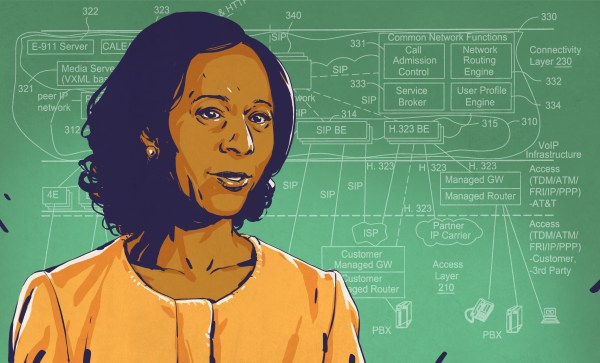
If you’ve ever used FaceTime, Skype, own a Magic Jack, or have donated money after a disaster by sending a text message, then you have Marian Croak to thank. Her leadership and forward thinking changed how Ma Bell used its reach and made all of these things possible.
Marian Croak is a soft-spoken woman and a self-described non-talker, but her actions spoke loudly in support of Internet Protocol (IP) as the future of communication. Humans are always looking for the next best communication medium, the fastest path to understanding each other clearly. We are still making phone calls today, but voice has been joined by text and video as the next best thing to being there. All of it is riding on a versatile network strongly rooted in Marian’s work.