The first music played on personal computers didn’t come out of fancy audio cards, or even a DAC. the first audio system in a personal computer was simply holding an AM radio up to the case and blinking address pins furiously. This worked wonderfully for homebrew computers where EMC compliance hadn’t even become an afterthought, but the technique still works today. [Chris] is playing music on the radio by sending bits over the system bus without using any wires at all.
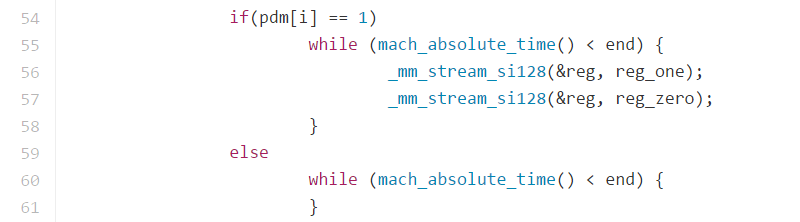
[Chris]’ code is based on the earlier work of [fulldecent], and works pretty much the same. To play a sound over the radio, the code simply writes to a location in memory when the waveform should be high, and doesn’t when the waveform is low.
Of course the ability to exfiltrate information over an airgap has a few more nefarious purposes, but [Chris] also has another way of doing just that which is undefeatable by a TEMPEST shielded computer. He can send one bit at a time by opening and closing a CD-ROM drive, capturing these bits with a webcam. Is it useful? It’s hard to imagine how this setup could ever capture any valuable data, but it is a proof of concept.















CD drive pressing reset on the neighbour system story: http://thedailywtf.com/articles/ITAPPMONROBOT
I’ve seen some pictures of such a solution somewhen but I cannot find them again…
:-(
I actually just felt bad for a computer.
Cool story man.
Now how many cd-drives could a system operate simultaneously?
Imagine 16 trays all ‘sending data’. :D
https://www.youtube.com/watch?v=bYcF_xX2DE8
Would it be much quicker just to flash the access light?
If you have a webcam pointing the computer you can use the screen, I believe.
Yes you can modulate the LCD brightness levels small but recordable amounts without the user noticing. There are many ways of leaking data out of a PC.
I have a script that will send the date and time out of my speakers in an ultrasound based code so that if I am recording a phone conversation the recording ends up with a recoverable time stamp hidden in it without the other party noticing anything.
Would you mind sharing that?
Who are you?
I’m not going to give scripts to kiddies, but the methods are well documented.
On Covert Acoustical Mesh Networks in Air.
https://arxiv.org/pdf/1406.1213.pdf
(Why did I wait to post that link? I was busy watching somebody digging hole LOL.)
Dan – Good article… I kinda’ knew I was re-inventing the wheel. Guilty as charged.
You are charged with being a bullshit artist who has actually done nothing. I wonder how many of your other posts on HAD take the same form?
Specifics please!
Evidently your PC, laptop, MAC, etc, all emit data in the cellular phone bandwidth. This did not escape the notice of Israelis at Ben Gurion Univ in the Negeb. They call the method GSMem.
I can see the CD Rom door gambit as useful to an operative who you cant talk to by radio for whatever reason. Explain that if any CD door opens on it’s own in the target room on any PC – bug out now! Company’s coming!
Also LCD exploit is good too. You can just open a browser screen and send a band of HTML tags of any size or color you want. Make sure you have a black background and point a webcam at it, and you have an air-gap exploit. Set up a JavaScript program that looks at a HTML you copied and pasted target text data into, of any text size. Turn on your webcam on your smartphone, click submit and the data is transferred to your video recorder on your phone for data extraction in you HQ-lab later. If you are a fast typist you can code this on scene without fooling with thumb drives, floppies, or any media insertion. The code is wicked simple too.The typing would be relatively silent if you brought a USB soft-keyboard rolled up in your rut-sack. The preamble would be a series of synch pulses then the host browser starts sending tags much like Morse Code or some Baudot configuration. If speed is required you’d have to evolve the code up to something similar to RTTY.
