[Nick Price] had a wonderful concept for a DEFCON badge: a device that worked a lot like a directional Geiger counter, but chirped at detecting WiFi deauthentication packets instead of radiation. That’s a wild idea and it somehow slipped past us last year. Why detect such a thing? Well, the WiFi deauth attack is a kind of invisible toxicity, effectively jamming wireless communications by forcing users to be constantly tied up with authentication, and this device would detect it.
A few things were harder than expected, however. To make the device directional, [Nick] designed and built a PCB Yagi antenna but it wasn’t practical. Not only was it far too big, it would also have required going to four layers on a PCB that was already expensive. The solution he settled on — inspired by a friend’s joke about just dropping the badge into a Pringles can — was to surround the PCB omni antenna with a copper pipe end cap from the plumbing section of any hardware store. [Nick] figured that soldering that to the ground plane should result in a simple, cheap, and attractive directional antenna mod. Did it work? We’ll all have to wait and see.
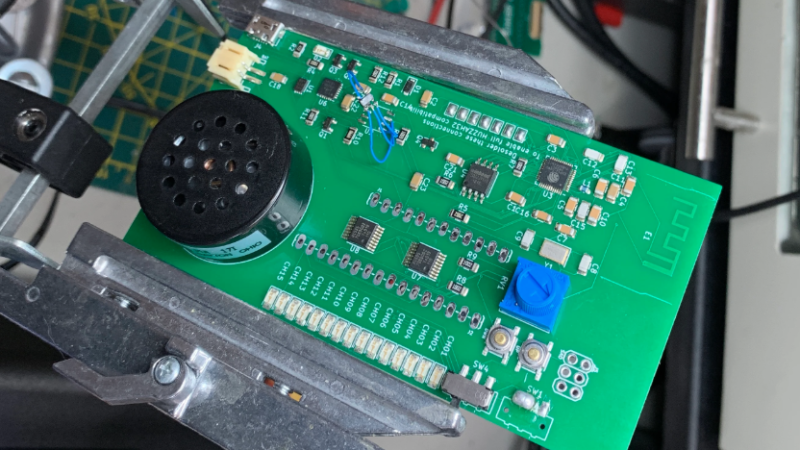
Sadly, [Nick] wasn’t able to finish in time for last year’s DEFCON. Hardware revisions mounted, and fabrication times for his specialized PCB were longer than usual. Worse news is that this year’s is cancelled, or rather is going virtual, which means he’s going to have to deauth himself. The good news is that now he’s got another 12-month extension. Watch the brief video of the functional prototype, embedded below.
https://www.youtube.com/watch?v=JWmiI62Fp3Q
The Geiger counter might be vintage hardware, but it has an endurance and appeal that is undeniable. It’s also been brought into the modern hobbyist era with this touchscreen-enabled unit with a beautiful enclosure and slick UI.















There HAS to be a better word for that. Or coin one now. Retract Frame. Cast-off Frame. Anything but deauthentificationing! (This is orders of magnitude worse than edge case and use case).
Aunthentication’nt-ifier.
“Deauthen-ator”
-Dr. Heinz Doofenschmertz
And now… to deauthenticate every Wi-Fi user in the TRI-STATE AREA!!
d16n
Deauth frame. It’s easy to abbreviate.
DEATHFRAME
Might be a name for a death metal band too. :-)
Now we’ve made that connection, this dude certainly sounds like he’s having trouble connecting to wifi, and I think a few tracks later on he’s got a corrupted hard disk and to top it all, it sounds like ransomware virus angst in the final track.
https://www.youtube.com/watch?v=4Tdo6y2JJMQ
Great idea. RF routing is kinda horrible
So this thing tracks down the hotspot disabler at your local convention center? Good. Honestly this should be considered jamming and any AP offering this feature confiscated and destroyed at the docks.
> any AP offering this feature confiscated and destroyed at the docks
So all of them (WPA,WPA2), the design flaws are part of the standard.
And WPA3 thanks to “dragonblood” vulnerabilities (again design flaws in the standard), allow attackers to perform downgrade attacks and side-channel attacks, enabling brute-forcing the passphrase, as well as launching denial-of-service attacks on Wi-Fi base stations (you forge a few dozen very computationally expensive ‘Auth-commit’ messages, and the AP is unable to do anything else at all).
(ref: https://papers.mathyvanhoef.com/dragonblood.pdf )
So maybe some future WPA 3.1 standard will fix the currently known design flaws, but that will be require new hardware. In theory it could be a firmware update, but where are the new sales in that.
It’s not about design flaws. It’s about the commercial access points that intentionally issue deauth’s on other nearby networks to render them unusable. Hotels tend to use them to stongarm conference attendees into paying through the nose for hotel wifi.
So then we confiscate and destroy any Wi-Fi AP that includes this feature.
Of course, then hotels will just install custom firmware to add the feature, so we’ll need to require all Wi-Fi APs to have locked-down, signed firmware with tamper detection so that nobody can add that feature you don’t approve of. Better restrict bare Wi-Fi transceivers to licensed OEMs too, so that a third-party can’t build a dedicated deauth module, so no more ESP-8266 or the like.
Remember, just because you own hardware doesn’t mean you “own” it! There’s always someone who knows better than you and will say you can’t do what you want with your own property.
Or what if you had a device fake a large number of networks and clients so the deauthing device wastes most of its bandwidth deauthing fake clients?
I like the cut of your jib.