The Chronos watch from Texas Instruments is a handy little piece of hardware if placed in the right hands. If you are not familiar with the platform, it is marketed as a “wearable wireless development system that comes in a sports watch”. In plain English, it’s a wearable wireless MCU mated with a 96 segment LCD, that boasts an integrated pressure sensor and 3-axis accelerometer. It is capable of running custom firmware, which allows it to do just about anything you would like.
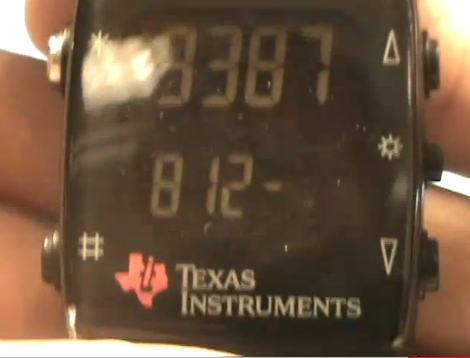
[Huan Trong] wanted to take advantage of Google’s new two-factor authentication, and decided his Chronos would make a great fob, since he would likely be wearing the watch most of the time anyhow. He put together some custom firmware that allows the watch to function as an authentication fob, providing the user with a valid Google passcode on command.
He does warn that the software is alpha code at best, stating that it doesn’t even allow the watch to keep time at the moment. We are definitely looking forward to seeing more code in the near future, keep up the great work!
Be sure to stick around to see a video of his watch in action.
[youtube=http://www.youtube.com/watch?v=MpEpaI5fURQ&w=470]















Nice work! Finally putting my chronos to do something usefull :)
Aww.. regenerating the QR code erases the application-specific passwords. Anyways, I’m going to try some other device. Perhaps a Pokemon Mini or some calculator.
“In plain English”? How is that any plainer? More specific, yes, but more plain, certainly not!
Just a side note: When you make, don’t change anything other than your secret key, otherwise I can’t be sure it will make.
The watch firmware will cycle through Time -> OTP -> Sync -> rf BSL. In the time and OTP mode it won’t display anything on the second line. Just wait for a couple of secs.
It can still keep time, but can only display the time in epoch ;-)
Ive not seen this watch before.
Ive been thinking of getting something a bit clunky and retro. And you can re-program it.
Go to get one, thanks for bringing it to my attention.
More interested in the code to generate the OTP?
The code he wrote is based on the RFC 4226 specifications and the TOTP specifications here.
http://tools.ietf.org/html/draft-mraihi-totp-timebased-06
Python based interpretation…
https://github.com/bdauvergne/python-oath/blob/master/hotp.py
Google has released the Google Authenticator code base… so their version of the code is freely available. There are also a bunch of different language versions out there.
http://code.google.com/p/google-authenticator
What a bummer.. I cannot even get the test vectors from working. Even tried downloading different sha1_hmac routine. Maybe my compiler is borked. http://tools.ietf.org/html/draft-mraihi-totp-timebased-00 should be ok right?
Every time I make an order at Farnell I always try to justify adding one of these TI watches to the shopping cart. It’s one of those cool things that you just want but can’t necessarily find a need for.
Today I thought “what the hell” and just bought one. ;o)
@DarkFader: Should be OK. I’ve got the SHA-1 routine from Ghostscript and HMAC_SHA from Google Authenticator (The GA’s SHA-1 routine is very tricky to port).
The tricky part is porting those to such a limited device and it was harder than I thought initially. Many SHA-1 implementations rely on long int, which we don’t have over there.
I have hacked together a standalone dummy OTP generator in C and can share it if that helps anyone.
I really wish TI would have given this watch a pixel matrix display. Just don’t know how to make sense of the numeric only display for a creative project.
Google uses an 80 bit secret, and I’ve managed to create code in .NET that does the trick once I decoded my Base32 secret from the website during the enrollment process. I haven’t bothered with the QRCode that they give you, which also includes the e-mail address and some other stuff I imagine. The e-mail address isn’t part of the secret, just the 10 bytes of data that they give you. I also seem to be 30 seconds slower than my cell phone, as the codes produced by my program are 1 step behind my cell phone, but they MATCH! :D I can post code somewhere or e-mail my code once I clean it up, everything’s hard coded now (which is bad).
Here is my PocketStation implementation