There’s a section of our community who concern themselves with the technological aspects of preparing for an uncertain future, and for them a significant proportion of effort goes in to communication. This has always included amateur radio, but in more recent years it has been extended to LoRa. To that end, [Bertrand Selva] has created a LoRa communicator, one which uses a Pi Pico, and delivers secure messaging.
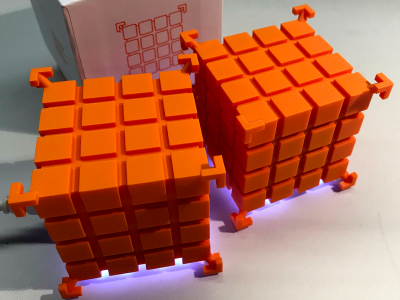
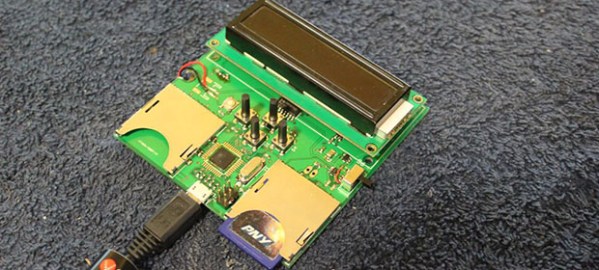
The hardware is a rather-nice looking 3D printed case with a color screen and a USB A port for a keyboard, but perhaps the way it works is more interesting. It takes a one-time pad approach to encryption, using a key the same length as the message. This means that an intercepted message is in effect undecryptable without the key, but we are curious about the keys themselves.
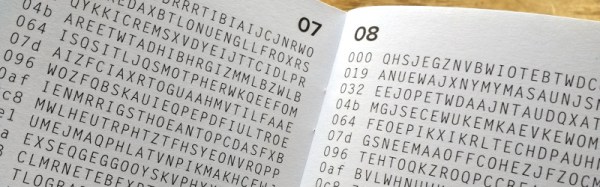
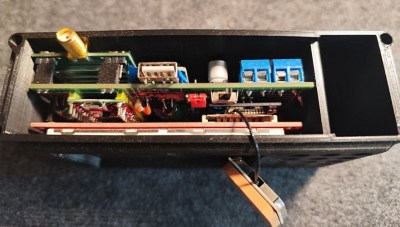 They’re a generated list of keys stored on an SD card with a copy present in each terminal on a particular net of devices, and each key is time-specific to a GPS derived time. Old keys are destroyed, but we’re interested in how the keys are generated as well as how such a system could be made to survive the loss of one of those SD cards. We’re guessing that just as when a Cold War spy had his one-time pad captured, that would mean game over for the security.
They’re a generated list of keys stored on an SD card with a copy present in each terminal on a particular net of devices, and each key is time-specific to a GPS derived time. Old keys are destroyed, but we’re interested in how the keys are generated as well as how such a system could be made to survive the loss of one of those SD cards. We’re guessing that just as when a Cold War spy had his one-time pad captured, that would mean game over for the security.
So if Meshtastic isn’t quite the thing for you then it’s possible that this could be an alternative. As an aside we’re interested to note that it’s using a 433 MHz LoRa module, revealing the different frequency preferences that exist between enthusiasts in different countries.
Continue reading “As The World Burns, At Least You’ll Have Secure Messaging”



 The project featured in this post is
The project featured in this post is