And no, you just can’t video the words you copy and pasted because text is hard to see in videos, and the data may scroll down a long way. It would be problematic to build an auto-scroller when the text is hard to resolve already. Changing it to an air-gap transmission code is much more efficient and increasing font size just slows down the process.Also you can insert a BOSS-KEY to pause the process when someone walks in on you and display a benign screen (i.e. Google search screen – return with back button). But you’d have to hide your roll-up keyboard…
Or maybe you could use a Arduino to store the desired code and send typing commands to the keyboard USB port. Some high-security PC’s won’t let you insert ANY media, nor go out to any unapproved websites (if any Internet access). The files on the Intranet or that PC are the only access you may have (it could be a thin-client too). The keyboard is their weak link.Typing and saving a HTML-Javascript locally on a PC is usually not forbidden. You can do it with NOTEPAD and use a PORTABLE browser on a thumb drive – if USB is allowed. Portable browser circumvent the company’s IT security features regarding web browsers (no local history kept).
Darn it! all my HTML tags where ignored because I use the greater than and lower than carets. In the 1st paragraph I was talking about the (HR) HTML tag (or horizontal line). Then later I was talking about the (TEXTAREA) tag which is the free-form field box.
<Damn>
Yes would work as it’s not a reserved HTML TAG. I should have used (code) tag think. But I’ve noticed it can’t handle HTML tags but only JavaScript or other codes. Also it’s not a good idea to include new lines with (code) either.
The TRS-80 did have a Assembler SDK but it was expensive back then. You must have been one of the cool kids. Most people only new BASIC and thought that knowing POKES and PEEKS was cool. It kinda’ was. I loved the COCO which I think was a 6502 µProc. You could easily do real world interfacing with it’s mouse port, cassette, and printer ports.
˂DAMN˃ – oh I see how you did that! Cool!
Or, you just capture the picture with the EMF given off by the screen’s drawing. Feasible on CRTs, and supposedly on LCDs just as much. At that point, just start blinking the bottom row of pixels on an off. As for typing all this out, one wonders if you could do it in bash or possibly even in MS batch.
Damn. I didn’t think this was still possible. It does make me wonder though, on what modern computers would this work? Would it work better on a plastic laptop than a desktop? How about an industrial ruggedized computer, one which is sealed inside a finned metal box? Just how well shielded could you get, if you say, stuck an RPi in a copper/lead box, and fed everything through (except power) over fiber? (anyone want to try using an endoscope to control their computer? It’s like one of those “let’s XP on a camera viewfinder” hacks) Would the move to terahertz photonic (not ‘electronic’) computers eventually eliminate this, once and for all?
Now I’m going to have to go wrap my computer in tinfoil……
Yes but the end-user still needs to see the display to do their work effectively. Some demand TWO monitors!. So there’s no way around this unless everyone wears a head-wear display. That would get many OSHA complaints in USA work place. Most factories, offices, etc. are going to stick with what is easy and the employees are happy. Nothing worse than a disgruntled employee.
So my idea above IS using the pixel method you mention. However, the line stretches all the way across the screen horizontally. You can make the HTML (HL) tag thick or thin. You can choose any color you want. The best background/foreground colors that some agencies like is NAVY BLUE background screen with a YELLOW Text. But White text on black is good too. Your Smartphone’s cameras will appreciate these color schemes too.
Yes Bash or MS BATCH would work quite well. HOWEVER, how would you get it from your thumb drive (usb flash drive) to the protected PC if they have turned off all USB ports or monitor them? An Arduino-based USB keyboard-typer comes to mind.The keyboard is NEVER turned off or how can the employee get any work done? Same applies to the mouse too.
Yes your “plastic” laptop/notebook is still vulnerable to Van Eck phreaking. Tinfoil is OK but aluminum would work too. But you must remember to ground it to a cold water pipe in the basement. cellar, or garage or your Faraday Shielding is pointless.There are other methods but they are too deep for some non-computer-savvy types.
