Have you ever considered sourcing an off-brand phone from the China markets? Why, or what stopped you? The answer is data and identity. You are trusting both when you decide to use a smartphone. Let’s face it, smartphones are a personality prosthesis in our society. They know your physical location, what your interests are, the people you hang out with, and how you spend your money. The keys to the castle are shared with these devices and you shouldn’t grant that kind of trust without knowing your phone is worthy of it.
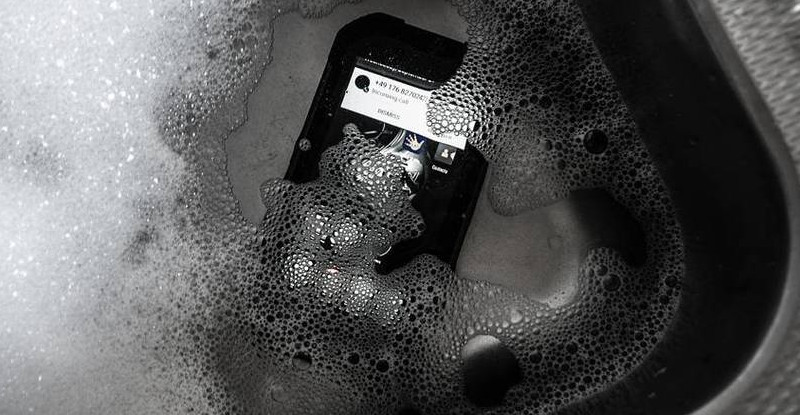
But… what if that phone has amazing features at an equally amazing price? [ijsf] bought the phone and then made it earn the proper level of trust. The model in question is a Blackview BV6000s — pictured above in a tub of soapy water proving it’s IP68 claim. This thing has flagship specs but not a flagship name so [ijsf] took [Dave Jones’] advice and took it apart instead of turning it on. In this case, it is a complete ROM dump and disassembly.
The goals was to find malware — anything that is potentially leaking data. Nothing was found, which we think is because this phone isn’t nearly shady enough. We’d expect the bargain basement models (like this $3 wonder vaporware) to be more in line. That one actually has a carrier behind it which means they plan to recoup on usage charges. But suspiciously cheap phones may be using a business model that makes it back by stealing a chunk of your identity.
Two good things come out of [ijsf’s] writeup. First, it’s a decent guide to dumping and snooping in a ROM. Second, in addition to the fruitless search for thieving apps, the annoying bloatware was removed for a cleaner ‘stock’ image.
















So… Crazy cheap phone good? Other than the LocationEM2, doesn’t seem like much anything. Though I am always afraid of radio-level bad stuff.
It depends on how you define malware: Recently rooted a Huawei phone. It had preinstalled 70Mb of Weibo stuff (Chinese facebook) It collected user data and was updated OTA despite any Weibo apps being installed as it was a phone bought from a store in Europe!!!
Cyanogenmod put an end to this and made this 80$ phone fast.
No need to put in spyware since google is so good at it already. Bazinga!
Having seen ijsf’s phone in person, and trusting his skills, I took the plunge and ordered the bv6000 (the somewhat higher-end version of the bv6000s). There is no Cyanogenmod for this phone (that I know of), but apparently, if you remove unnecessary stuff, the phone works really well.
Did you test it for stagefreight vulnerabilities?
Most Chinese smartphones still haven’t fixed them.
I’ll ask him, and I’ll check it on my phone when it is delivered. If I find something, I’ll update his blog post.
Apparently, the stagefright bug was fixed in Android 5.1. This phone runs Android 6.0, so it should not have that vulnerability.
One interesting angle you might like to think about is that a lot of the main stream phones are produced in China, as are a large number of the assemblies used in those main stream phones. It would not be beyond the wit of man to slip some spookware in at a more fundamental level. If it only dialled the mothership once a month or so, who would know?
For a widespread phone (iPhone, Samsung Galaxy, Nexus) it would be discovered very quickly. It’s like the opposite of “security by obscurity” — it’s “malware detection by ubiquity”. Every company distributing them has an interest in selling a clean and secure device, lets they be culpable when a data breach occurs.
