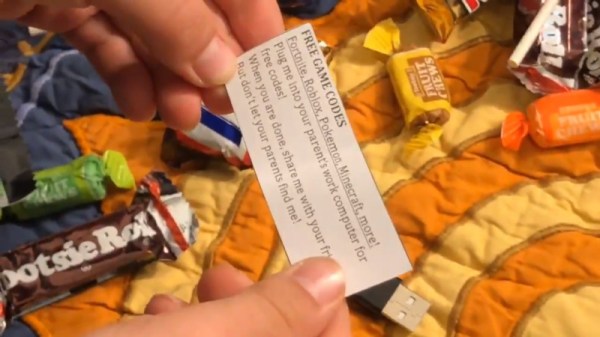
Most people know that they shouldn’t plug strange flash drives into their computers, but what about a USB cable? A cable doesn’t immediately register as an active electronic device to most people, but it’s entirely possible to hide a small, malicious microcontroller inside the shell of one of the plugs. [Joel Serna Moreno] and some collaborators have done just that with their Evil Crow Cable-Wind.
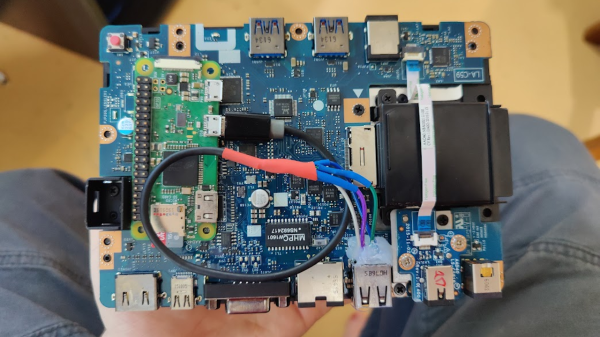
This cable comes in two variants: one USB-A to USB-C, and one with USB-C to USB-C. A tiny circuit board containing an ESP32-S3 hides inside a USB-C plug on each cable, and can carry out a keystroke injection attack. The cable’s firmware is open-source, and has an impressive set of features: a payload syntax checker, payload autocompletion, OS detection, and the ability to impersonate the USB device of your choice.
The cable provides a control interface over WiFi, and it’s possible to edit and deploy live payloads without physical access to the cable (this is where the syntax checker should be particularly useful). The firmware also provides a remote shell for computers without a network connection; the cable opens a shell on the target computer which routes commands and responses through the cable’s WiFi connection (demonstrated in the video below).
The main advantage of the Evil Crow Cable Wind is its price: only about $25, at which point you can afford to lose a few during deployment. We’ve previously seen a malicious cable once before. Of course, these attacks aren’t limited to cables and USB drives; we’ve seen them in USB-C docks, in a gaming mouse, and the fear of them in fans.
Thanks to [rustysun9] for the tip!