Oh and you could defeat my method with 3M Privacy screening. That glass is DARK as heck if you are not sitting directly in front of it, no side angle viewing. Also take the polarization filter off of your laptop or LCD screen and all people walking by see is a white screen. But you have your polarized eye-glasses on and you see a normal LCD screen.
The whole point of using a commonly available scripting language is to just memorize the script and enter it without needing any additional software.
+1
My point exactly!
But first you have to install the scripting language…
I think a practical black-hat, in this case, would either need to know DEBUG, or be able to type raw code into text documents, then run those. People have done that before, machine code limiting the opcodes they use to those also in the ASCII printable region. Rename the .txt to .exe (or whatever) and run it as-is. Even if just to bootstrap something a bit more useful.
JavaScript and VBScript are pretty much default scripting languages in most (if not all) browsers. And you could bring your own PORTABLE BROWSER on a thumb drive if the target PC allowed that. However, I tried writing the code for an air-gap LCD exploit. It works but I realized it would be a bit much for a neophyte to memorize. You’d have to be a master-coder or advanced to type this on the fly quickly from memory. It is several lines of code not just a small snippet of code.
My point about fiber optics was when everything moves to interfacing over fiber optic, all it takes is something like a display or other peripherals which are entirely optical. Perhaps even the computers too, once the photonics people figure out how to make a repeater with good binary behavior. Then I figure emf might just drop down to nearly zero.
Til someone invents a Super-Quantum interferometer, that can put up a map of your CPU cycles from anywhere in the Universe. So far, not on the horizon.
There’s single-photon secure transmission systems, that use quantum spin and the Pauli exclusion principle (I think), to send single photons over optical fibre, in such a way as you can tell the photon hasn’t been intercepted or replaced along it’s way. For really really secure links. Something I read about years ago in New Scientist, now actually available and used, by the people that need it and can afford it.
Fiber optic systems are not immune to creative espionage. And fiber repeaters are already “a thing”. The Japanese pioneered a fiber optic splicing method system that is almost flawless. IIRC didn’t “we” do that in East Berlin back in the day?
The thing I’m talking about uses single photons on purpose. And I think it’s entanglement rather than Pauli, now I remember. Bob can tell if the photon you recieve is the one that Alice sent. Somehow. It can only be that photon, any other shows up. So you can’t intercept the photon and manipulate it, or replace with another. It’s utterly, far as we know about quantum stuff, untappable.
I think it’s to do with entanglement where measuring one photon collapses the probability state of the other. You’ll have to look it up if you want to know the proper details.
Sure normal fibres can be spliced into, you can probably do it with duct tape and a phototransistor, there’ll be a hack here about it sooner or later, but the thing I mention is special.
Yes I’m familiar with the subject matter you mention. And what you said pretty much summed up how it works. However, fibre splicing is really unforgiving when it comes to duct tape. You’d need a professional fibre splitter and some real skills in fibre alignment. The losses you’d introduce would be massive, ergo detectable. Your split could be EXACTLY located by IT security with a fibre TDR. So those American spooks in those East Berlin tunnels must have had some really sophisticated equipment and some awesome skills, The Russians never found out about it until someone told them. IIRC “they” also did this in the South Pacific to an international undersea fibre cable.
The only flaw in QE is the end-points. At either end the end-user still needs to have the data un-encrypted so he/she can read it or hear it. That’s where you’d plant your air-gap exploit even in a QE Secure System. Unless you could do like TESLA (Mr. Elon Musk) is thinking about now and implant (i.e. inject) neural mesh to you brain and have a direct link from the QE system to your brain.
Hmmm, The last three PC’s I bought did not come with a built in optical drive. And my PC’s prior to that were laptops without a mechanism to pull the tray closed. It had to be done manually by sliding it back in by hand. The CD drive technique comes at a time where obsolescence has limited it to a tool that goes unused.
It’s a pretty pathetic exfiltration system anyway, if you’ve somehow managed to get a camera into the room, you surely aren’t limited to 1 bit every 5 seconds, for the minute or so til the user notices and calls tech support to come fix his CD drive.
I remember making sounds with a TRS-80 computer in 1978 for a school fair.
