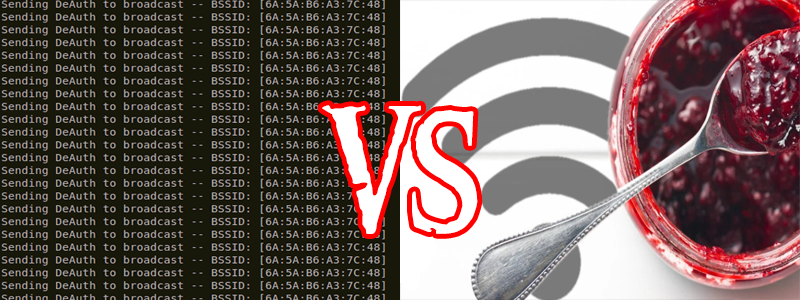
Terminology is something that gets us all mixed up at some point. [Seytonic] does a great job of explaining the difference between WiFi jammers and deauthenticators in the video embedded below. A lot of you will already know the difference however it is useful to point out the difference since so many people call deauth devices “WiFi Jammers”.
In their YouTube video they go on to explain that jammers basically throw out a load of noise on all WiFi channels making the frequencies unusable in a given distance from the jammer. Jammers are also normally quite expensive, mostly illegal, and thus hard to find unless of course you build your own.
WiFi deauthentication on the other hand works in a very different way. WiFi sends unencrypted packets of data called management frames. Because these are unencrypted, even if the network is using WPA2, malicious parties can send deauthentication commands which boot users off of an access point. There is hope though with 802.11w which encrypts management frames. It’s been around for a while however manufacturers don’t seem bothered and don’t implement it, even though it would improve the security of a WiFi device from these types of attacks.















Heh… You just discovered this now? It’s been explicitly stated in all the specs going way back… and the complete solution to the problem was developed years before this problem was. It’s a complete non-issue. Only value here is that those trying this prank will be easy to ID so they can be caught…
Hackaday has featured several WiFi Deauthing devices over the years including one with 2 ESP8266es.
There’s also been a discussion post I believe about a US hotel chain deauthing other people’s access points (like MiFis) to force visitors to buy their own expensive wifi.
Why are people easy to ID? I’m sure people knowing what a deauth attack is will also know how to roll their MAC :)
“a US hotel chain deauthing other people’s access points” – that would be really intrusive. Got a link for that? I suppose people would retaliate by deauthenticating the hotel’s expensive wifi.
It was Marriott.
https://www.forthepeople.com/class-action-lawyers/hotels-blocking-wifi/
Not to blame netadmins but I am one and some over zealous netadmins set their management environment to auto and let them block all ad-hoc wifi within their spatial domain without regard. The purpose for a netadmins to do this is when bandwidth is being consumed in a certain area all of the APs will need to adjust their frequencies to accommodate that foreign broadcaster and keep their coverage consistent with maximum differing frequency over lap. Anyways wireless management systems require alot of tuning, consideration and also monitoring. I.E. hire people for keeps and adjust configuration to represent policy and don’t let your deployment go stagnant. Also almost every consumer endpoint supports 802.11w it’s just consumer grade APs that don’t.
I’ve known this information for a long time,however HackaDay is full of people with different skills, interests and knowledge. You will always find a post or two on HackaDay that will be trivial to you and that’s fine but it might be new information to someone else.
This
Thank you! Well said…
It’s not easy to identify someone running a deauth attack. I’m not sure why you would think it is.
Scan for excessive deauth packets in WireShark.
Alright, you now know someone is doing it. How do you find out who? There are even Android apps for this, are you going to search everyone’s phones?
if you’ve got their number, you can just look them up in the white pages. Let’s not make this more complicated than it has to be, gentlemen.
jamming can be done if you could transmit and sweep the 1.4 to 5 ghz band to jam them.
though illegal in the usa it is used by some to prevent wifi usage.
deauthentication is better for many reasons the main being password cracking.
you get the client to have to reconnect sending out the 4 way handshake that then hash crackers can be done to get the password.
the reason maybe the 802.11w is not being used is.
1. it is proprietary and the owners are demand an extreme amount of money to license just like denuvo why denuvo is going to fall.
2. government pressure to keep wifi insecure so the nsa can break in and plant magic lantern or carnivore.
i think the reason that apple was spared from government forced cracking of iphone is because of another party told the fbi how to crack it
I agree with 1. But 2, not really.
The government doesn’t need to break your wifi. It is too detectable and they can capture all your stuff in the cloud anyway, or on the way there and back. Also, this doesn’t really decrease the hackability. They can just wait for handshake frames instead of forcing them with a deauth.
3. None of the customers of the products are actually experiencing de-auth problems. So why invest in something they are not asking for. If massive de-authing becomes a problem, then the products will move.
Wifi jammer doesn’t have to be expensive. Spark gap generator generates a lot of RF noise and can wreck havoc on wide range of radio spectrum including wifi. It is still illegal because it can interfere with important radio function such as police radio and cellular system.
To be fair, the FCC would treat these the same, as shown in the case against hotels using similar Techniques to prevent wifi hotspot use on site.
It is illegal to interfere with the lawful use of a radio communication link controlled by others. This covers Jammers and packet injection.
Just so people don’t think this is some legal grey area, it isn’t, it is illegal to use on others
Slight difference tho. Jamming is indiscriminate. Deauth is targeted. Its easier to hide one than the other, making it less likely to get noticed by the FCC.
The FCC doesn’t have the budget to care about or enforce it unless someone complains. They don’t roam the streets in vans with Yagis.
LOL. Don’t kid yourself. If need be they sure do.
And even then (complaint) they usually don’t have time. I tried to report a long-time 5KW CB station and they were not interested. There were even complaints (not formal) from Australia.
In case you are interested in reconfiguring the Wi-Fi chip in a Nexus 5 smartphone into a reactive jammer, you can check out our project also available on hackaday.io: https://hackaday.io/project/26085-nexmon-jammer
Yep. HaD covers quite a broad range of topics, from metal casting to agriculture to bare-metal coding. Its unlikely that anybody is an expert in all of it. How routine or interesting a post is will vary from person to person.
That is exactly what this article was about. I’m a software guy but in the last few years I have got into the hardware scene and I love it, Without “back to basics” type posts I would never have known where to start when it came to hardware. also the video had quite a lot of information on the subject even though I knew it already someone will be learning the ropes somewhere as we are not all FPGA sensei’s with blackbelts in C/python etc.
Thanks and you were 100% correct with your assessment of this article.