easy way to install security software on them.
You would have to be logged into the computer to even choose what action to take. I always lock my laptop when I get a cup of coffee just in case the animals or children accidentally delete something.