I wrote it in assembly (actually machine code as I didn’t have an assembler) and it generated PWM to the cassette port and that PWM was modulated with a sine wave and the frequency of the sine wave was varied.
My science teacher connected it to an amp speaker and oscilloscope and he couldn’t get why he was seeing a sine wave from a digital output. The digital PWM was filtered off by the lack of bandwidth of the amp leaving only the lower frequency sine wave.
I don’t know if PWM was actually a thing then.
We also had 4 disk drives so I did the Larsen scanner thing with the access lights.
I played around with JavaScript codes and found a way to air-gap text data from a target PC with about 100 lines of code that uses Morse Code to send the text via the PC’s speaker at frequency ABOVE adult hearing (i.e. 15 to 20Khz). You would record the high-pitched audio on your Smartphone or MPEG recorder. No average adult in the room could hear it. And kids (who can hear it) probably won’t be in an office normally, but probably wouldn’t even care about the mosquito-like sound. The JS code would automatically resize or move the screen off-screen to avoid detection. You could retrieve it with the ALT-TAB keys.
When you get back home to decode it, you run a heterodyne JavaScript WebApi sound generator that mixes with recording to produce a lower hearable Morse Code to play into you HAM CW decoder (i.e. Fldigi or CWGet). Or you could use Audacity to lower the pitch and increase the tempo, and still play it to the CW decoders.
You can use the same thing with a HTML5 (canvas) tag in where you can change the brightness property of a image on the screen in step with Morse Code. Or just toggle in the browser the body.bgcolor=color JS command to toggle between two very close colors like Blue and Navy Blue, Gray and Light Gray, etc. The subtle difference may be undetectable by casual viewers..
No you didn’t.
Dan – I did not write it, another coder did. I played with it and it is awesome to at least me. I couldn’t hear NOTHING but my Audacity recording was showing Morse Code pulses! So I reduced playback speed and pitch went down. I increased tempo and the original Morse Code speed was achieved. I’m trying to cobble together a tone decoder in JavaScript but the codes from others keep locking up my browser. So I need to reverse-engineer it some more. Anyone can help out if they like. I supply the code but I’m like you about that guy that asked you for display-brightness and ultrasound code. Like who the heck is he and what will he use it for? Good question Dan! I got a cryptic kudos message on one of my innocent .IO’s from IRAN! Now he deleted his PM to me. Suspicious as hell… Don’t want to help them with good ideas!
@Mark – Thanks! It does work. I played “The Quick Brown Fox Jumped Over the Lazy Moon.” to my Ham Radio CW decoder from loudspeaker to internal microphone and SHAZAAM! it appeared flawlessly. However, the decoder will only work up to 3,000 Hz not 20,000 Hz. So that sucks. Anybody have any ideas? I’m thinking hetrodyning or some sort of audio downconverter.
Yeah, we know you can’t code.
You could show us a screen shot of the sonogram view from audacity, and keep in mind that there are people on HAD who can do this sort of stuff and know what sort of additional artefacts the sonogram should show. :-)
http://4.bp.blogspot.com/-zV9wE5LHvhc/T5XC4iZ38-I/AAAAAAAAAA0/NgRooldcdK4/s1600/interrogation.png
I like that Victor Mature and Marlon Brando…
No most people at HaD know I’m pretty good with JavaScript (and a few other script languages), however, they know I’m not an EXTREME advanced coder but I can keep up with the pack. Yes I can supply a screenshot if you like. I have to setup it all up again. However, it’s not rocket science what I did. I just lifted someone elses code and made my own revisions. It makes sense that the new HTML5 WebKitAPI can generate a solid tone (not .wav or .mp3) for however long you want, and it can exceed 24,000 hz.But can our PC speaker handle that? Evidently the piezo speakers can. The internal mics in our PC’s can detect upwards of 20,000 Hz (or better).
Your story is drifting….
BTW people who do actually know what they are doing can leak any data, even binary files.
Looking forward to the sonogram, I hope you don’t mind that it can also be used to profile your gear, and the environment it is in…. Yes, depending on conditions, even the size of the room you are in.
