Back when we started The Hackaday Prize, security, big brother, and the NSA were making headlines every day. Since that time, there has been enough bread and circuses in the news to wipe the consequences of these leaks out of the public consciousness, but work is still being done by hackers and tinkerers the world over to give you the tools to protect your data.
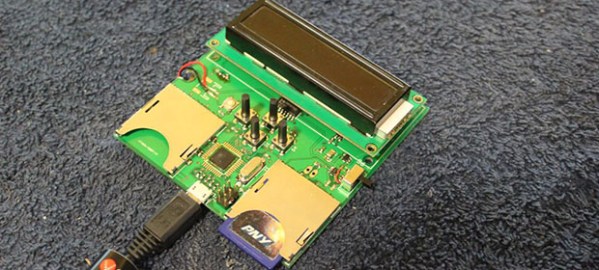
NSA Away is one of these tools. The first part of the project is a standalone key generator that writes the same random bits to a pair of SD cards simultaneously. With their random number generator, this is perfect encryption. The only way to crack the one time pad the team is using for encryption is to 1) use parts of the pad more than once, 2) have a terrible RNG, or 3) do something really stupid like sell the one time pad in a store.
The other part of the build is an Android-based encryption device with a camera, keyboard, SD card reader, and a USB port. This device reads the ‘OTP SD cards’ and reads data with the camera using OCR and decrypts it on the screen. Provided the OTP doesn’t fall into the wrong hands, this is a perfectly secure way to transmit data to anyone.
As far as progress goes, the members of the team have a fully functional pad generator, writing random data to SD cards. This device can also output random bits to a computer as a USB HID device, should you want to transmit your pad over unsecured mediums.
It’s an impressive bit of work, especially in the RNG department. The team is using eight avalanche noise generators in the circuit description. This part of the build isn’t quite working yet, but that’s really not needed for a proof of concept.
 The project featured in this post is a quarterfinalist in The Hackaday Prize.
The project featured in this post is a quarterfinalist in The Hackaday Prize.