Embedded Linux devices are everywhere these days, and sooner or later, you’re going to want to poke around in one of them. But how? That’s where posts like this one from [Felipe Astroza] come in. While his work is focused on the Foscam C1 security camera, the techniques and tools he outlines here will work on all sorts of gadgets that have a tiny penguin at their core.
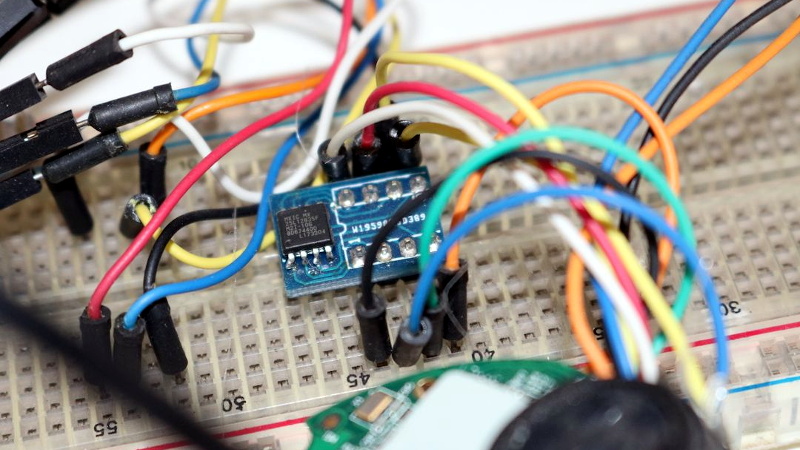
Rather than trying to go in through the front door, [Felipe] starts his assault with the nuclear option: removing the SPI MX25L12835F flash chip from the camera’s PCB and dumping its contents with a Raspberry Pi. From there he walks through the use of different tools to determine the partition scheme of the chip and eventually extract passwords and other interesting bits of information from the various file systems within.

That alone would be worth the read, but things really get interesting once [Felipe] discovers the FirmwareUpgrade program. Since the Foscam’s software updates are encrypted, he reasons that reverse engineering this binary would uncover the key and allow for the creation of custom firmware images that can be flashed through the stock interface.
Further investigation with Ghidra and friends identifies an interesting shared library linked to the executable in question, which is then disassembled in an effort to figure out how the key is being obfuscated. We won’t ruin the surprise, but [Felipe] eventually gets what he’s after.
This isn’t the first time [Felipe] has played around with the firmware on these Internet connected cameras, and we dare say it won’t be his last. For those who are really into tinkering with these sort of devices, it’s not unheard of to install a socket for the flash chip to make software modifications faster and easier.















Why wont companies that use linux firmwares give us root access? I reckon that at CCTV company that is hacker and maker friendly would become quite popular. Maybe do it like Chromebooks, which usually have a “hacker mode” screw inside, or some other explicit way of voiding the warrantee.
We don’t need corporate cooperation when we have articles like this. Customer support is very expensive, much cheaper to just leave the interesting bits readily available and let the hackers sort things out on their own. Besides it is much more fun to do a reverse engineering teardown than it is to read a spec sheet.
i loved the old arm chromebooks so much. you would only need to isolate the ‘hacker screw’ if you wanted to replace the bootloader, which i never did. the stock bootloader was compatible with replacing chromeos with debian.
not sure if this is really universal, but when i shopped for a new chromebook last year, the last generation or two from every manufacturer now has a fully-locked bootloader. i think google did a little bait-and-switch to us there, a kind of, dare i say it, anti-competitive behavior.
I’m not sure what you mean- you can replace the bootloader?
C201 club rise up
https://en.m.wikipedia.org/wiki/Libreboot
The write-protect screw was mostly supplanted by the CR50. If you disconnect the battery in the newer (2017+) devices, it disables the hardware write-protect, achieving the same goal. A lot of the new(er) models support mrchromebox’s firmware, including coreboot. Hope this helps!
You don’t even need to disconnect the battery, you just need to buy or build the usb debug cable and go through the unlock procedure using that.
If they give *you* the ability to get root, then they’ll have a hard time stopping *me* from getting root. You would dislike this very much, but you would blame them instead of me. So the easiest solution is just to deny everyone root.
So you can get into Any linux machine that has a root user??? Please prove it, break into my machine, go right ahead.
To add some nuance you missed, wrzwicky is claiming they can get into any linux machine with a root user where the root credentials are made public.
Having root access on a CCTV system such as a IP camera or DVR is a security threat. It’s a Security appliance after all.
A lot of CCTV companies have gotten into trouble for dropping into a simple bash like shell from a simple serial connection.
A lot of super cheap Hikvision clones from ebay have modified firmware that is used as a Zombie bot network.
i’d like to ruin the surprise. “That is sad, Foscam verifies the integrity with an asymmetric key, so it’s virtually impossible create a custom firmware to ship it through the official update method.” … “Finally! The black box decrypter is revealed! Honestly I don’t know if it’s useful for decrypting an updated firmware from the official support page, …”
can apparently decrypt a firmware update, but can’t encrypt a new one.
so, not the pot of gold i was hoping for. oh well.
Cryptography is a really good thing for privacy and stuff, but a major pain in the butt when doing reverse engineering… Sometimes firmware is encrypted, sometimes signed, almost all web traffic (sniffing firmware update traffic anybody?) today goes over TLS, … :-/
Hi Greg, u-boot console access is enough to replace the firmware for a custom one. The down side is you need UART wiring.
While sad for you, this is a good thing. Else a man-in-the-middle attack could update the firmware with a hostile payload.
What we did at Ultimaker, was sign our updates asymmetric, so you cannot update by normal means to custom firmware. Which prevents any MITM attack. But at the same time, there is a menu option to enable the developer console, which gives full SSH access. So people that like to customize firmware can do so.
I’m still convinced this is the best way.
I wont drop the couple of companies in it (because the feature helps me), but some that use encrypted firmware still have a legacy option to use unencrypted.
Since operations on the cameras are typically run by scripts you just need to alter the right script to spit out a decrypted firmware upgrade, alter it and then inject it back in after the encryption process.
Most cams used to have root, but often this is now blocked. However many are not, many are wide open still.
Some even allow you to run your own code on them.
It’s a playground rife for cyber security bug hunting.
Reading the original article and just saw that radare2 has been forked. Interesting times ahead, let’s see how the developpment of the fork (Rizin) and the original radare2 continue (or not). r2 is a nice tool but not easy to use and the documentation for hacking the code is mostly missing, that’s a problem with a lot of FLOSS and quite a pain.
Great project, I did a similar one during lock down last year, although my skills in reverse engineering software are not good, I managed to simply find the on board http/cgi executable that creates a new user and run this to make an admin password. check it out here (sorry for the long video) https://www.youtube.com/watch?v=xlwkrVfg7dE