Here you go Dan. It’s a 20KHz Morse Code through my PC speaker to it’s microphone. Audacity recording. There is background news from the TV in the room but you can see some of the pulses in the beginning. Couldn’t show entire stream as it was too long. Please note I could hear NOTHING while recording!
http://oi66.tinypic.com/30db1ae.jpg
It would seem that you don’t even know what a sonogram display is.
Drifting? How so? Are you having a go at me mate? :-)
http://mrsngai.edublogs.org/files/2014/09/Digging-Hole001-2b3x5mi.jpg
Ummmm…. a sonogram is a medical thing I think. The Audacity screenshot I supplied is kinda’ sorta’ the same thing. It shows the wave form. Isn’t that what you asked or?
define:sonagram
1. a graph representing a sound, showing the distribution of energy at different frequencies.
2. a visual image produced from an ultrasound examination.
Mahahahaa, busted, you have NFI. Change your nick to speakswithass.
Methinks you’re trying to start a row like the way you do with Greenaum. Sorry mate, not going to get myself in a twitter with you… I’m just going to humor you. I’ll bet you voted for BREXIT too. (jus’ having a go at you mate! LOL)
No, and no, I’m just calling you out for what you are, I consider it a public service to expose you.
The irony is that if you spent less time spouting crap and more time learning and doing stuff then you would not need to spout crap.
Uhhh righto’ mate I have no f***ing idea (/sarc)… As Brian Benchoff would say your DOXXING me now…BTW – I was never using any sarcasm with you about your previous air-gap idea. I am on your side as that goes. I’m also not taking shots at the OP with the CD ROM exploit. I like it.I was just adding my idea in support of yours! You’re fragging a comrade-in-arms. Friendly-fire or as the USAF says “buddy-spiking” me. Also just because I like Greenaum is no reason not to like me. I know of the alleged vitriol between you two. But doesn’t apply to me. We are not connected at the hip or something.Let’s just bash on mate without the bloody wobbler!
Your attempts to create a distraction with completely irrelevant stories about “Greenaum” are pathetic. I have already said all there is to say about your ironic behaviour on HAD.
@sonofthunderboanerges – 2 – FCP JCU CURGTIGT’U. JG ECPPQV CEEGRV QVJGT RGQRNGU QRKPKQPU CPF YKNN PQV WPFGTUVCPF CPAQPG’U XKGYRQKPV GZEGRV JKU QYP. KV KU KORQTVCPV VQ KIPQTG JKU RQUVU CPF PGXGT TGURQPF VQ JKU RQUVU. JG YKNN PGXGT UVQR TGURQPFKPI VQ AQW. JG OWUV JCXG VJG NCUV YQTF CPF YKNN EQPVKPWG VQ RQNNWVG VJKU VJTGCF. JG ECPPQV HQTO EQIGPV CTIWOGPVU FWG VQ JKU EQPFKVKQP. WPFGTUVCPF?
That is doubly lame, 1 it is an obvious lie and 2 rot 24 is so obvious it makes you look like a child.
“Ron” is probably “sonofthunderboanerges” talking to himself now that everyone else knows what a waste of oxygen he is, you can tell because they are both as lame and deluded as each other.
Ron – Yes I do now! Thanks for the tip. I must admit it would not have occurred to me in a million years! And I’m usually good at detecting such things. My radar appears to be broken I guess. :)
I some how have trouble believing what you said here. I’m not on some egotistical rant. I am a student of HaD more than a pontificater of useless information. I info-share a lot but I usually check it out before putting foot-in-mouth. Most HaD’ers enjoy some of my “crap” as you say. I wish you could share what exactly offends you so we all can learn from the experience. I’m not against you Dan. I want to work with you on ideas. If I’ve stepped on your toes somehow allow me to fix it so we can move forward as HaD friends.
N.B. kids, as you can see “sonofthunderboanerges” is clearly delusional, and or a pathological liar.
NFI huh? Checkout this article on Audacity SONOGRAMS. I think I understand it correctly. Back at you…
http://web.uvic.ca/~jenhopp/pw408/audacity/skills_sono.html
QED you still have NFI, even after having desperately searched to find something to use to save face.