Forcing all data traffic via a VPN that you control, that also has very strict routing and firewall rules, should significantly reduce your risk. It is a shame that mobile network connection providers do not have this as an option for all customers. i.e. They route 100% of your mobile traffic to an nominated IPv6 address that they also provide for you so that at home, or in your office, you can host a VPN server, because this would even cover the scenario where your VPN set-up on the phone was being by-passed by malicious code. This does not stop your government from monitoring your activities, it just ensure they probably need a warrant to do it effectively.
I’d also assume that to one degree or another that all closed systems are a threat, even if it is simply due to incompetence, therefore I suggest that you cultivate multiple identities and use the more throw-way ones for activities that have a higher risk of leaking information. Also consider asking yourself do you really need every aspect of your life so integrated or should you partition off some key parts of it in ways that are less technologically enabled because as so much of our society becomes “wired” those who disconnect get forgotten completely and therefore are not likely targets.
You can also make your personal data more “relational” so that without the data referred to your other data is almost meaningless to somebody without a “Rosetta stone”, a relationship diagram. How you accomplish this is beyond the scope of this comment and dependent on how you use your devices, but you should be able to understand what I am suggesting if you have ever worked with SQL databases.
The option used to be there within the GGSN Nortel and Ericsson, to have that connect to your own VPN server. Although I don’t think the GGSNs were designed to support 10K’s to 100K’s of VPNs for individuals…just for larger corporates.
“Let’s face it, smartphones are a personality prosthesis in our society. ”
This would be better as “Let’s face it, smartphones are a personality proxy in our society.”, unless like many of us your personality needs a good deal of assistance.
Use of phone in 1990
Direct link Modem or a fax or a Phone call.
Use of a phone in 2016
Takes photo of face at Obscure angle puts up some pretentious information about daily activities.
spams pointless message services on thoughts for the day.
When is world war 3 going to happen already
Nah, people are always dicks, ridiculous shit was sent around by fax, people had really inane and pointless shit to say on BBS chats by modem, and at the dawn of recorded history the Sumarians were complaining about “kids today” on clay tablets.
god damn iSlabs
Then iPapyrus was invented
On the other end of the spectrum the Neo900, an open upgrade board by the OpenMoko team for the Nokia N900 which skips the hardware forward about 4 years. Nearly all documentation available except the board design files(to slow down the assumed Chinese clone). They tried to keep everything as sandboxed as possible to prevent the black-box parts, especially the modular GSM/3-4G radio from reading, executing, or injecting code into the OS through the normal modem-CPU-memory control tie-ins. The downside is getting prototype into production 100% in the EU while keeping the price down on what ends up being last-gen tech. OTOH I am still stuck with a pre-Elop/MSFT Linux Nokia N900 and nothing else that I can see on the horizon to replace it as my everyday mobile computing device and communicator.
>keeping the price down
At what they estimate at over $1000+… yeah, I gave up on Neo900. Anything open source and good is going to be priced out the ass because there’s no widespread demand to be able to scale up production to scale down costs (eg, Novena).
HA! I found out about the Neo900 project about a year ago while looking for things to do with my old N900. Granted it is a great project worthy of support, but the price tag ruined it completely.
I bought a Blackview Zeta last year to replace my Samsung Galaxy S2 which had developed the Wifi & BT fault. Phone always seemed a little sluggish & suspected a file manager I’d downloaded to try of installing pop-up adware on it.
Factory reset. Adware was still there.
Used Kingroot to track that down & remove it until we got Cyanogen installed on it and what do you know, it’s now a HELL of a lot faster.
I always wondered what kind of nasty stuff could be hiding in the firmware of those cheap phones.
Too bad the FCC won’t let anyone dig about in the radio code… I’d imagine that if anything is borked, it’d be the radio bits.
It has access to every bit of data going in and out, plus it’s usually the entropy source for the RNG, and with everything running on a single SoC including radio, I wouldn’t be surprised to find that the RNG is bugged…
Where did you even find a link to purchase the device? I’ve looked all over their site
New fireware for this phone has been released, it fixed some bugs