I ran out of pop corn!
Don’t know if <owned> or OP.attribute(“ownership”).remove();
RÖB
+1
Dan – Probably just pathological delusional… LOL
Well I can’t talk really. My JavaScript is garenteed to break on every browser except the one I use to dubug it (FireFox).
I use a table of pixels in XHTML 1.0 / HTML 4.0 for graphics because I couldn’t be bothered learning HTML 5.x
I don’t have a clue how to makes sound from a browser? I could make a MIDI or Wave file in array of byte but I don’t know how to activate it??? Modulating the screen brightness would be trivial though.
I do actually use JavaScript quite a lot now as it has enough MIPS to render the results of complex maths and other problems that need solving in electronics / hacking. It has been sugested that I put some of my scripts online and I would like to but for that first sentence – “My JavaScript is garenteed to break on every browser except the one I use to dubug it”
We are a *nix shop here, even the kids, so scripts are for inventing, then the slow parts are converted to C code so the shell script can pipe data through it like any other utility in /bin I have all sorts of interesting, but useless to most people, code, why would anyone else care what the levenshtein distance between consecutive words in /usr/share/dict/words are? I could share that code, but anything that can be misused I will not share on the understanding that if you are mature enough to use it wisely you probably already know how to do it anyway. :-)
LW LV SUHWWB FOHDU GDQ PXVW DOZDBV KDYH WKH ODVW ZRUG. KH FDQQRW DFFHSW RWKHU SHRSOHV RSLQLRQV DQG ZLOO QRW XQGHUVWDQG DQBRQH’V YLHZSRLQW HAFHSW KLV RZQ. LW LV LPSRUWDQW WR LJQRUH KLV SRVWV DQG QHYHU UHVSRQG WR KLV SRVWV. KH ZLOO QHYHU VWRS UHVSRQGLQJ WR BRX. KH PXVW KDYH WKH ODVW ZRUG DQG ZLOO FRQWLQXH WR SROOXWH WKLV WKUHDG. KH FDQQRW IRUP FRJHQW DUJXPHQWV GXH WR KLV FRQGLWLRQ. XQGHUVWDQG?
That got tired hours ago, rot(n) is something lame.
Hs hr oqdssx bkdzq xnt zqd nardrrdc vhsg rnldancx zmc bzmmns dudm itrshex xntq adgzuhntq, zmc sgzs hr bqddox, lntsg aqdzsgdq kdudk bqddox.
Xlex asyph fi gviitc mj xlex’w alex mx aew.
PurpleTurdBracket – What behavior do you specifically refer to? You sound so much like Dan. Almost mirror-image.
Ted – Agreed…
Because that is who’s words I was quoting, you silly turd.
That’s a great idea. The speaker in PC’s are usually piezo, so they can easily produce frequencies outside the human hearing range.
Thanks Mark…
Purple monkey dishwasher.
Now wait a minute! the “other” guy has a legitimate reason for being a anti-social dick. What are you talking about? No just ask Brian Benchoff (the OP) if Ron and I are the same person. He does that if asked nicely. “waste of oxygen” “lame”, “delusional”? Why not share with us SPECIFICALLY how that applies to me so the effort to do a “public service” is achieved. Hmmmm… I wonder if your IP address matches another guy here… Your mendacious vitriol is telling! Don’t worry I wouldn’t dream of outting you. Just not my style…
Calling you pathological was on the money and I almost feel sorry for you, if only I could get over my feelings of revulsion.
Or I am just some idiot that wanted to get my 2 cents in the middle of someones argument.
Yeah, that could be it, except for the evidence that everyone can see here. Now anyone can be shown this thread next time that creepy guy bullshits to somebody. Game over.
PurpleTurdBracket – “Pathological” is only an adjective. Pathological “what”? You know the UK healthcare system is much better than ours here in USA. I recommend some communication training and behavioral therapy can help you to learn to socialize more successfully. I tried here but I am not qualified. Too bad you can not articulate what your diagnosis of my personal malady specifically is. I applaud your HaD public service in exposing me for the alleged fraud you think I am. But you need to share your pain and gain strength from the sharing. If am the source of the pain then explain specifically how I am that pain. Not just nebulous generalities with no strength of knowledge. Share so I can fix my problems too. (To Others: I know this is self-flagellation on my part – no more unsecured ciphers please – it’s not apparently working.)
At the risk of being flamed – and *no* I am *NOT* buying into this conversation!
BUT … “Pathological” is actually a category in its own right and is equally valid as the sub-category you are hinting at.
In any case – I am *not* taking your (over the net / instant) diagnosis seriously.
RÖB – I understand your P.O.V. here but the adjective term “pathology” is simply a word that means “the study of the path to something”. Euphemistically the adjective PATHOLOGICAL used incorrectly by many to describe a mental condition when in fact is just a noun describing another noun such as LIAR, etc. People do the same thing with PSYCHOPATH. That does not mean a raving lunatic bent on murder. Psychopathy and sociopathy are not that at all. Try Wikipedia on that to see what they really are. It is quite revealing.
RE: Online diagnosis… That was not me. Someone else here gave me that guy’s DSM condition. I was only speaking to the condition not diagnosing as that would be an unsound thing to do. Maybe the “other guy” with the dissociative online personality condition was trying to diagnose me. That’s OK as the correct response is to humor them as they really don’t see that their comments are narcissistic and pejorative. They actually believe the ridiculous idea that they are doing a “public service”. I just like to explore the psyche of such benighted thinking. Human behavior fascinates me.
Let’s just say I do perform instant online profiling. Occupational trend on my part.
===================
Back on topic!
Does anyone know how to send a CD ROM door eject command via JavaScript? Maybe via VBScript on a ASP server? I dunno.
Just brainstormed a JavaScript audio person tracker. Using the same HTML5 WebKitAPI to send out a constant 15-16Khz tone from your wi\fe’s SmartPhone set to your website. Then with a Tone decoder API you could track her in a shopping mall like a beacon tracking system. The signal would get stronger as you get closer and weaker as you move away from her. Sometimes she could be in the next aisle and you would not even know it normally.
Here’s the code:
var context = new (window.AudioContext || window.webkitAudioContext());
var oscillator = context.createOscillator();
oscillator.frequency.value = 16000;
oscillator.connect(context.destination);
oscillator.start(0);
That last line starts the constant tone. Setting it to -1 makes it stop. It’s all new fro browsers and only works in FireFox or Chrome.
Just need to figure out the audio detection scheme. Any ideas?
aka SOTB
To All Would Be Cipher Masters! To send secret messages to one another without revealing who you are or your real email address. Here is the a little-more-complex technique better than the Caesar Cipher (which is too unsecured):
1. Go to http://enigmaco.de/enigma/enigma.html to compile a message with rolling cipher codes – even ‘you know who’ has trouble with.
2. Then ask the recipient to go throwawaymail .com and setup a temporary email address that lasts 48 hours.
3. When he sends you the throwawaymail email, you send the cipher FROM the enigma app as it breaks down rotors, modes, etc.
4. Recipient has only less than 48 hours (2 days) to go read it at the throwaway web site before it’s deleted. He will have to decode the message at the engima website.
5. But if you already know your friend’s email address then don’t bother with throwawaymail.
But all that’s for secret squirrel type stuff. If you just want to comment behind someone’s back, just the recipient needs to use throwawaymail site.
Here’s how dialog might go:
Hey dude! Go get a throwaway and reply it to me so I can send you something very interesting!
1. Once you get it in a HaD reply post, then send him the “interesting stuff” from your normal email service or sendanonymousemail .net if you’re that paranoid.
2. Recipient must remember to go back often within the 48 hour window to see your stuff.
3. Recipient must not permanently bookmark the site. What would be the point?
4. And don’t worry about target seeing it. He can’t. And he can’t spam you either as it will be gone in 2 days! All he’ll see is the throwawaymail email address in the HaD post but SO WHAT?
Good luck and make this technique viral please.
SOTB